Cadaver Worm: An Exercise in Malware Fiction
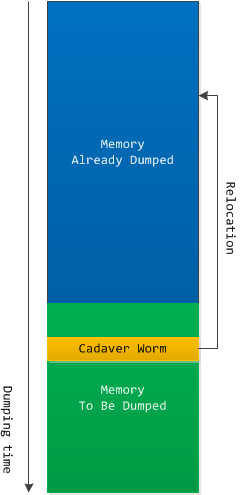
Sunday, February 10th, 2013The discovery of a “black hole horizon” in a complete memory dump inspired this fictitious malware. There in a dump we discovered an innocuous ASCII message:
fffff880`15925010 fffff880`159250d0 "Dumping physical memory to disk: 80% ."
A little thought and we realized that this page was saved to a page file at the time when only 80% of memory were dumped. So we do not know what were in that page during the rest of the time (and would never know). I guess Cadaver Worms live there spreading from PC to PC and causing blue screens immediately upon infection to minimize discovery. They are not in crash dumps because they relocate themselves during the system dump procedure. They thaw frozen CPUs and send themselves to network. Who would suspect a computer showing a blue screen sending network packets?
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -