Archive for the ‘Computational Ghosts and Bug Hauntings’ Category
Sunday, April 18th, 2010
OpenTask to offer first 3 volumes of Memory Dump Analysis Anthology in one set:



The set is available exclusively from OpenTask e-Commerce web site starting from June. Individual volumes are also available from Amazon, Barnes & Noble and other bookstores worldwide.
Product information:
- Title: Modern Memory Dump and Software Trace Analysis: Volumes 1-3
- Author: Dmitry Vostokov
- Language: English
- Product Dimensions: 22.86 x 15.24
- Paperback: 1600 pages
- Publisher: Opentask (31 May 2010)
- ISBN-13: 978-1-906717-99-5
Information about individual volumes:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in .NET Debugging, Aesthetics of Memory Dumps, Announcements, AntiPatterns, Art, Assembly Language, Books, Bugchecks Depicted, C and C++, CDA Pattern Classification, CDF Analysis Tips and Tricks, Categorical Debugging, Certification, Citrix, Code Reading, Common Mistakes, Computational Ghosts and Bug Hauntings, Computer Science, Countefactual Debugging, Crash Analysis Report Environment (CARE), Crash Dump Analysis, Crash Dump Patterns, Crash Dumps for Dummies, Data Recovery, DebugWare Patterns, Debugging, Debugging Methodology, Debugging Slang, Deep Down C++, Dictionary of Debugging, Dr. Watson, Education and Research, Escalation Engineering, Fun with Crash Dumps, Futuristic Memory Dump Analysis, GDB for WinDbg Users, Hardware, History, Horrors of Computation, Hyper-V, Intelligent Memory Movement, Kernel Development, Laws of Troubleshooting and Debugging, Mathematics of Debugging, Memiotics (Memory Semiotics), Memoidealism, Memoretics, Memory Analysis Culture, Memory Analysis Forensics and Intelligence, Memory Auralization, Memory Dump Analysis Jobs, Memory Religion (Memorianity), Memory Space Art, Memory Space Music, Memory Systems Language, Memory Visualization, Memuonics, Minidump Analysis, Multithreading, Music for Debugging, Music of Computation, New Acronyms, New Words, Occult Debugging, Philosophy, Psi-computation, Publishing, Science of Memory Dump Analysis, Science of Software Tracing, Security, Software Architecture, Software Defect Construction, Software Engineering, Software Generalist, Software Maintenance Institute, Software Narratology, Software Technical Support, Software Trace Analysis, Software Trace Visualization, Software Tracing for Dummies, Software Victimology, Stack Trace Collection, Testing, Tools, Trace Analysis Patterns, Training and Seminars, Troubleshooting Methodology, Victimware, Virtualization, Vista, Visual Dump Analysis, WinDbg Scripts, WinDbg Tips and Tricks, WinDbg for GDB Users, Windows 7, Windows Server 2008, Windows System Administration | No Comments »
Friday, April 2nd, 2010
After this 1st of April evening spent in circus with my family I approached a PC to check my blog (seen from the window) and found a number format exception on a side bar currency conversion widget:

At first I panicked but then recalled that I already encountered some currency conversion problems with that widget. At the time of this writing, it is no long a local April Fool’s day but the problem persists.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Computational Ghosts and Bug Hauntings, Debugging | 2 Comments »
Wednesday, November 25th, 2009
Highly recommended to listen during analysis of a complete memory dump from an isolated dead system to build tension resulting in a problem resolution in 21 minutes:
Rachmaninov: Symphonic Dances & the Isle of the Dead

- Dmitry Vostokov @ DumpAnalysis.org -
Posted in Computational Ghosts and Bug Hauntings, Crash Dump Analysis, Debugging, Horrors of Computation, Music for Debugging, Occult Debugging | No Comments »
Tuesday, November 24th, 2009
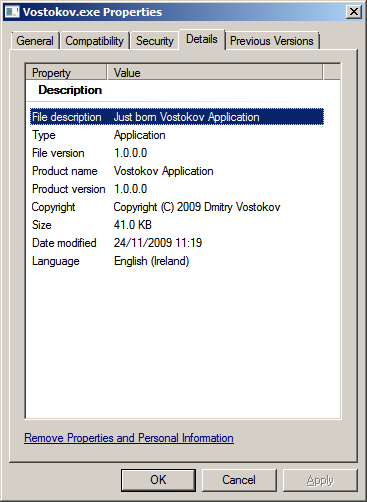
Finally you can run my moniker process (just born version doesn’t consume CPU time) and if I come across the dump of your system I would be very pleased to see Vostokov.exe in the list of running processes (!vm or !process 0 0 WinDbg commands).
lkd> !vm
[...]
0780 svchost.exe 354 ( 1416 Kb)
0720 svchost.exe 330 ( 1320 Kb)
0768 svchost.exe 322 ( 1288 Kb)
07d4 svchost.exe 296 ( 1184 Kb)
0dc8 Vostokov.exe 134 ( 536 Kb)
019c smss.exe 128 ( 512 Kb)
0ec4 wmplayer.exe 0 ( 0 Kb)
0288 wmplayer.exe 0 ( 0 Kb)
01ac wmplayer.exe 0 ( 0 Kb)
lkd> !process 0 0
**** NT ACTIVE PROCESS DUMP ****
PROCESS fffffa8003bf1040
SessionId: none Cid: 0004 Peb: 00000000 ParentCid: 0000
DirBase: 00124000 ObjectTable: fffff88000000080 HandleCount: 570.
Image: System
[...]
PROCESS fffffa8005eeac10
SessionId: 2 Cid: 0888 Peb: 7fffffd5000 ParentCid: 0458
DirBase: 1c64e000 ObjectTable: fffff8800cab5b50 HandleCount: 312.
Image: windbg.exe
PROCESS fffffa8005e87620
SessionId: 2 Cid: 09d4 Peb: 7efdf000 ParentCid: 0f64
DirBase: 112938000 ObjectTable: fffff8800c8b2980 HandleCount: 28.
Image: cmd.exe
PROCESS fffffa800579cb50
SessionId: 2 Cid: 0dc8 Peb: 7efdf000 ParentCid: 09d4
DirBase: 092aa000 ObjectTable: fffff880105df610 HandleCount: 9.
Image: Vostokov.exe
PROCESS fffffa8005e3e7a0
SessionId: 2 Cid: 09c8 Peb: 7efdf000 ParentCid: 0b24
DirBase: 78baf000 ObjectTable: fffff8800cfe0a30 HandleCount: 433.
Image: iexplore.exe
PROCESS fffffa8005f53040
SessionId: 2 Cid: 0db8 Peb: 7fffffd9000 ParentCid: 0458
DirBase: 11856e000 ObjectTable: fffff8800c460710 HandleCount: 45.
Image: notepad.exe
lkd> .process /r /p fffffa800579cb50
Implicit process is now fffffa80`0579cb50
lkd> lmv m Vostokov
start end module name
00000000`001f0000 00000000`001fe000 Vostokov (deferred)
Image path: c:\Users\[...]\Vostokov.exe
Image name: Vostokov.exe
Timestamp: Tue Nov 24 11:19:31 2009 (4B0BC143)
CheckSum: 000156E1
ImageSize: 0000E000
File version: 1.0.0.0
Product version: 1.0.0.0
File flags: 0 (Mask 17)
File OS: 4 Unknown Win32
File type: 1.0 App
File date: 00000000.00000000
Translations: 1809.04b0
CompanyName: DumpAnalysis.org
ProductName: Vostokov Application
InternalName: Vostokov
OriginalFilename: Vostokov.exe
ProductVersion: Just born
FileVersion: Just born
FileDescription: Just born Vostokov Application
LegalCopyright: Copyright (C) 2009 Dmitry Vostokov
Comments: Written by Dmitry Vostokov
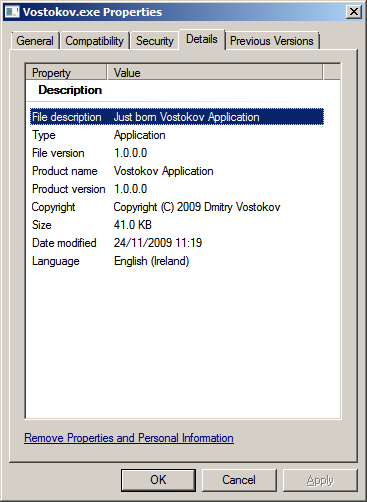
You can inspect its memory if you attach WinDbg to a running instance or from a complete memory or a user process dump (symbols are supplied):
0:001> da /c 90 Vostokov!szCopyright
00000000`001fac40 "Vostokov.exe, Just born version 1.0.0.0, Copyright (c) 2009 by Dmitry Vostokov, DumpAnalysis.org"
You can download my moniker together with .cpp and .pdb files from here (named in a classic 8.3 format):
Download Vostokov.zip
Now I’m going to teach it something useful and release the next aged version soon.
- Dmitry Vostokov @ DumpAnalysis.org -
Posted in Announcements, Computational Ghosts and Bug Hauntings, Fun with Crash Dumps, Memory Religion (Memorianity) | No Comments »
Wednesday, November 18th, 2009
A few days ago I noticed that one euro became 10 times more than its usual conversion value to Russian rouble (ruble). As shown on the picture below it was 1:430.96 instead of expected 1:43.096. At first, I thought of a sudden devaluation and rushed to financial websites for confirmation but they didn’t show any signs of it. I then wanted to announce my findings and cause panic on Wall Street (computers crash there too) but other battles with bugs set this problem aside.

This evening I noticed that it was fixed (remotely, I suppose, on a distant server):

- Dmitry Vostokov @ DumpAnalysis.org -
Posted in Computational Ghosts and Bug Hauntings, Debugging | 1 Comment »
Saturday, September 26th, 2009
This is a revised, edited, cross-referenced and thematically organized volume of selected DumpAnalysis.org blog posts about crash dump analysis and debugging written in October 2008 - June 2009 for software engineers developing and maintaining products on Windows platforms, quality assurance engineers testing software on Windows platforms and technical support and escalation engineers dealing with complex software issues. The third volume features:
- 15 new crash dump analysis patterns
- 29 new pattern interaction case studies
- Trace analysis patterns
- Updated checklist
- Fully cross-referenced with Volume 1 and Volume 2
- New appendixes
Product information:
- Title: Memory Dump Analysis Anthology, Volume 3
- Author: Dmitry Vostokov
- Language: English
- Product Dimensions: 22.86 x 15.24
- Paperback: 404 pages
- Publisher: Opentask (20 December 2009)
- ISBN-13: 978-1-906717-43-8
- Hardcover: 404 pages
- Publisher: Opentask (30 January 2010)
- ISBN-13: 978-1-906717-44-5

Back cover features 3D computer memory visualization image.
- Dmitry Vostokov @ DumpAnalysis.org -
Posted in Announcements, AntiPatterns, Art, Assembly Language, Books, C and C++, CDF Analysis Tips and Tricks, Certification, Citrix, Code Reading, Common Mistakes, Computational Ghosts and Bug Hauntings, Computer Science, Countefactual Debugging, Crash Dump Analysis, Crash Dump Patterns, Crash Dumps for Dummies, DebugWare Patterns, Debugging, Debugging Slang, Deep Down C++, Education and Research, Escalation Engineering, Fun with Crash Dumps, Futuristic Memory Dump Analysis, Games for Debugging, Hardware, Horrors of Computation, Hyper-V, Intelligent Memory Movement, Kernel Development, Mathematics of Debugging, Memiotics (Memory Semiotics), Memoidealism, Memoretics, Memory Analysis Culture, Memory Analysis Forensics and Intelligence, Memory Dreams, Memory Dump Analysis Jobs, Memory Space Music, Memory Visualization, Memuonics, Minidump Analysis, Multithreading, Music for Debugging, New Acronyms, New Words, Occult Debugging, Philosophy, Poetry, Psi-computation, Publishing, Science of Memory Dump Analysis, Science of Software Tracing, Security, Software Architecture, Software Defect Construction, Software Engineering, Software Generalist, Software Narratology, Software Technical Support, Software Trace Analysis, Software Tracing for Dummies, Testing, Tools, Trace Analysis Patterns, Training and Seminars, Troubleshooting Methodology, Virtualization, Vista, Visual Dump Analysis, WinDbg Scripts, WinDbg Tips and Tricks, WinDbg for GDB Users, Windows 7, Windows Server 2008, Windows System Administration | No Comments »
Tuesday, June 9th, 2009
The Adelphi Training Center in Dublin, Ireland, is haunted by the ghost of pre-Internet epoch. During one debugging night, when installing a secret service, Drilliam Traceless was murdered by a redundant engineer who was envy to his charisma. He stubbed him in the back while Drilliam was unlocking his mini-computer case. He died whispering: “I’ll be back debugging”. His face sometimes appears on greenish screensavers running on computers located in that center. During morning training sessions, many trainees think this is a kind of the so called Guinness effect.
The story is adapted from The Ghost of Adelphi Theatre.
- Dmitry Vostokov @ DumpAnalysis.org -
Posted in Computational Ghosts and Bug Hauntings, Debugging, Fun with Crash Dumps, Psi-computation | No Comments »
Friday, May 22nd, 2009
This is a computational ghost that comes from CPU spiking tops and hills to bring sickness to small programs. Red color from RGB triplets provides early warning signs.
Inspired by non-computational Acheri.
PS. This category of computational ghosts and bug hauntings was also inspired by an e-mail conversation between two software engineers that I witnessed some years ago when one told another: “Is this your fix that is still haunting us?”. If you have ever visited heated code review debates you can imagine the provoked response.
- Dmitry Vostokov @ DumpAnalysis.org -
Posted in Computational Ghosts and Bug Hauntings, Fun with Crash Dumps, Psi-computation | No Comments »