Trace Analysis Patterns (Part 89)
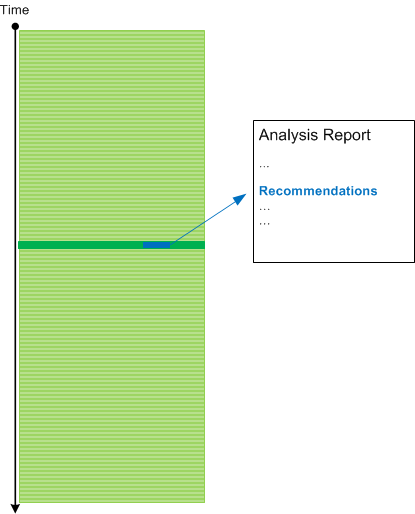
Thursday, June 26th, 2014Usually when we analyse traces and find an Anchor or Error Message we do backtracking using a combination of Data Flow and Message Sets and selecting appropriate log messages to form Back Trace leading to a possible root cause message:
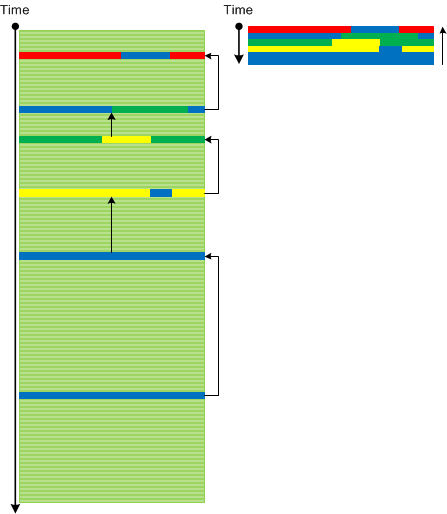
This pattern is different from Error Thread pattern which just backtracks messages having the same TID (or in general ATID). It is also different from Exception Stack Trace pattern which is just a serialized stack trace from memory snapshot.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -