Crash Dump Analysis Patterns (Part 304)
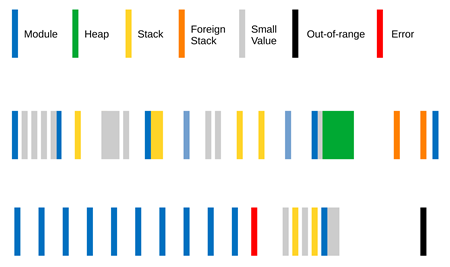
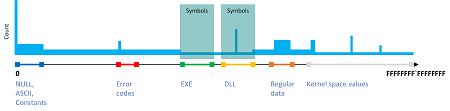
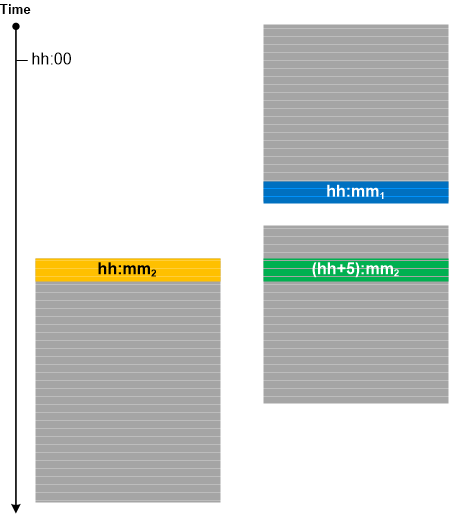
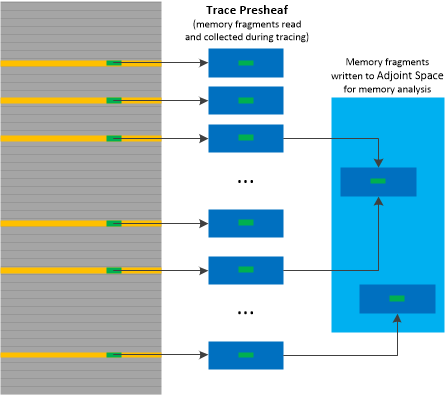
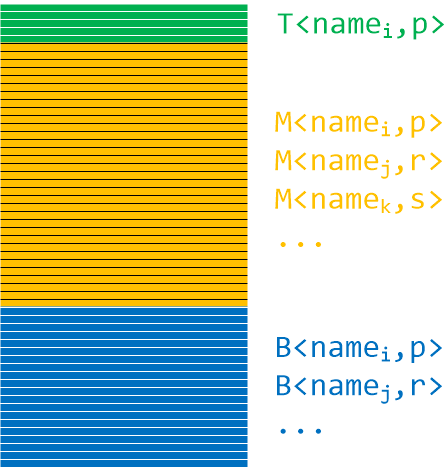
Sunday, December 7th, 2025The Latent Structure pattern addresses situations where a memory region appears raw and untyped yet shows early, incomplete signs of structural organization. Signals, such as small or pointer-like values, alignment regularities, recurring byte sequences, partial strings, or fragments that resemble fields, suggest that a real structure might exist, but cannot yet be interpreted safely or confidently. Latent Structure represents the pre-suspect stage in structural diagnostics: the point where the analyst notices potential form but must resist premature interpretation. Acting too early risks misclassifying problems and misidentifying root causes. Several forces complicate this stage: partial overwrites, coincidental alignments, ABI or version mismatches, and cognitive biases that encourage overinterpretation. This analysis pattern, therefore, emphasizes careful, hypothesis-driven exploration using techniques such as tentative structure casting, pointer-chain heuristics, checks for internal semantic coherence, software internals, and domain knowledge, all without assuming the structure’s validity. When enough evidence accumulates, a Latent Structure transitions into a Suspect Structure (subject of the next analysis pattern), where it becomes testable.
For example, we may see these fragment in Execution Residue:
00000029`e7efeb00 00001f80`0010004b
00000029`e7efeb08 0053002b`002b0033
00000029`e7efeb10 00000242`002b002b
Finally, we write the formal pattern structure card.
Intent
Detect hidden or unclear structural organization in raw memory regions that exhibit early indicators of structure-like form but whose types are not yet known.
Context
Appears in:
Execution Residue, Pointer Cone, Memory Region, and Region Strata.
Problem
A memory dump shows a region of raw bytes without explicit type information that contains hints suggesting that a structure may be present. Prematurely interpreting such memory can lead to false positives, misclassification, incorrect casting, and a chain of misleading hypotheses.
Forces
Data:
- Memory may contain partial structures
- Overwrites blur structure boundaries
- Random-looking regions may hide structured subregions
Semantics:
- Pointer-like values may be real or coincidental
- Partial strings
- Field alignments may appear regular due to chance
Modules:
- Coincidental symbols
- ABI or version mismatches
Cognitive biases:
- Insufficient domain knowledge
- Premature suspicion
Symptoms
- Structural hints in bytes
- Pointer-like values
- Strings and identity hints
- Alignment and regularity
- Recurring patterns across multiple memory locations
- Partial structure validity
- Incomplete or corrupt-like structure
Resolution Strategies
- Structure casting
- Heuristic field and pointer chain analysis
- Verification of internal semantic coherence
Resulting Context
Structure becomes Suspect and testable for validity.
Related Patterns
Hidden Artifact Patterns, Corrupt Structure, Module Hint, Falsity and Coincidence Patterns, Shared Buffer Overwrite, Value References, Small Value, Design Value, Shared Structure, and Regular Data.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -