October 5th, 2011
A page to reference all different kinds of symbol patterns is necessary, so I created this post:
I’ll update it as soon as I add more similar patterns.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Crash Dump Analysis, Crash Dump Patterns, Debugging | No Comments »
October 4th, 2011
First, we announced Debugging TV and its first weekly program called Frames where each episode features some facet of debugging, memory dump, and software trace analysis in 8 minutes. The first episode is about symbol files plus extra 8 minutes to ask questions.
Debugging TV Frame 0×01
Date: Friday, October 7, 2011
Time: 5:45 PM - 6:01 PM BST
Space is limited.
Reserve your seat now at:
https://www3.gotomeeting.com/register/640694470
Second, Accelerated Windows Memory Dump Analysis book became available on Amazon and Barnes & Noble.
Third, a recording of Fundamentals of Complete Crash and Hang Memory Dump Analysis (Revision 2) Webinar was made available for viewing.
Fourth, I’m working now on the next 5 crash dump analysis patterns to be published this week.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Books, Crash Dump Analysis, Debugging, Debugging TV, Publishing, WinDbg Tips and Tricks | 2 Comments »
September 26th, 2011
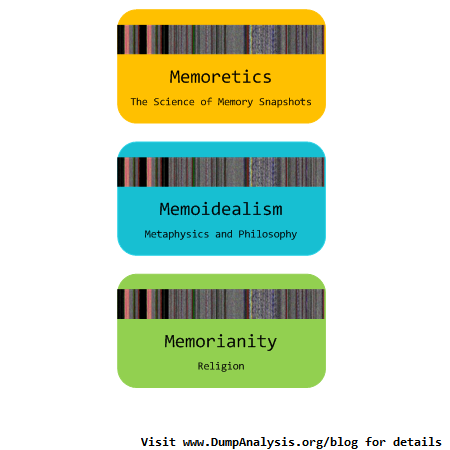
Memoretics views Cyber Space as Memory Space + Memory Data. Here Memory Space consists of many different memory spaces. Although data is private property memory space where it is located is not:

We propose private property on memory spaces and their partitions as a solution to various Cyber problems such as Cyber Crime and Cyber War:

- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Cyber Intelligence, Cyber Problems, Cyber Security, Cyber Space, Cyber Warfare, Memory Analysis Forensics and Intelligence, Security | No Comments »
September 26th, 2011
The idea of this bugtation came to me when I was browsing Wrotten English: A Celebration of Literary Misprints, Mistakes and Mishaps book in a local Costa:
book in a local Costa:


In a chapter on funny book titles I could find:
Dumps (The story of a plain app and its struggles in computation).
Dumps by Meade (Chambers, 1905)
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Bugtations, Crash Dump Analysis, Fun with Crash Dumps | No Comments »
September 21st, 2011
Memoretics promotes pattern-driven memory dump and software trace analysis which has many uses but not limited to:
- Software and site reliability
- Software Debugging
- QA and Software Testing
- Computer Security
- Software Troubleshooting
- Malware Research and Analysis
- Tools as a Service (TaaS)
- Supportability
- Software Diagnostics

- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Cloud Memory Dump Analysis, Computer Forensics, Crash Dump Analysis, Crash Dump Patterns, DebugWare Patterns, Debugging, Debugging Trends, Escalation Engineering, Malware Analysis, Malware Patterns, Memiotics (Memory Semiotics), Memoretics, Memory Analysis Forensics and Intelligence, Metadefect Template Library, Metamalware, Pattern Models, Pattern Prediction, Reverse Engineering, Root Cause Analysis, Science of Memory Dump Analysis, Science of Software Tracing, Security, Software Behavior DNA, Software Behavior Patterns, Software Behavioral Genome, Software Defect Construction, Software Engineering, Software Generalist, Software Narratology, Software Support Patterns, Software Technical Support, Software Trace Analysis, Software Troubleshooting Patterns, Structural Memory Patterns, Structural Trace Patterns, Systems Thinking, Testing, Tools, Trace Analysis Patterns, Troubleshooting Methodology, UI Problem Analysis Patterns, Unified Debugging Patterns, Victimware, Windows System Administration, Workaround Patterns | No Comments »
September 21st, 2011
Memoretics as a science of memory snapshots borrows many ideas from the following disciplines (the list is not exhaustive):
- Troubleshooting and Debugging
- Intelligence Analysis
- Critical Thinking
- Forensics
- Linguistics
- Archaeology
- Psychoanalysis
- History
- Mathematics: Sets and Categories
- Literary Criticism and Narratology
It also contributes many ideas back. The following diagram depicts such an interaction:

- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Archaeology of Computer Memory, Categorical Debugging, Computer Forensics, Computer Science, Countefactual Debugging, Crash Dump Analysis, Crash Dump De-analysis, Crash Dump Patterns, Debugging, Debugging Methodology, Dublin School of Security, Education and Research, Escalation Engineering, General Memory Analysis, Generative Debugging, Hermeneutics of Memory Dumps and Traces, History, Intelligence Analysis Patterns, M->analysis, Malware Analysis, Malware Patterns, Mathematics of Debugging, Memiotics (Memory Semiotics), Memoretics, Memory Analysis Forensics and Intelligence, Memory Dump Analysis and History, Memory Systems Language, Memory Visualization, Metadefect Template Library, Metamalware, New Debugging School, Paleo-debugging, Pattern Models, Pattern Prediction, Psychoanalysis of Software Maintenance and Support, Psychology, Reverse Engineering, Root Cause Analysis, Science of Memory Dump Analysis, Science of Software Tracing, Security, Software Architecture, Software Behavior DNA, Software Behavior Patterns, Software Behavioral Genome, Software Chorography, Software Chorology, Software Defect Construction, Software Engineering, Software Narratology, Software Technical Support, Software Trace Analysis, Software Trace Analysis and History, Software Trace Deconstruction, Software Trace Linguistics, Software Trace Reading, Software Trace Visualization, Software Tracing Implementation Patterns, Software Troubleshooting Patterns, Software Victimology, Software and History, Structural Memory Analysis and Social Sciences, Structural Memory Patterns, Structural Trace Patterns, Systems Thinking, Testing, Tools, Trace Analysis Patterns, Troubleshooting Methodology, UI Problem Analysis Patterns, Unified Debugging Patterns, Victimware, Virtualization, Visual Dump Analysis, Workaround Patterns | No Comments »
September 19th, 2011
R.E.M. album Out of Time is a great joy to listen for Win32 API debugging veterans familiar with Visual Basic
is a great joy to listen for Win32 API debugging veterans familiar with Visual Basic .
.


I put my own track title names here:
1. I Can’t Find It!
2. Losing My Data
3. LOWORD
4. Near A Wild Pointer (*pa, *pa, *ppa, …)
5. End Of Session
6. Happy Customers
7. Be LONG
8. Half A Word Away! (A Miracle)
9. Printer Driver (Can’t Spell Its Name)
10. Customer Feedback (One, Two, Three, …)
11. Found Me In Dumps
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Debugging, Fun with Crash Dumps, Fun with Debugging, Music for Debugging | No Comments »
September 17th, 2011
Whereas DNA of a ruptured computation is a coarse grained, software behavioral genome in general is fine grained consisting of multiple behavioral patterns such as seen in memory dumps and software traces. I will elaborate more on it later especially in relation to software behavior profiles. Here’s a nice “memory DNA” metaphorical picture from 3D memory visualization post:

- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Crash Dump Patterns, Memory Visualization, Software Behavior DNA, Software Behavior Patterns, Software Behavioral Genome, Trace Analysis Patterns | No Comments »
September 14th, 2011
Original Message pattern deals with software trace messages where certain activity is repeated several times but the only the first message occurrence or specific message vocabulary has significance for analysis activity. Typical example from CDF/ETW tracing is module load events:
# Module PID TID Time Message
[...]
35835 ModuleA 11000 11640 17:27:28.720 LoadImageEvent: \Device\HarddiskVolume2\Windows\System32\userinit.exe PId 5208
[…]
37684 ModuleA 12332 9576 17:27:29.063 LoadImageEvent: \Windows\System32\userinit.exe PId 573C
[…]
37687 ModuleA 12332 9576 17:27:29.064 LoadImageEvent: \Windows\System32\userinit.exe PId 573C
[…]
What we are looking here is for message invariant like “.exe” but interested in the occurrence of specific path structures like \Device\HarddiskVolume because in our troubleshooting context they signify process launch sequence during terminal session initialization.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in CDF Analysis Tips and Tricks, Debugging, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
September 12th, 2011
If you like the completeness, grand complete memory dumps, multi-volume oeuvres (the more volumes the better) and natural memory visualization you would then like to open this box and listen to this complete performance achievement to get energy and inspiration for long debugging sessions:
Liszt: The Complete Piano Music


- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Complete Memory Dump Analysis, Crash Dump Analysis, Debugging, Memory Visualization, Music for Debugging | No Comments »
September 12th, 2011
In 3×3 format:
Q. What philosophical school do I belong to?
A. I consider myself the last Presocratic philosopher.
Q. What is my difference from the first Presocratics?
A. The philosophy of Memoidealism that I founded postulates that Memory is the essence of things, the first principle, like fire.
Q. Can I name 3 great philosophers?
A. 3 V’s: Giambattista Vico, Circle Vienna, Dmitry Vostokov (*). The circle is not one philosopher though but a cloud memory aggregate. If you insist on a person I would then replace it with Voltaire.
(*) The idea came to me after reading that Ayn Rand could only recommend 3 A’s - Aristotle, Aquinas, and Ayn Rand.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Interviews, Memoidealism, Metaphysics of Memory Worldview, Philosophy | No Comments »
September 12th, 2011
Just noticed this book and pre-ordered it:
Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software


I like the cover picture - I recently bought a Dell Alienware laptop just to do malware and victimware analysis 
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Books, Malware Analysis, Victimware | 3 Comments »
September 7th, 2011
Whereas Stack Trace Collection pattern covers all thread stack traces from a memory dump Stack Trace Set pattern covers only unique non-duplicated thread stack traces differing for example, in stack frame modules and function names. In user process memory dumps it is !uniqstack WinDbg command (don’t forget that command has optional parameters, for example, -v to simulate verbose ~*kv output):
0:000> ~
. 0 Id: f00.f04 Suspend: 0 Teb: 7efdd000 Unfrozen
1 Id: f00.f18 Suspend: 1 Teb: 7efda000 Unfrozen
2 Id: f00.f1c Suspend: 1 Teb: 7efd7000 Unfrozen
0:000> ~*kc
. 0 Id: f00.f04 Suspend: 0 Teb: 7efdd000 Unfrozen
ntdll!NtWaitForMultipleObjects
KERNELBASE!WaitForMultipleObjectsEx
kernel32!WaitForMultipleObjectsExImplementation
kernel32!WaitForMultipleObjects
kernel32!WerpReportFaultInternal
kernel32!WerpReportFault
kernel32!BasepReportFault
kernel32!UnhandledExceptionFilter
ntdll!__RtlUserThreadStart
ntdll!_EH4_CallFilterFunc
ntdll!_except_handler4
ntdll!ExecuteHandler2
ntdll!ExecuteHandler
ntdll!KiUserExceptionDispatcher
KERNELBASE!DebugBreak
ApplicationK!main
ApplicationK!__tmainCRTStartup
kernel32!BaseThreadInitThunk
ntdll!__RtlUserThreadStart
ntdll!_RtlUserThreadStart
1 Id: f00.f18 Suspend: 1 Teb: 7efda000 Unfrozen
ntdll!NtDelayExecution
KERNELBASE!SleepEx
KERNELBASE!Sleep
kernel32!WerpReportFault
kernel32!BasepReportFault
kernel32!UnhandledExceptionFilter
ntdll!__RtlUserThreadStart
ntdll!_EH4_CallFilterFunc
ntdll!_except_handler4
ntdll!ExecuteHandler2
ntdll!ExecuteHandler
ntdll!KiUserExceptionDispatcher
ApplicationK!thread_two
ApplicationK!_callthreadstart
ApplicationK!_threadstart
kernel32!BaseThreadInitThunk
ntdll!__RtlUserThreadStart
ntdll!_RtlUserThreadStart
2 Id: f00.f1c Suspend: 1 Teb: 7efd7000 Unfrozen
ntdll!NtDelayExecution
KERNELBASE!SleepEx
KERNELBASE!Sleep
kernel32!WerpReportFault
kernel32!BasepReportFault
kernel32!UnhandledExceptionFilter
ntdll!__RtlUserThreadStart
ntdll!_EH4_CallFilterFunc
ntdll!_except_handler4
ntdll!ExecuteHandler2
ntdll!ExecuteHandler
ntdll!KiUserExceptionDispatcher
ApplicationK!thread_two
ApplicationK!_callthreadstart
ApplicationK!_threadstart
kernel32!BaseThreadInitThunk
ntdll!__RtlUserThreadStart
ntdll!_RtlUserThreadStart
0:000> !uniqstack
Processing 3 threads, please wait
. 0 Id: f00.f04 Suspend: 0 Teb: 7efdd000 Unfrozen
Start: ApplicationK!mainCRTStartup (013a137c)
Priority: 0 Priority class: 32 Affinity: 3
ChildEBP RetAddr
0037f1a4 770d0bdd ntdll!NtWaitForMultipleObjects+0x15
0037f240 7529162d KERNELBASE!WaitForMultipleObjectsEx+0x100
0037f288 75291921 kernel32!WaitForMultipleObjectsExImplementation+0xe0
0037f2a4 752b9b2d kernel32!WaitForMultipleObjects+0x18
0037f310 752b9bca kernel32!WerpReportFaultInternal+0x186
0037f324 752b98f8 kernel32!WerpReportFault+0x70
0037f334 752b9875 kernel32!BasepReportFault+0x20
0037f3c0 77b10df7 kernel32!UnhandledExceptionFilter+0x1af
0037f3c8 77b10cd4 ntdll!__RtlUserThreadStart+0x62
0037f3dc 77b10b71 ntdll!_EH4_CallFilterFunc+0x12
0037f404 77ae6ac9 ntdll!_except_handler4+0x8e
0037f428 77ae6a9b ntdll!ExecuteHandler2+0x26
0037f4d8 77ab010f ntdll!ExecuteHandler+0x24
0037f4d8 770d280c ntdll!KiUserExceptionDispatcher+0xf
0037f824 013a1035 KERNELBASE!DebugBreak+0x2
0037f828 013a1325 ApplicationK!main+0x25
0037f870 75293677 ApplicationK!__tmainCRTStartup+0xfb
0037f87c 77ad9f02 kernel32!BaseThreadInitThunk+0xe
0037f8bc 77ad9ed5 ntdll!__RtlUserThreadStart+0x70
0037f8d4 00000000 ntdll!_RtlUserThreadStart+0x1b
. 1 Id: f00.f18 Suspend: 1 Teb: 7efda000 Unfrozen
Start: ApplicationK!_threadstart (013a10d1)
Priority: 0 Priority class: 32 Affinity: 3
ChildEBP RetAddr
0080f9ac 770d31bb ntdll!NtDelayExecution+0x15
0080fa14 770d3a8b KERNELBASE!SleepEx+0x65
0080fa24 752d28dd KERNELBASE!Sleep+0xf
0080fa38 752b98f8 kernel32!WerpReportFault+0x3f
0080fa48 752b9875 kernel32!BasepReportFault+0x20
0080fad4 77b10df7 kernel32!UnhandledExceptionFilter+0x1af
0080fadc 77b10cd4 ntdll!__RtlUserThreadStart+0x62
0080faf0 77b10b71 ntdll!_EH4_CallFilterFunc+0x12
0080fb18 77ae6ac9 ntdll!_except_handler4+0x8e
0080fb3c 77ae6a9b ntdll!ExecuteHandler2+0x26
0080fbec 77ab010f ntdll!ExecuteHandler+0x24
0080fbec 013a1000 ntdll!KiUserExceptionDispatcher+0xf
0080ff38 013a10ab ApplicationK!thread_two
0080ff70 013a1147 ApplicationK!_callthreadstart+0x1b
0080ff78 75293677 ApplicationK!_threadstart+0x76
0080ff84 77ad9f02 kernel32!BaseThreadInitThunk+0xe
0080ffc4 77ad9ed5 ntdll!__RtlUserThreadStart+0x70
0080ffdc 00000000 ntdll!_RtlUserThreadStart+0x1b
Total threads: 3
Duplicate callstacks: 1(windbg thread #s follow):
2
Generally, any property can be chosen to form such a set from a collection of stack traces.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Crash Dump Analysis, Crash Dump Patterns, Debugging, Stack Trace Collection, WinDbg Tips and Tricks | 1 Comment »
September 7th, 2011
A few weeks ago when I was asked about my opinion whether the current economic crisis will deepen an idea came to me that Cloud Computing is the last Model piece of MVC (Model-View-Controller) where View is Social Media such as Facebook, LinkedIn, Twitter, etc. and Controller is Internet itself. With the final piece of the puzzle the World needs new MVC Revolution in order to get back on track.
Posted in Cloud Computing, Software Generalist Worldview, Software and Economics, Software and Future, Software and History, Software and Modeling, Software and Politics, Software and Sociology | No Comments »
August 30th, 2011
This is a new pattern about activation contexts. Here we have software exceptions STATUS_SXS_*, for example:
STATUS_SXS_EARLY_DEACTIVATION 0xC015000F
STATUS_SXS_INVALID_DEACTIVATION 0xC0150010
0:000> !analyze -v
[...]
EXCEPTION_RECORD: ffffffff -- (.exr 0xffffffffffffffff)
ExceptionAddress: 77a54441 (ntdll!RtlDeactivateActivationContext+0x00000154)
ExceptionCode: c015000f
ExceptionFlags: 00000000
NumberParameters: 3
Parameter[0]: 00000000
Parameter[1]: 0056cbe8
Parameter[2]: 0056cc18
EXCEPTION_CODE: (NTSTATUS) 0xc015000f - The activation context being deactivated is not the most recently activated one.
CONTEXT: 003df6c8 -- (.cxr 0x3df6c8)
eax=003df9bc ebx=13050002 ecx=00000000 edx=00000000 esi=0056cbe8 edi=0056cc18
eip=77a54441 esp=003df9b0 ebp=003dfa0c iopl=0 nv up ei pl nz na pe nc
cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00000206
ntdll!RtlDeactivateActivationContext+0x154:
77a54441 8b36 mov esi,dword ptr [esi] ds:002b:0056cbe8=0056cbb8
Resetting default scope
STACK_TEXT:
003dfa0c 755aa138 005507d0 13050002 003dfa7c ntdll!RtlDeactivateActivationContext+0×154
003dfa1c 002b1235 00000000 13050002 3a92c68c kernel32!DeactivateActCtx+0×31
003dfa7c 002b13b5 00000001 01f01e98 01f01ec8 TestActCtx!wmain+0×225
003dfac4 75593677 7efde000 003dfb10 77a09f02 TestActCtx!__tmainCRTStartup+0xfa
003dfad0 77a09f02 7efde000 7e35c89d 00000000 kernel32!BaseThreadInitThunk+0xe
003dfb10 77a09ed5 002b140c 7efde000 ffffffff ntdll!__RtlUserThreadStart+0×70
003dfb28 00000000 002b140c 7efde000 00000000 ntdll!_RtlUserThreadStart+0×1b
The ReactOS code for RtlDeactivateActivationContext function suggests the following line of inquiry:
0:000> dt _TEB
TestActCtx!_TEB
+0x000 NtTib : _NT_TIB
+0x01c EnvironmentPointer : Ptr32 Void
+0x020 ClientId : _CLIENT_ID
+0x028 ActiveRpcHandle : Ptr32 Void
+0x02c ThreadLocalStoragePointer : Ptr32 Void
+0x030 ProcessEnvironmentBlock : Ptr32 _PEB
+0x034 LastErrorValue : Uint4B
+0x038 CountOfOwnedCriticalSections : Uint4B
+0x03c CsrClientThread : Ptr32 Void
+0x040 Win32ThreadInfo : Ptr32 Void
+0x044 User32Reserved : [26] Uint4B
+0x0ac UserReserved : [5] Uint4B
+0x0c0 WOW32Reserved : Ptr32 Void
+0x0c4 CurrentLocale : Uint4B
+0x0c8 FpSoftwareStatusRegister : Uint4B
+0x0cc SystemReserved1 : [54] Ptr32 Void
+0x1a4 ExceptionCode : Int4B
+0×1a8 ActivationContextStack : _ACTIVATION_CONTEXT_STACK
+0×1bc SpareBytes1 : [24] UChar
+0×1d4 GdiTebBatch : _GDI_TEB_BATCH
+0×6b4 RealClientId : _CLIENT_ID
+0×6bc GdiCachedProcessHandle : Ptr32 Void
+0×6c0 GdiClientPID : Uint4B
+0×6c4 GdiClientTID : Uint4B
+0×6c8 GdiThreadLocalInfo : Ptr32 Void
+0×6cc Win32ClientInfo : [62] Uint4B
+0×7c4 glDispatchTable : [233] Ptr32 Void
+0xb68 glReserved1 : [29] Uint4B
+0xbdc glReserved2 : Ptr32 Void
+0xbe0 glSectionInfo : Ptr32 Void
+0xbe4 glSection : Ptr32 Void
+0xbe8 glTable : Ptr32 Void
+0xbec glCurrentRC : Ptr32 Void
+0xbf0 glContext : Ptr32 Void
+0xbf4 LastStatusValue : Uint4B
+0xbf8 StaticUnicodeString : _UNICODE_STRING
+0xc00 StaticUnicodeBuffer : [261] Wchar
+0xe0c DeallocationStack : Ptr32 Void
+0xe10 TlsSlots : [64] Ptr32 Void
+0xf10 TlsLinks : _LIST_ENTRY
+0xf18 Vdm : Ptr32 Void
+0xf1c ReservedForNtRpc : Ptr32 Void
+0xf20 DbgSsReserved : [2] Ptr32 Void
+0xf28 HardErrorMode : Uint4B
+0xf2c Instrumentation : [16] Ptr32 Void
+0xf6c WinSockData : Ptr32 Void
+0xf70 GdiBatchCount : Uint4B
+0xf74 InDbgPrint : UChar
+0xf75 FreeStackOnTermination : UChar
+0xf76 HasFiberData : UChar
+0xf77 IdealProcessor : UChar
+0xf78 Spare3 : Uint4B
+0xf7c ReservedForPerf : Ptr32 Void
+0xf80 ReservedForOle : Ptr32 Void
+0xf84 WaitingOnLoaderLock : Uint4B
+0xf88 Wx86Thread : _Wx86ThreadState
+0xf94 TlsExpansionSlots : Ptr32 Ptr32 Void
+0xf98 ImpersonationLocale : Uint4B
+0xf9c IsImpersonating : Uint4B
+0xfa0 NlsCache : Ptr32 Void
+0xfa4 pShimData : Ptr32 Void
+0xfa8 HeapVirtualAffinity : Uint4B
+0xfac CurrentTransactionHandle : Ptr32 Void
+0xfb0 ActiveFrame : Ptr32 _TEB_ACTIVE_FRAME
+0xfb4 FlsData : Ptr32 Void
0:000> dt _ACTIVATION_CONTEXT_STACK
TestActCtx!_ACTIVATION_CONTEXT_STACK
+0x000 Flags : Uint4B
+0x004 NextCookieSequenceNumber : Uint4B
+0x008 ActiveFrame : Ptr32 _RTL_ACTIVATION_CONTEXT_STACK_FRAME
+0x00c FrameListCache : _LIST_ENTRY
0:000> dt _RTL_ACTIVATION_CONTEXT_STACK_FRAME
ntdll!_RTL_ACTIVATION_CONTEXT_STACK_FRAME
+0x000 Previous : Ptr32 _RTL_ACTIVATION_CONTEXT_STACK_FRAME
+0x004 ActivationContext : Ptr32 _ACTIVATION_CONTEXT
+0x008 Flags : Uint4B
0:000> dd 0056cc18 l4
0056cc18 0056cbe8 0056ca6c 00000028 13050003
0:000> dd 0056cbe8
0056cbe8 0056cbb8 0056c934 00000028 13050002
0056cbf8 00000000 00000000 00000000 00000000
0056cc08 00000000 00000000 00000000 00000000
0056cc18 0056cbe8 0056ca6c 00000028 13050003
0056cc28 00000000 00000000 00000000 00000000
0056cc38 00000000 00000000 00000000 00000000
0056cc48 00000000 00000000 0000000c 00000000
0056cc58 00000000 00000000 00000000 00000000
0:000> dd 0056cbb8
0056cbb8 00000000 0056c7fc 00000028 13050001
0056cbc8 00000000 00000000 00000000 00000000
0056cbd8 00000000 00000000 00000000 00000000
0056cbe8 0056cbb8 0056c934 00000028 13050002
0056cbf8 00000000 00000000 00000000 00000000
0056cc08 00000000 00000000 00000000 00000000
0056cc18 0056cbe8 0056ca6c 00000028 13050003
0056cc28 00000000 00000000 00000000 00000000
We see that a different cookie was found on top of the thread activation stack and the code raised the runtime exception.
For this pattern I have also created a modeling application and present its source code with additional memory dump analysis in a separate post.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Crash Dump Analysis, Crash Dump Patterns, Debugging, MFC Debugging | No Comments »