Archive for February, 2023
Saturday, February 25th, 2023
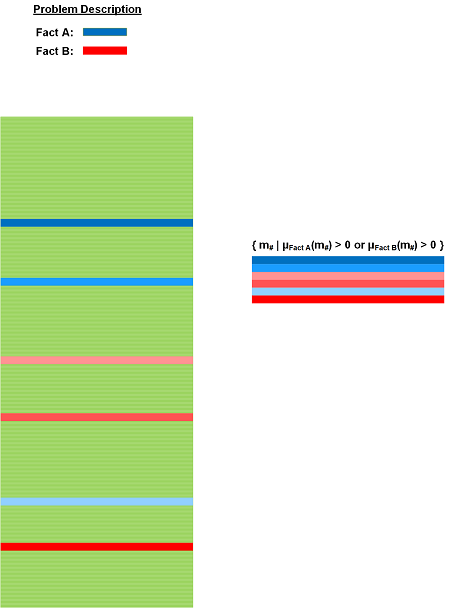
Often, we have Basic Facts but are unsure 100% if particular trace messages are relevant or not. We take the idea of Case Messages analysis pattern from fuzzy sets where we have a degree of membership function. It is illustrated in the following diagram:
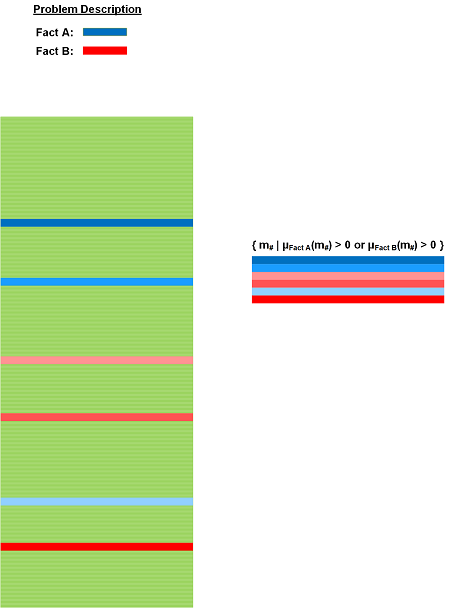
In comparison, Message Set analysis pattern is about crisp sets where the degree of membership is either 0 or 1.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Sunday, February 19th, 2023
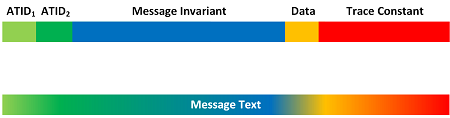
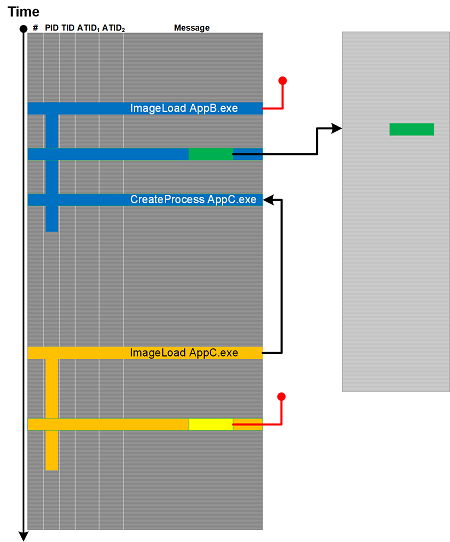
If necessary, for example, for the conversion to Text Trace, individual trace messages may need to be converted to message text form blending various message constituents like ATIDs, Message Invariants, data, and Trace Constants into some textual narrative form. We illustrate it in the following diagram:
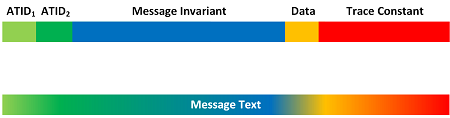
We call the resulting message text Denormalized Message. It is the reverse process than finding Features of Activity and constructing structured messages conforming to some Trace Schema.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Narratology, Software Trace Analysis, Text Analysis, Trace Analysis Patterns | Comments Off
Sunday, February 19th, 2023
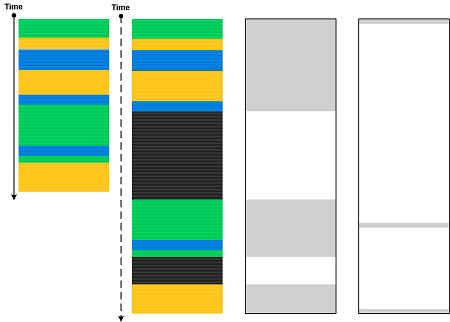
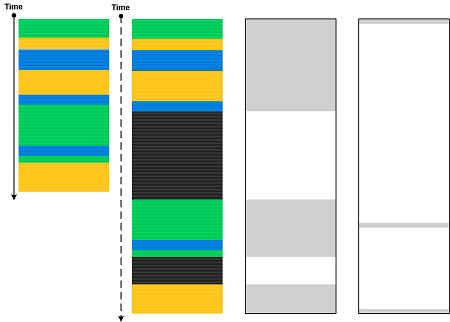
In addition to Trace Skeleton, we can insert Silent Messages, treat non-silent messages as instances of some template message, and even take Quotient Trace of them, leaving the position of final non-silent messages intact. This is similar to retraction in topology, so we name this analysis pattern Trace Retract and illustrate it in the following diagram:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Topology | Comments Off
Sunday, February 19th, 2023
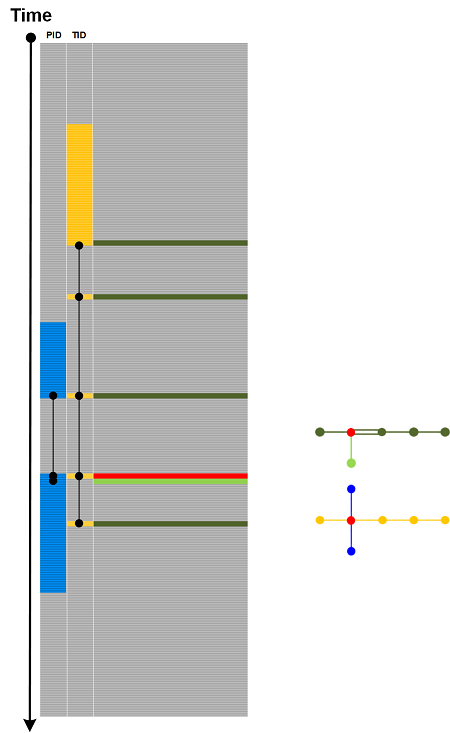
When we construct Trace Molecule, we may find that some Message Complex links from different ATIDs point to the same message and Tracemes. In such a case we have Message Bond by analogy with covalent bonds. One such example is illustrated in the following diagram:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Chemistry, Log Analysis, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Saturday, February 18th, 2023
Trace Nerve is Thread of Activity or Adjoint Thread of Activity that runs through all Activity Regions. An example is illustrated in the following diagram:
Of course, depending on trace or log, there can be several Trace Nerves. This analysis pattern was inspired by nerve complexes in topology.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Topology | Comments Off
Saturday, February 18th, 2023
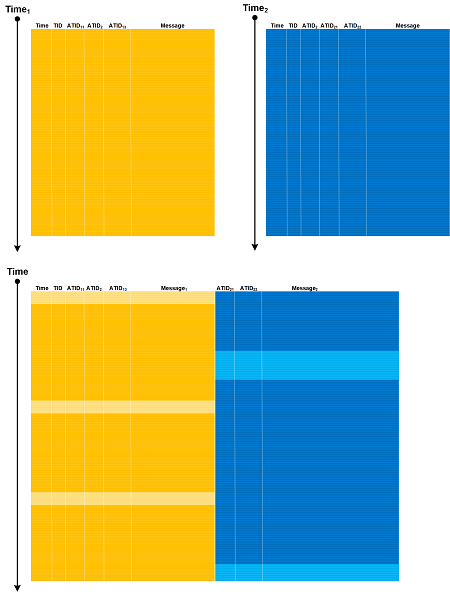
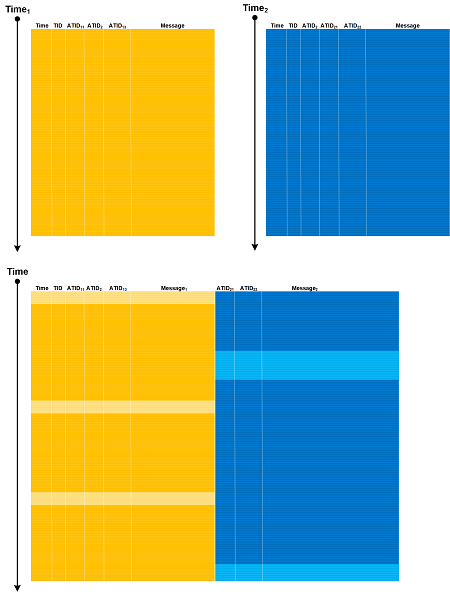
Looking at software traces and logs as 2-categories allows us to consider Whisker Traces (horizontal composition) in addition to vertical composition such as Serial Traces, Trace Mask, and Container Traces. The same ATIDs can be combined, and if there is a time mismatch, additional message copies need to be added (whiskering). The process is illustrated in the following diagram:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Friday, February 17th, 2023
Trace embedding usually happens when some external tracing or logging framework or library is used. In this case, a trace message becomes part of an outer trace message which may have its own uniform Trace Schema. In this case, Embedded Trace analysis pattern is different from Container Trace where outer Trace Schemas may be different.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Saturday, February 11th, 2023
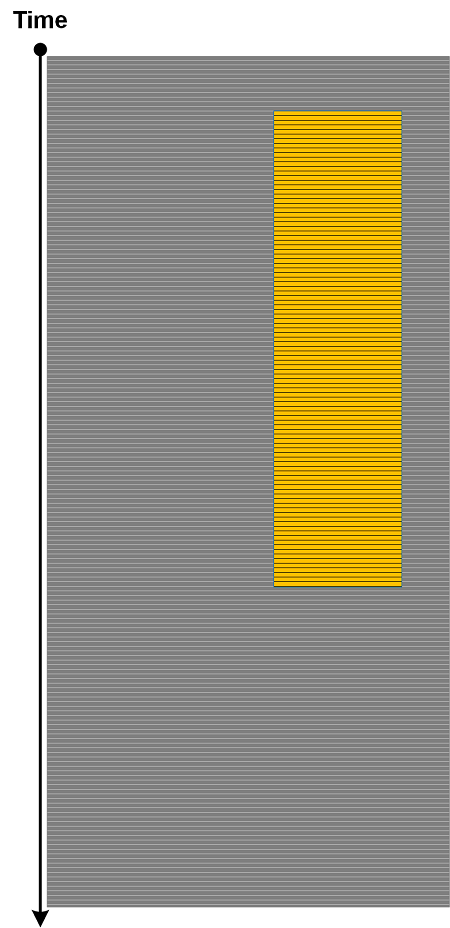
Trace Windows, the obvious analysis pattern that was always implicit, is added now due to the proliferation of stream processing nowadays. However, it captures not only horizontal windows but vertical ones, similar to subspaces if we consider messages as vectors. Both types of windows can be combined. This is illustrated in the following diagram:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Data Analysis, Data Science, Databases, Log Analysis, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Wednesday, February 8th, 2023
There’s some kind of duality between trace data and activity. For example, trace data corresponds to CoData (CoTrace, CoLog), the analysis activity. On the other hand, Regions of Activity (and various Activity-related patterns such Thread of Activity) may contain data that itself may point to some activity (not necessarily the same), CoActivity. For example, some keyboard-related message data may contain values of passwords. This analysis pattern is illustrated schematically in the following diagram:
CoActivity is different from Data Flow, where the same or modified value is passed from one message to another, not necessarily inside the same activity.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Security, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Tuesday, February 7th, 2023
For any Message Complex, we can choose the corresponding Tracemes and assign them to points. If we keep ourselves only to line segments, we call these arrangements Trace Molecules. One example is illustrated in the following diagram:
This molecular approach was inspired by semic molecules in semic analysis. On the other hand, ultimately, the whole trace is one giant molecule similar to the traces and logs as proteins metaphor. This approach differs from the earlier artificial chemistry approach to trace and log analysis where molecules are patterns.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Chemistry, Log Analysis, Semantics, Semiotics, Software Trace Analysis, Software Trace Linguistics, Trace Analysis Patterns | Comments Off
Monday, February 6th, 2023
Consider the following trace message:
object: 0x77F468AB100 ref: 2
It contains several Tracemes, the smallest units of tracing (trace meaning, by analogy with semes), corresponding to Message Invariants and their data: //object memory address//, and //reference count//. However, they are structurally higher in the semantic hierarchy when compared with sememes. Traceme is pronounced /tɹeɪˈsiːm/ and can also be interpreted as trace me.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Semantics, Semiotics, Software Trace Analysis, Software Trace Linguistics, Trace Analysis Patterns | Comments Off
Sunday, February 5th, 2023
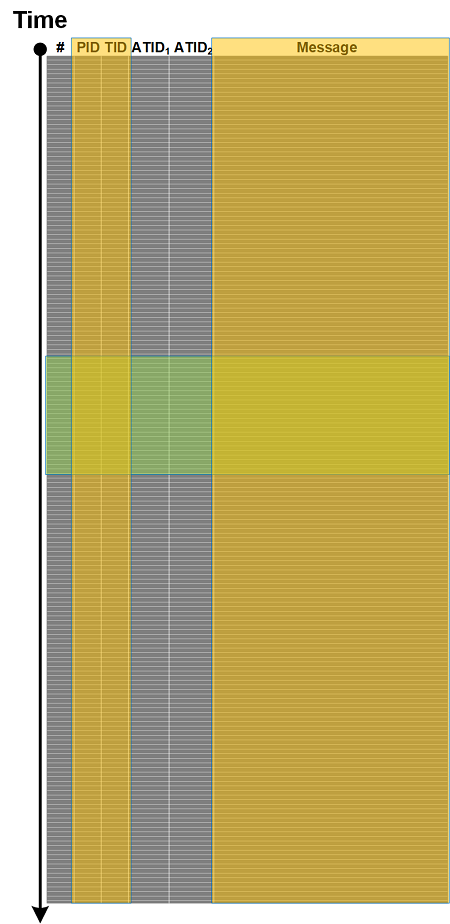
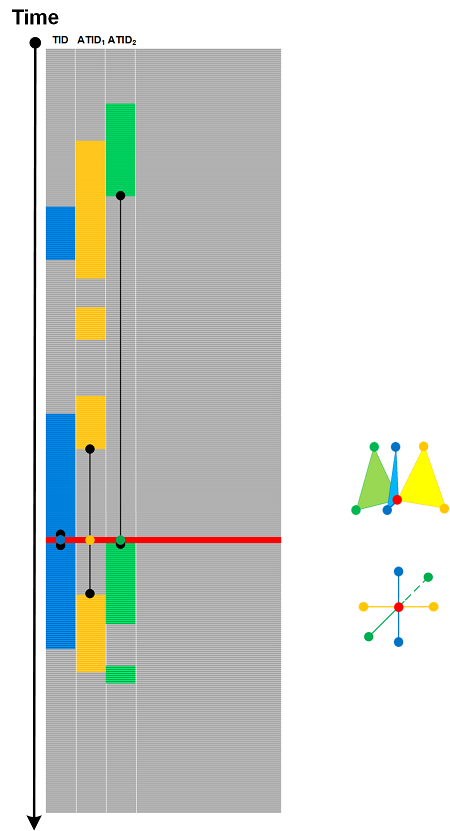
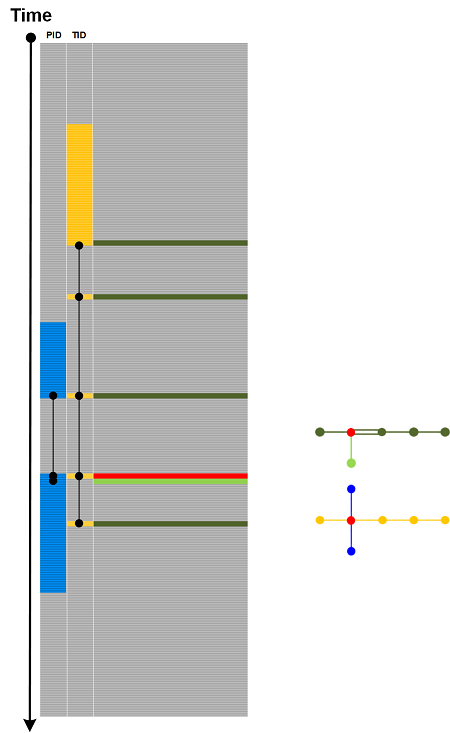
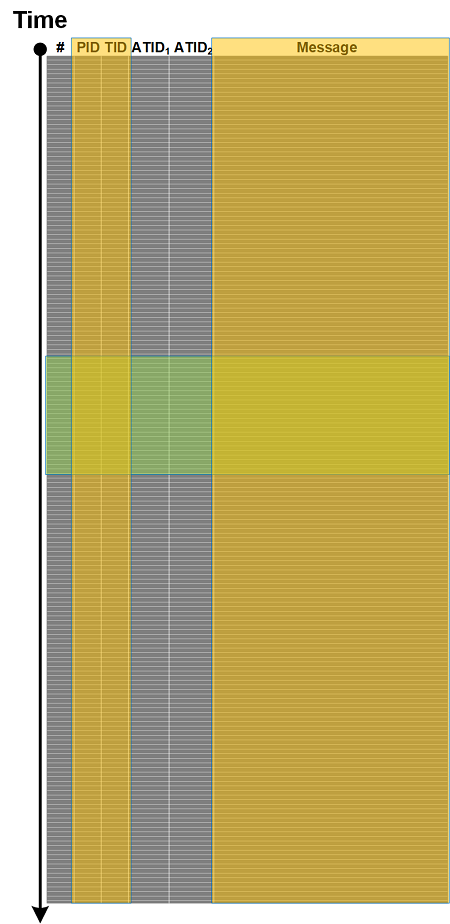
Message Complex takes inspiration from simplicial complexes. We select a message, choose TID or ATID, and connect to the nearest messages having the same TID or ATID. This procedure can be repeated for newly connected messages. Then we select another ATID and repeat the procedure. Three connected messages with the same ATID may form a triangle and may also intersect another triangle with a different ATID if they share the same message. A very simple example is illustrated in the following diagram:
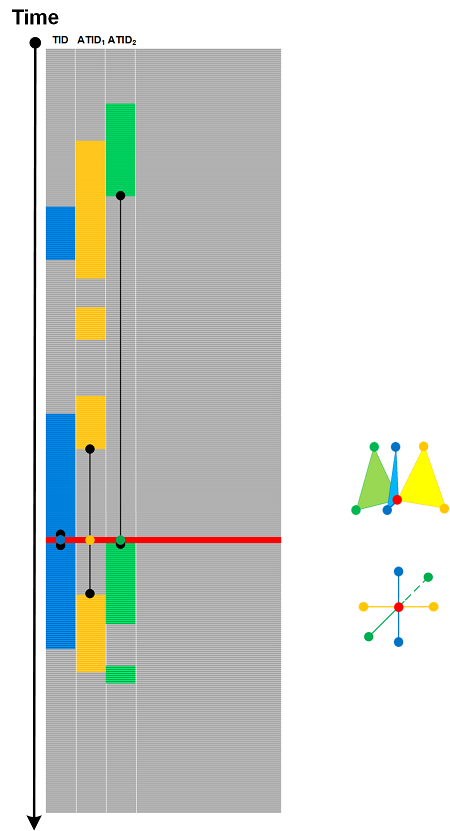
Message Complex is more structural and geometric compared to Message Context, which is just a set of surrounding messages regardless of their TID or ATID based on some relationship criteria.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Saturday, February 4th, 2023
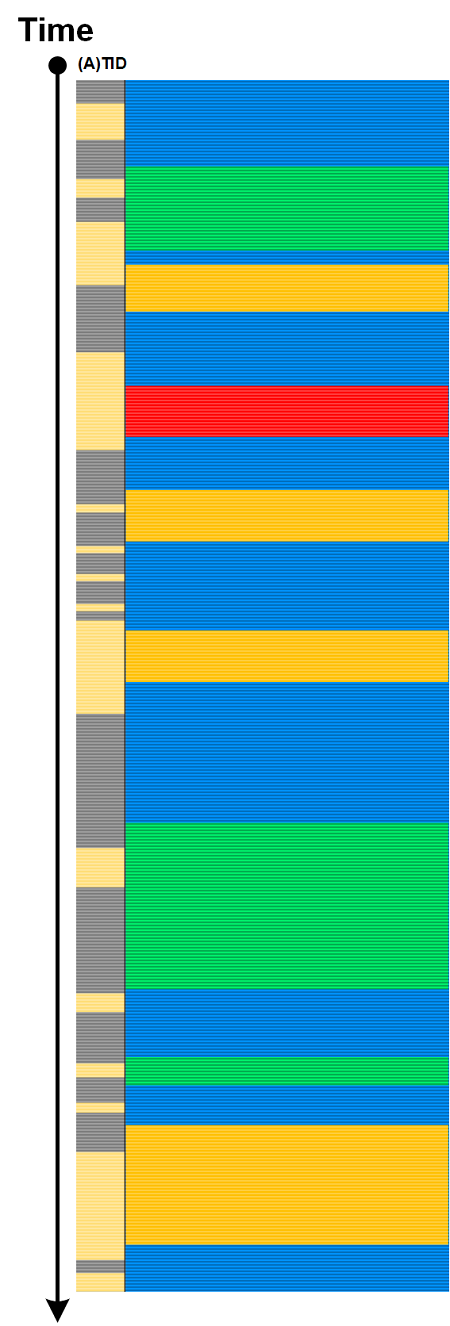
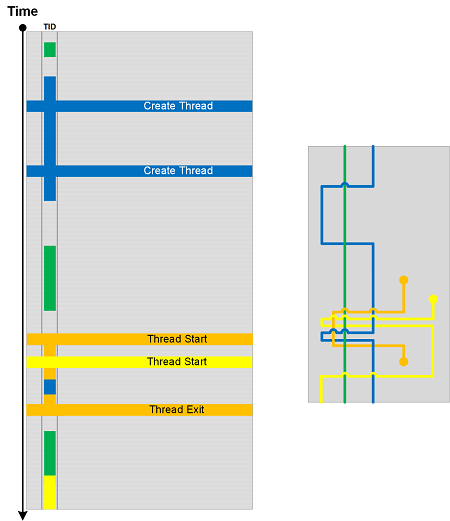
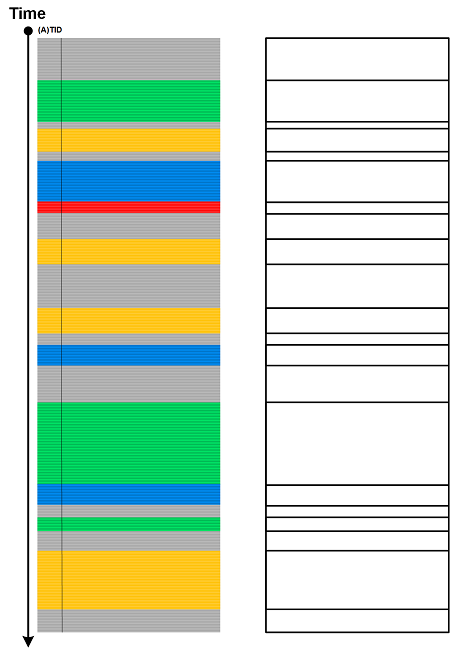
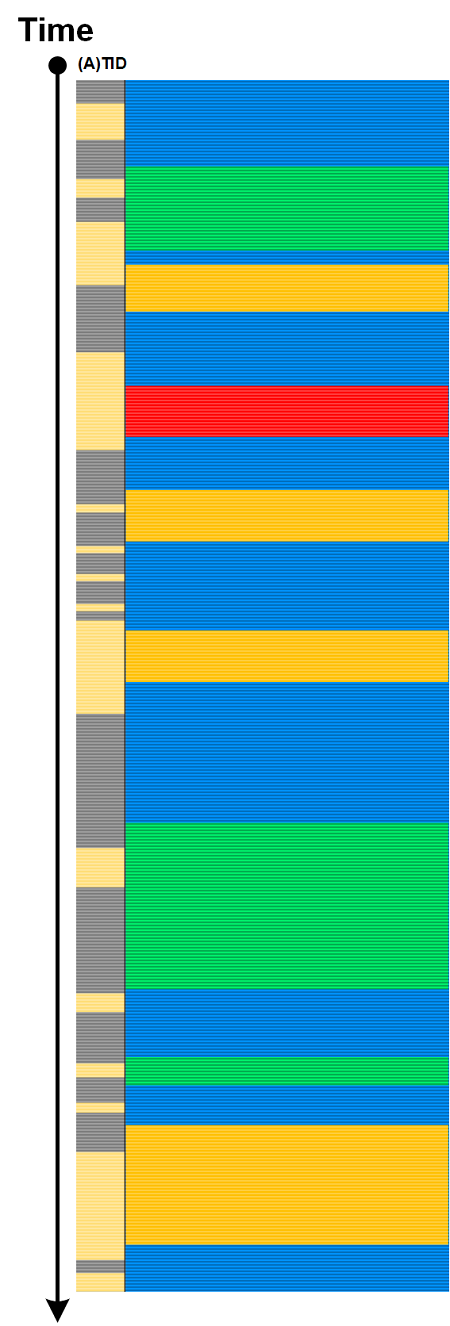
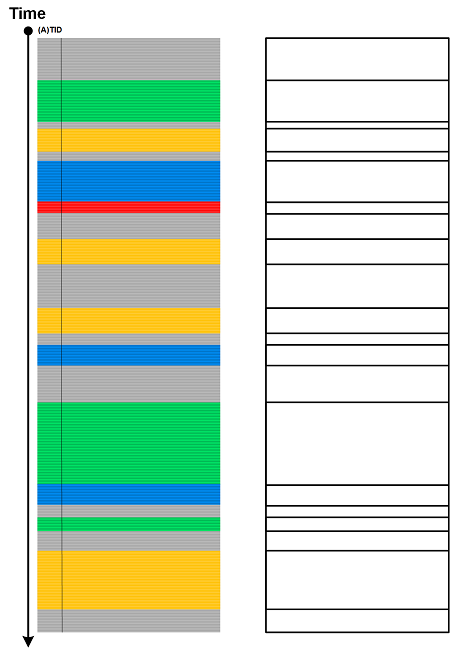
(Adjoint) Threads of Activity can be interpreted as braids (multibraiding). This braid analogy assumes that all (adjoint) threads implicitly start and end outside of the trace boundaries. However, some (adjoint) threads may start after the beginning of the tracing or end before the finishing of the tracing. Such modified braids are called braidoids. There can be several braidoids per trace based on the chosen (A)TIDs. We call this analysis pattern Trace Braidoids and one, based on TID, is illustrated in the following diagram:
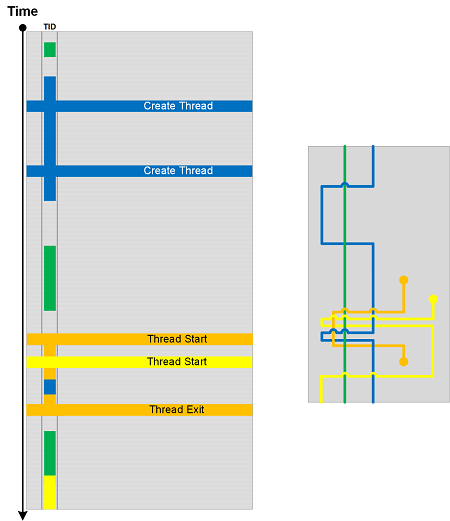
We added arc crossings when a different TID becomes current. Please also compare these crossings with other analysis patterns such as Braid Group and Braid of Activity.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Thursday, February 2nd, 2023
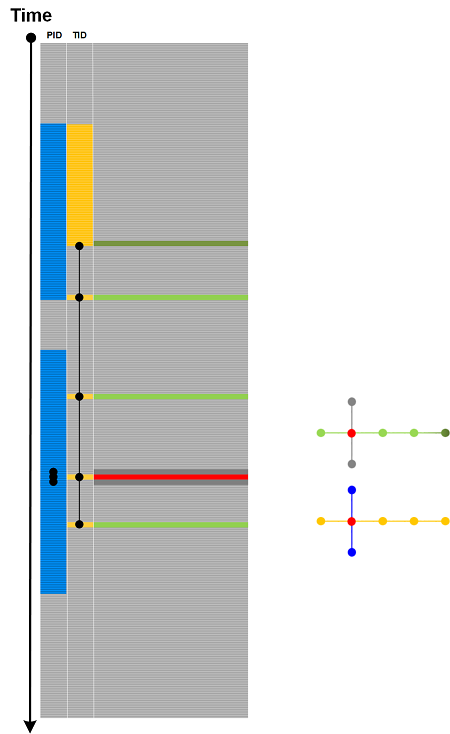
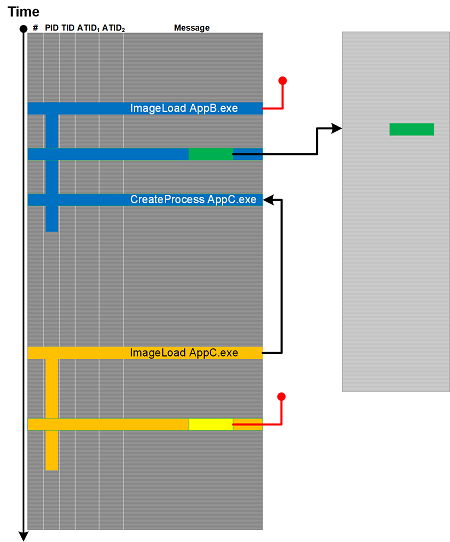
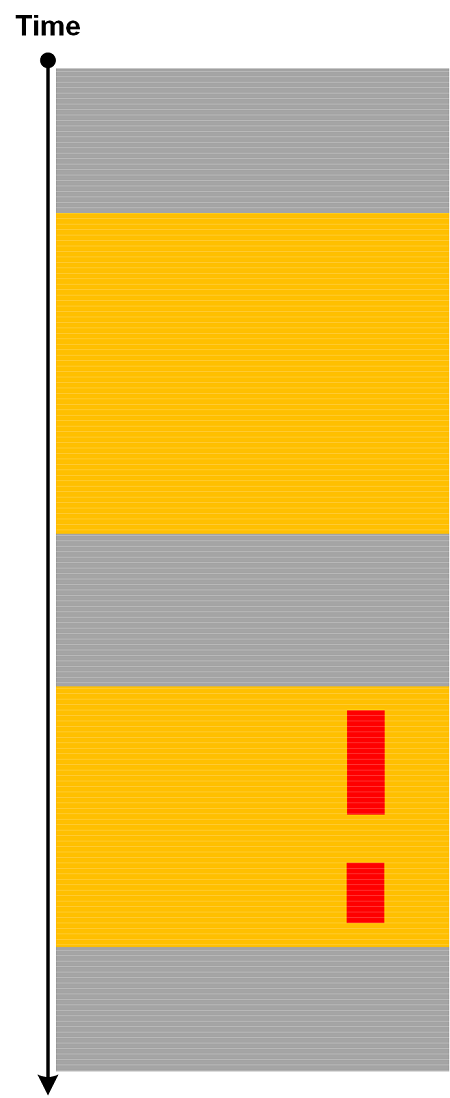
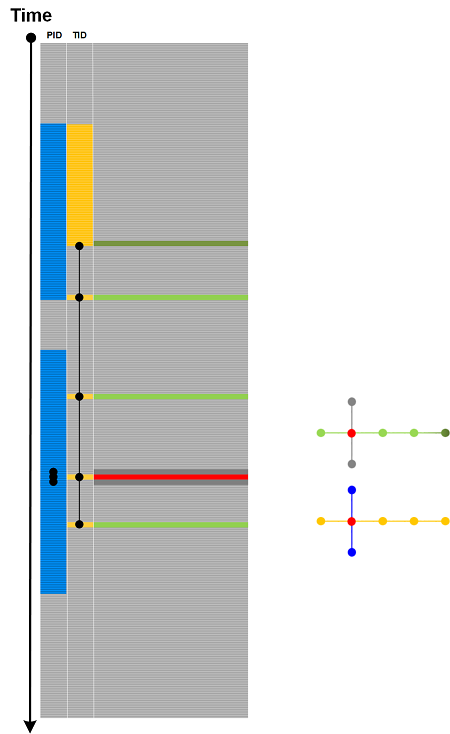
Message data may point to other messages in the same trace (see the example of Linked Messages) or in the other trace (see the Data Selector example). But similar data in other messages may not point to any other messages in the same or other, perhaps Truncated, traces and logs collected at the same time - similar to invalid pointers, for example, kernel addresses in process memory dumps or user space addresses in kernel memory dumps. We call this analysis pattern Null Reference (also notice the analogy with foreign key values in data tables where Null is not a value). Another analogy here is referential failure. This is illustrated in the following diagram adapted from Linked Messages analysis pattern diagram.
This analysis pattern is different from Missing Data where the reference is itself missing.
These Null References can be remediated by longer supplemental traces, Fiber Bundle, and Adjoint Spaces.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | Comments Off
Wednesday, February 1st, 2023
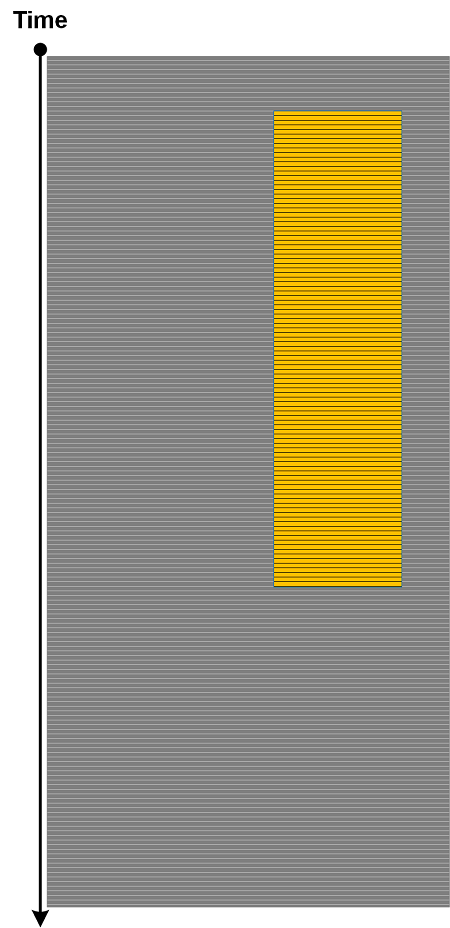
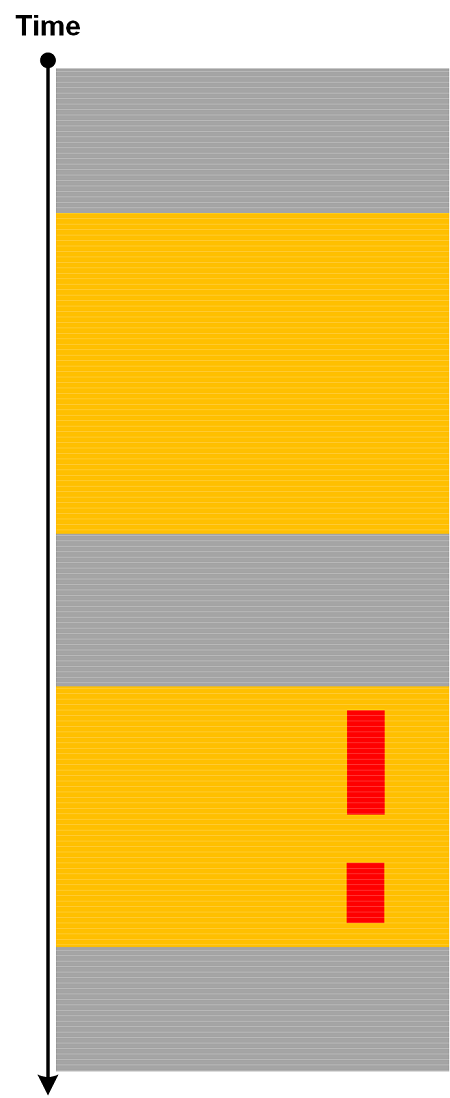
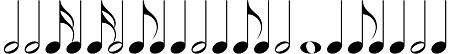
When we disregard the length of message blocks having the same attribute (ATID), we get Quotient Trace. But when we disregard the content of these message blocks (and replace each message with the same “empty” non-Silent Message) but preserve their length, we get Trace Skeleton.
Different Trace Shapes may have different Trace Skeletons but we can generate similar shapes from one skeleton.
We can also apply a music metaphor and consider it as Trace Rhythm:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | Comments Off