Archive for May, 2011
Friday, May 27th, 2011
Tapping - The act of collecting software traces for subsequent pattern-driven trace analysis. From TAP (Trace Analysis Pattern).
Examples: We started tapping the service for any anomalies. Software tapping methods and tools.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Debugging, Debugging Slang, Memory Analysis Forensics and Intelligence, Memory Intelligence Agency, New Acronyms, Software Trace Analysis | No Comments »
Thursday, May 26th, 2011
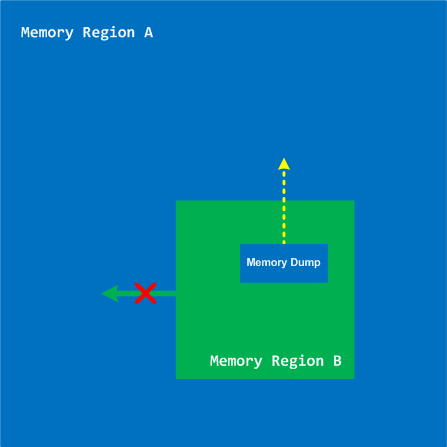
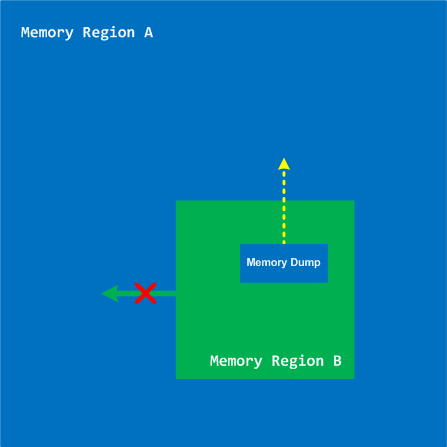
A few years ago when searching for interdisciplinary ideas via metaphorical bijections I found many parallels between memory dump analysis and intelligence. At that time I started reading a book Intelligence Analysis: A Target-Centric Approach, 2nd Edition (currently in the 3rd edition
(currently in the 3rd edition ). Now looking at the cover of that book I think it might have later unconsciously influenced the picture of RADII process:
). Now looking at the cover of that book I think it might have later unconsciously influenced the picture of RADII process:




After some break with studying intelligence I now resume it after I found that tapping (trace analysis patterns for general memory traces with extra uncertainty attribute) could be a good basis for intelligence analysis patterns. My recent jump into cyber warfare also contributed to that. As a fictional continuation from MIx line (MI5, MI6 *) I feel the need to create MIA to promote such ideas (it is a well known fact that MI6 initially started as an amateurish organization **).
* MI5 and MI6 both look to me as pool tags  GCHQ sounds like related to Garbage Collector
GCHQ sounds like related to Garbage Collector
** Strategic Intelligence [5 volumes], Volume 1
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Cyber Warfare, Memory Analysis Forensics and Intelligence, Memory Intelligence Agency, Security, Software Trace Analysis | No Comments »
Tuesday, May 24th, 2011
“… the vital point for you to understand is that all” tracing “must be conducted with the creation of” solution “in mind. That is what must colour and control your selection of” tracing “events.”
Michael Allen, The Truth About Writing
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Bugtations, Debugging, Fun with Debugging, Fun with Software Traces, Software Narratology, Software Trace Analysis, Software Trace Reading | No Comments »
Tuesday, May 24th, 2011
One of the questions asked during Introduction to Pattern-Driven Software Problem Solving Webinar was how to map bugcheck codes to crash dump analysis patterns. I’m starting this post to provide a few initial mappings and plan to extend it later.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Bugchecks Depicted, Crash Dump Analysis, Crash Dump Patterns, Debugging, Kernel Development | No Comments »
Sunday, May 22nd, 2011
Being deep into intelligence analysis while preparing for cyberwarfare memory dump analysis presentation I came to an idea of intelligence analysis patterns based on software trace analysis patterns and software narratology. Basically we consider intelligence data as pseudo-software trace messages with an additional probability field (column). Most of the patterns can be transferred and used immediately in intelligence analysis and I’m working on such a map. Because real software trace messages are quite certain (deterministic) where their sequences sometimes not (see, for example, Impossible Trace pattern) there are some unique patterns applicable only in intelligence analysis domain and I’m working on the first such pattern to introduce it in the next part.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Cyber Warfare, Intelligence Analysis Patterns, Memory Analysis Forensics and Intelligence, Security, Software Narratology, Software Trace Analysis, Software Trace Analysis and History, Trace Analysis Patterns | No Comments »
Saturday, May 21st, 2011
Posted in Announcements, Debugging, EasyDbg, Memory Analysis Forensics and Intelligence, New Acronyms, Software Trace Analysis, Software Trace Reading, Tool Objects, Tools, Trace Analysis Patterns | No Comments »
Friday, May 20th, 2011
I came to the idea of Memory-Time when reading about Samuel Alexander’s Space-Time (see also Memory Creates God). Here Memory plays the same foundational part as Space with memory-instants paralleling point-instants. I recently found the notion of memory-time (small capitals) appearing in Wittgenstein lectures as cited in Jaakko Hintikka’s paper “Wittgenstein on being and time”. However, it is considered there from the phenomenological subject-based perspective with a role of memory in the creation of time and external world and was only present in the earlier Tractatus-based Wittgenstein’s worldview.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Memoidealism, Memory Religion (Memorianity), Memuonics, Metaphysics of Memory Worldview, Philosophy | No Comments »
Sunday, May 15th, 2011
Presentation Software Trace and Memory Dump Analysis: Patterns, Tools, Processes and Best Practices from E2E Virtualization Conference (13th of May, 2011) is available for download:
http://www.dumpanalysis.com/STMDA-materials
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Debugging, Debugging Methodology, Escalation Engineering, Presentations, Root Cause Analysis, Software Behavior Patterns, Software Technical Support, Software Trace Analysis, Software Trace Reading, Tools, Trace Analysis Patterns, Training and Seminars, Troubleshooting Methodology | No Comments »
Wednesday, May 11th, 2011
In this series we start with our analysis of monsters in the realm of computer memory, software defects, malware, corrupt software structures and their various behaviour. Some of monsters are based on exaggerated crash dump and software trace patterns, some are based on the accumulated debugging and technical support wisdom. The first monster we present today is called Chimera and it lives in DLL Hell. It is based on a exaggerated pattern called Module Variety. When opening a 64-bit memory dump it shows several pages of modules (lm WinDbg command):
As the monster’s creator explained to me they used an experimental way to represent every class object as a loaded component. And it was a word processor where every paragraph, every sentence, every word and every letter was an object implemented in a separate module! The goal was to have any letter literally dance on a screen if necessary.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Computer Memory Monsters, Fun with Crash Dumps, Fun with Debugging, Fun with Malware, Horrors of Computation, Memory Dump Fiction, Software Narrative Fiction | No Comments »
Monday, May 9th, 2011
Having written on how Memoidealism explains miracles I now move into explaining the whole discipline of natural theology. I use one of the current definitions of it as “the idea that there exists some link between the world we observe and another transcendent realm” (Alister McGrath, Darwinism and The Divine). One such link is a memory dump from an inaccessible memory region.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Intelligent Memory Movement, Memoidealism, Memory Religion (Memorianity), Metaphysics of Memory Worldview, Philosophy, Religion | No Comments »
Sunday, May 8th, 2011
Learn how to analyze application, service and system crashes and freezes, navigate through memory dump space and diagnose heap corruption, memory leaks, CPU spikes, blocked threads, deadlocks, wait chains, and much more. We use a unique and innovative pattern-driven analysis approach to speed up the learning curve.

Memory Dump Analysis Services organizes a training course.
If you are registered you are allowed to optionally submit your memory dumps before the training. This will allow us in addition to the carefully constructed problems tailor extra examples to the needs of the attendees. All registrants will receive an optional pre-test before the first session and an optional test after each session.
The training consists of 2 four-hour sessions (4 hours on the first day and 4 hours on the next day). When you finish the training you additionally get:
- A full transcript in PDF format (retail price $200)
- 5 volumes of Memory Dump Analysis Anthology in PDF format (retail price $100)
- An attendance certificate (PDF format)
Prerequisites: Basic Windows troubleshooting
Session 1: August 1, 2011 2:00 PM - 6:00 PM BST
Session 2: August 2, 2011 2:00 PM - 6:00 PM BST
Price: 210 USD
Space is limited.
Reserve your remote training seat now.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Crash Dump Analysis, Crash Dump Patterns, Memory Dump Analysis Services, Software Technical Support, Testing, Tools, Training and Seminars, Vista, WinDbg Tips and Tricks, Windows 7, Windows Server 2008, Windows System Administration, x64 Windows | No Comments »
Thursday, May 5th, 2011
This is a forthcoming virtual event to learn analysis of blockages, delays, obstructions, preventions, and stoppages in victimware suffering from software defects and malware. Additional information on how to join will be available soon on the main portal page:
http://www.dumpanalysis.org/stoppages2011
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Crash Dump Analysis, Debugging, Malware Analysis, Software Trace Analysis, StopPages Conferences, Victimware | No Comments »
Sunday, May 1st, 2011
Most of the time software trace messages coming from the same source code fragment (PLOT) contain invariant parts such as function and variable names, descriptions, and mutable parts such as pointer values and error codes. Message Invariant is a pattern useful for comparative analysis of several trace files where we are interested in message differences. For example, in one troubleshooting scenario certain objects were not created correctly for one user. We suspected a different object version was linked to a user profile. Separate application debug traces were recorded for each user and we could see version 0×4 for the problem user and 0×5 for all other normal users:
# Module PID TID Time Message
[...]
2782 ModuleA 2124 5648 10:58:03.356 CreateObject: pObject 0×00A83D30 data ([…]) version 0×4
[…]
# Module PID TID Time Message
[...]
4793 ModuleA 2376 8480 09:22:01.947 CreateObject: pObject 0×00BA4E20 data ([…]) version 0×5
[…]
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in CDF Analysis Tips and Tricks, Debugging, Software Trace Analysis, Software Trace Reading, Structural Trace Patterns, Trace Analysis Patterns | No Comments »
Sunday, May 1st, 2011
To model software behavior at application and system levels, test generative debugging scenarious and construct software defects using metaprogramming I started working on MdTL (Metadefect Template Library). Its consists of C++ templates for structural and behavioral patterns. The simplest examples include Threads<Spike> and Spike<Thread>. The template classes can be more complex, of course, utilizing the full power of C++, STL, and existing libraries like Boost. The unique and novel feature of this library is the inclusion of dual classes of behaviour such as Leak<>, Deadlock<>, Overflow<>, Residue<>, Exception<>, Contention<>, etc. parameterized by various structural memory classes like Process<>, Thread<>, Heap<>, Stack<>, Region<>, Buffer<>, etc. MdTL also includes classes to model software tracing and this will be used for simultaneous software trace and memory dump analysis case study in the forthcoming presentation. I also plan to extend this metaprogramming approach in the future to model malware analysis patterns by introducing Metamalware Template Library (MmTL).
Forthcoming parts will introduce template classes and examples.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in C and C++, Crash Dump Patterns, Debugging, Generative Debugging, Malware Analysis, Malware Patterns, Metadefect Template Library, Metamalware, New Acronyms, Software Behavior Patterns, Software Defect Construction, Structural Memory Patterns, Structural Trace Patterns, Tools, Trace Analysis Patterns, Victimware | No Comments »