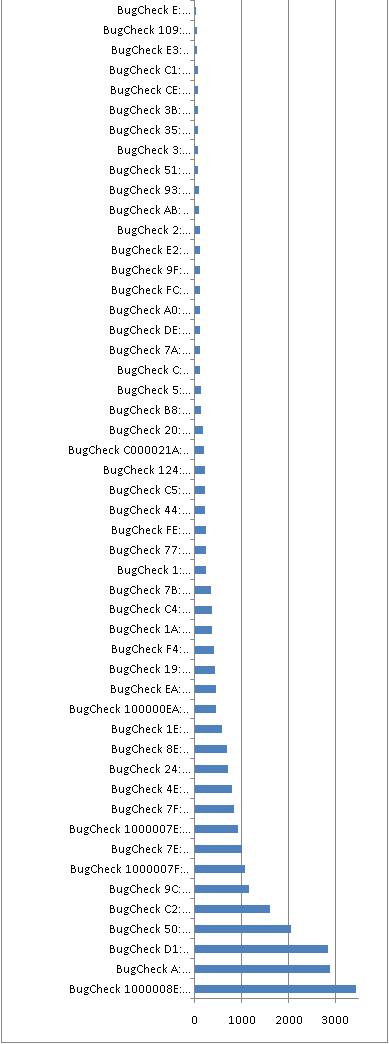
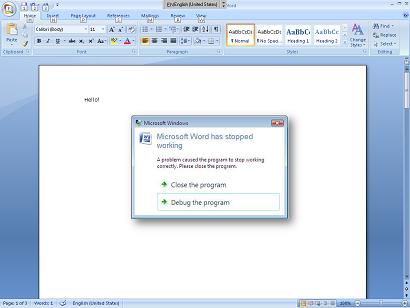
259 bugchecks are documented in WinDbg help. I did Google search for every one and here is their search results distribution graph cut off for data with less than 10 matches:
Of course there is some noise and matches do not always correspond to WinDbg bugcheck analysis output but we can get rough idea about bugcheck frequency. For example, unhandled exceptions in kernel mode, IRQL contract violation, pool corruption and hardware failures are the most frequent. Here is the full table:
|
BugCheck 1000008E: KERNEL_MODE_EXCEPTION_NOT_HANDLED_M
|
3440
|
|
BugCheck A: IRQL_NOT_LESS_OR_EQUAL
|
2890
|
|
BugCheck D1: DRIVER_IRQL_NOT_LESS_OR_EQUAL
|
2840
|
|
BugCheck 50: PAGE_FAULT_IN_NONPAGED_AREA
|
2040
|
|
BugCheck C2: BAD_POOL_CALLER
|
1600
|
|
BugCheck 9C: MACHINE_CHECK_EXCEPTION
|
1150
|
|
BugCheck 1000007F: UNEXPECTED_KERNEL_MODE_TRAP_M
|
1070
|
|
BugCheck 7E: SYSTEM_THREAD_EXCEPTION_NOT_HANDLED
|
998
|
|
BugCheck 1000007E: SYSTEM_THREAD_EXCEPTION_NOT_HANDLED_M
|
917
|
|
BugCheck 7F: UNEXPECTED_KERNEL_MODE_TRAP
|
834
|
|
BugCheck 4E: PFN_LIST_CORRUPT
|
799
|
|
BugCheck 24: NTFS_FILE_SYSTEM
|
697
|
|
BugCheck 8E: KERNEL_MODE_EXCEPTION_NOT_HANDLED
|
686
|
|
BugCheck 1E: KMODE_EXCEPTION_NOT_HANDLED
|
571
|
|
BugCheck 100000EA: THREAD_STUCK_IN_DEVICE_DRIVER_M
|
450
|
|
BugCheck EA: THREAD_STUCK_IN_DEVICE_DRIVER
|
446
|
|
BugCheck 19: BAD_POOL_HEADER
|
434
|
|
BugCheck F4: CRITICAL_OBJECT_TERMINATION
|
397
|
|
BugCheck 1A: MEMORY_MANAGEMENT
|
373
|
|
BugCheck C4: DRIVER_VERIFIER_DETECTED_VIOLATION
|
360
|
|
BugCheck 7B: INACCESSIBLE_BOOT_DEVICE
|
347
|
|
BugCheck 1: APC_INDEX_MISMATCH
|
242
|
|
BugCheck 77: KERNEL_STACK_INPAGE_ERROR
|
240
|
|
BugCheck FE: BUGCODE_USB_DRIVER
|
239
|
|
BugCheck 44: MULTIPLE_IRP_COMPLETE_REQUESTS
|
216
|
|
BugCheck C5: DRIVER_CORRUPTED_EXPOOL
|
207
|
|
BugCheck 124: WHEA_UNCORRECTABLE_ERROR
|
204
|
|
BugCheck C000021A: STATUS_SYSTEM_PROCESS_TERMINATED
|
187
|
|
BugCheck 20: KERNEL_APC_PENDING_DURING_EXIT
|
168
|
|
BugCheck B8: ATTEMPTED_SWITCH_FROM_DPC
|
124
|
|
BugCheck 5: INVALID_PROCESS_ATTACH_ATTEMPT
|
123
|
|
BugCheck C: MAXIMUM_WAIT_OBJECTS_EXCEEDED
|
110
|
|
BugCheck 7A: KERNEL_DATA_INPAGE_ERROR
|
110
|
|
BugCheck DE: POOL_CORRUPTION_IN_FILE_AREA
|
106
|
|
BugCheck A0: INTERNAL_POWER_ERROR
|
104
|
|
BugCheck FC: ATTEMPTED_EXECUTE_OF_NOEXECUTE_MEMORY
|
101
|
|
BugCheck 9F: DRIVER_POWER_STATE_FAILURE
|
98
|
|
BugCheck E2: MANUALLY_INITIATED_CRASH
|
98
|
|
BugCheck 2: DEVICE_QUEUE_NOT_BUSY
|
97
|
|
BugCheck AB: SESSION_HAS_VALID_POOL_ON_EXIT
|
86
|
|
BugCheck 93: INVALID_KERNEL_HANDLE
|
83
|
|
BugCheck 51: REGISTRY_ERROR
|
73
|
|
BugCheck 3: INVALID_AFFINITY_SET
|
71
|
|
BugCheck 35: NO_MORE_IRP_STACK_LOCATIONS
|
71
|
|
BugCheck 3B: SYSTEM_SERVICE_EXCEPTION
|
70
|
|
BugCheck CE: DRIVER_UNLOADED_WITHOUT_CANCELLING_PENDING_OPERATIONS
|
65
|
|
BugCheck C1: SPECIAL_POOL_DETECTED_MEMORY_CORRUPTION
|
59
|
|
BugCheck E3: RESOURCE_NOT_OWNED
|
43
|
|
BugCheck 109: CRITICAL_STRUCTURE_CORRUPTION
|
33
|
|
BugCheck E: NO_USER_MODE_CONTEXT
|
32
|
|
BugCheck D: MUTEX_LEVEL_NUMBER_VIOLATION
|
23
|
|
BugCheck 12: TRAP_CAUSE_UNKNOWN
|
14
|
|
BugCheck 23: FAT_FILE_SYSTEM
|
10
|
|
BugCheck 116: VIDEO_TDR_ERROR
|
10
|
|
BugCheck 9: IRQL_NOT_GREATER_OR_EQUAL
|
9
|
|
BugCheck 10D: WDF_VIOLATION
|
9
|
|
BugCheck 4: INVALID_DATA_ACCESS_TRAP
|
8
|
|
BugCheck 6: INVALID_PROCESS_DETACH_ATTEMPT
|
8
|
|
BugCheck 3F: NO_MORE_SYSTEM_PTES
|
8
|
|
BugCheck C9: DRIVER_VERIFIER_IOMANAGER_VIOLATION
|
8
|
|
BugCheck D0: DRIVER_CORRUPTED_MMPOOL
|
8
|
|
BugCheck 117: VIDEO_TDR_TIMEOUT_DETECTED
|
8
|
|
BugCheck F: SPIN_LOCK_ALREADY_OWNED
|
7
|
|
BugCheck 11: THREAD_NOT_MUTEX_OWNER
|
6
|
|
BugCheck 6B: PROCESS1_INITIALIZATION_FAILED
|
6
|
|
BugCheck BE: ATTEMPTED_WRITE_TO_READONLY_MEMORY
|
6
|
|
BugCheck B: NO_EXCEPTION_HANDLING_SUPPORT
|
5
|
|
BugCheck 27: RDR_FILE_SYSTEM
|
5
|
|
BugCheck 41: MUST_SUCCEED_POOL_EMPTY
|
5
|
|
BugCheck 96: INVALID_WORK_QUEUE_ITEM
|
5
|
|
BugCheck D5: DRIVER_PAGE_FAULT_IN_FREED_SPECIAL_POOL
|
5
|
|
BugCheck DA: SYSTEM_PTE_MISUSE
|
5
|
|
BugCheck E1: WORKER_THREAD_RETURNED_AT_BAD_IRQL
|
5
|
|
BugCheck E6: DRIVER_VERIFIER_DMA_VIOLATION
|
5
|
|
BugCheck 10E: VIDEO_MEMORY_MANAGEMENT_INTERNAL
|
5
|
|
BugCheck 8: IRQL_NOT_DISPATCH_LEVEL
|
4
|
|
BugCheck 18: REFERENCE_BY_POINTER
|
4
|
|
BugCheck 34: CACHE_MANAGER
|
4
|
|
BugCheck 76: PROCESS_HAS_LOCKED_PAGES
|
4
|
|
BugCheck CA: PNP_DETECTED_FATAL_ERROR
|
4
|
|
BugCheck CB: DRIVER_LEFT_LOCKED_PAGES_IN_PROCESS
|
4
|
|
BugCheck D2: BUGCODE_ID_DRIVER
|
4
|
|
BugCheck D4: SYSTEM_SCAN_AT_RAISED_IRQL_CAUGHT_IMPROPER_DRIVER_UNLOAD
|
4
|
|
BugCheck D9: LOCKED_PAGES_TRACKER_CORRUPTION
|
4
|
|
BugCheck F7: DRIVER_OVERRAN_STACK_BUFFER
|
4
|
|
BugCheck 101: CLOCK_WATCHDOG_TIMEOUT
|
4
|
|
BugCheck C0000218: STATUS_CANNOT_LOAD_REGISTRY_FILE
|
4
|
|
BugCheck 7: INVALID_SOFTWARE_INTERRUPT
|
3
|
|
BugCheck 13: EMPTY_THREAD_REAPER_LIST
|
3
|
|
BugCheck 14: CREATE_DELETE_LOCK_NOT_LOCKED
|
3
|
|
BugCheck 22: FILE_SYSTEM
|
3
|
|
BugCheck 29: SECURITY_SYSTEM
|
3
|
|
BugCheck 39: SYSTEM_EXIT_OWNED_MUTEX
|
3
|
|
BugCheck 46: DEREF_UNKNOWN_LOGON_SESSION
|
3
|
|
BugCheck 4D: NO_PAGES_AVAILABLE
|
3
|
|
BugCheck 9E: USER_MODE_HEALTH_MONITOR
|
3
|
|
BugCheck BA: SESSION_HAS_VALID_VIEWS_ON_EXIT
|
3
|
|
BugCheck D3: DRIVER_PORTION_MUST_BE_NONPAGED
|
3
|
|
BugCheck D6: DRIVER_PAGE_FAULT_BEYOND_END_OF_ALLOCATION
|
3
|
|
BugCheck E7: INVALID_FLOATING_POINT_STATE
|
3
|
|
BugCheck 100: LOADER_BLOCK_MISMATCH
|
3
|
|
BugCheck 106: AGP_ILLEGALLY_REPROGRAMMED
|
3
|
|
BugCheck DEADDEAD: MANUALLY_INITIATED_CRASH1
|
3
|
|
BugCheck 10: SPIN_LOCK_NOT_OWNED
|
2
|
|
BugCheck 21: QUOTA_UNDERFLOW
|
2
|
|
BugCheck 26: CDFS_FILE_SYSTEM
|
2
|
|
BugCheck 30: SET_OF_INVALID_CONTEXT
|
2
|
|
BugCheck 33: UNEXPECTED_INITIALIZATION_CALL
|
2
|
|
BugCheck 36: DEVICE_REFERENCE_COUNT_NOT_ZERO
|
2
|
|
BugCheck 37: FLOPPY_INTERNAL_ERROR
|
2
|
|
BugCheck 40: TARGET_MDL_TOO_SMALL
|
2
|
|
BugCheck 42: ATDISK_DRIVER_INTERNAL
|
2
|
|
BugCheck 4A: IRQL_GT_ZERO_AT_SYSTEM_SERVICE
|
2
|
|
BugCheck 72: ASSIGN_DRIVE_LETTERS_FAILED
|
2
|
|
BugCheck 73: CONFIG_LIST_FAILED
|
2
|
|
BugCheck CD: PAGE_FAULT_BEYOND_END_OF_ALLOCATION
|
2
|
|
BugCheck CF: TERMINAL_SERVER_DRIVER_MADE_INCORRECT_MEMORY_REFERENCE
|
2
|
|
BugCheck E4: WORKER_INVALID
|
2
|
|
BugCheck 104: AGP_INVALID_ACCESS
|
2
|
|
BugCheck 15: LAST_CHANCE_CALLED_FROM_KMODE
|
1
|
|
BugCheck 16: CID_HANDLE_CREATION
|
1
|
|
BugCheck 17: CID_HANDLE_DELETION
|
1
|
|
BugCheck 28: CORRUPT_ACCESS_TOKEN
|
1
|
|
BugCheck 38: SERIAL_DRIVER_INTERNAL
|
1
|
|
BugCheck 43: NO_SUCH_PARTITION
|
1
|
|
BugCheck 45: INSUFFICIENT_SYSTEM_MAP_REGS
|
1
|
|
BugCheck 48: CANCEL_STATE_IN_COMPLETED_IRP
|
1
|
|
BugCheck 49: PAGE_FAULT_WITH_INTERRUPTS_OFF
|
1
|
|
BugCheck 57: XNS_INTERNAL_ERROR
|
1
|
|
BugCheck 58: FTDISK_INTERNAL_ERROR
|
1
|
|
BugCheck 5C: HAL_INITIALIZATION_FAILED
|
1
|
|
BugCheck 60: PROCESS_INITIALIZATION_FAILED
|
1
|
|
BugCheck 62: OBJECT1_INITIALIZATION_FAILED
|
1
|
|
BugCheck 63: SECURITY1_INITIALIZATION_FAILED
|
1
|
|
BugCheck 64: SYMBOLIC_INITIALIZATION_FAILED
|
1
|
|
BugCheck 67: CONFIG_INITIALIZATION_FAILED
|
1
|
|
BugCheck 68: FILE_INITIALIZATION_FAILED
|
1
|
|
BugCheck 70: SESSION4_INITIALIZATION_FAILED
|
1
|
|
BugCheck 74: BAD_SYSTEM_CONFIG_INFO
|
1
|
|
BugCheck 75: CANNOT_WRITE_CONFIGURATION
|
1
|
|
BugCheck 79: MISMATCHED_HAL
|
1
|
|
BugCheck 7D: INSTALL_MORE_MEMORY
|
1
|
|
BugCheck 80: NMI_HARDWARE_FAILURE
|
1
|
|
BugCheck 82: DFS_FILE_SYSTEM
|
1
|
|
BugCheck 85: SETUP_FAILURE
|
1
|
|
BugCheck 99: INVALID_REGION_OR_SEGMENT
|
1
|
|
BugCheck A1: PCI_BUS_DRIVER_INTERNAL
|
1
|
|
BugCheck BF: MUTEX_ALREADY_OWNED
|
1
|
|
BugCheck CC: PAGE_FAULT_IN_FREED_SPECIAL_POOL
|
1
|
|
BugCheck DB: DRIVER_CORRUPTED_SYSPTES
|
1
|
|
BugCheck E8: INVALID_CANCEL_OF_FILE_OPEN
|
1
|
|
BugCheck ED: UNMOUNTABLE_BOOT_VOLUME
|
1
|
|
BugCheck FD: DIRTY_NOWRITE_PAGES_CONGESTION
|
1
|
|
BugCheck 108: THIRD_PARTY_FILE_SYSTEM_FAILURE
|
1
|
|
BugCheck 111: RECURSIVE_NMI
|
1
|
|
BugCheck 121: DRIVER_VIOLATION
|
1
|
|
BugCheck 122: WHEA_INTERNAL_ERROR
|
1
|
|
BugCheck 1B: PFN_SHARE_COUNT
|
0
|
|
BugCheck 1C: PFN_REFERENCE_COUNT
|
0
|
|
BugCheck 1D: NO_SPIN_LOCK_AVAILABLE
|
0
|
|
BugCheck 1F: SHARED_RESOURCE_CONV_ERROR
|
0
|
|
BugCheck 25: NPFS_FILE_SYSTEM
|
0
|
|
BugCheck 2A: INCONSISTENT_IRP
|
0
|
|
BugCheck 2B: PANIC_STACK_SWITCH
|
0
|
|
BugCheck 2C: PORT_DRIVER_INTERNAL
|
0
|
|
BugCheck 2D: SCSI_DISK_DRIVER_INTERNAL
|
0
|
|
BugCheck 2E: DATA_BUS_ERROR
|
0
|
|
BugCheck 2F: INSTRUCTION_BUS_ERROR
|
0
|
|
BugCheck 31: PHASE0_INITIALIZATION_FAILED
|
0
|
|
BugCheck 32: PHASE1_INITIALIZATION_FAILED
|
0
|
|
BugCheck 3A: SYSTEM_UNWIND_PREVIOUS_USER
|
0
|
|
BugCheck 3C: INTERRUPT_UNWIND_ATTEMPTED
|
0
|
|
BugCheck 3D: INTERRUPT_EXCEPTION_NOT_HANDLED
|
0
|
|
BugCheck 3E: MULTIPROCESSOR_CONFIGURATION_NOT_SUPPORTED
|
0
|
|
BugCheck 47: REF_UNKNOWN_LOGON_SESSION
|
0
|
|
BugCheck 4B: STREAMS_INTERNAL_ERROR
|
0
|
|
BugCheck 4C: FATAL_UNHANDLED_HARD_ERROR
|
0
|
|
BugCheck 4F: NDIS_INTERNAL_ERROR
|
0
|
|
BugCheck 52: MAILSLOT_FILE_SYSTEM
|
0
|
|
BugCheck 53: NO_BOOT_DEVICE
|
0
|
|
BugCheck 54: LM_SERVER_INTERNAL_ERROR
|
0
|
|
BugCheck 55: DATA_COHERENCY_EXCEPTION
|
0
|
|
BugCheck 56: INSTRUCTION_COHERENCY_EXCEPTION
|
0
|
|
BugCheck 59: PINBALL_FILE_SYSTEM
|
0
|
|
BugCheck 5A: CRITICAL_SERVICE_FAILED
|
0
|
|
BugCheck 5B: SET_ENV_VAR_FAILED
|
0
|
|
BugCheck 5D: UNSUPPORTED_PROCESSOR
|
0
|
|
BugCheck 5E: OBJECT_INITIALIZATION_FAILED
|
0
|
|
BugCheck 5F: SECURITY_INITIALIZATION_FAILED
|
0
|
|
BugCheck 61: HAL1_INITIALIZATION_FAILED
|
0
|
|
BugCheck 65: MEMORY1_INITIALIZATION_FAILED
|
0
|
|
BugCheck 66: CACHE_INITIALIZATION_FAILED
|
0
|
|
BugCheck 69: IO1_INITIALIZATION_FAILED
|
0
|
|
BugCheck 6A: LPC_INITIALIZATION_FAILED
|
0
|
|
BugCheck 6C: REFMON_INITIALIZATION_FAILED
|
0
|
|
BugCheck 6D: SESSION1_INITIALIZATION_FAILED
|
0
|
|
BugCheck 6E: SESSION2_INITIALIZATION_FAILED
|
0
|
|
BugCheck 6F: SESSION3_INITIALIZATION_FAILED
|
0
|
|
BugCheck 71: SESSION5_INITIALIZATION_FAILED
|
0
|
|
BugCheck 78: PHASE0_EXCEPTION
|
0
|
|
BugCheck 7C: BUGCODE_NDIS_DRIVER
|
0
|
|
BugCheck 81: SPIN_LOCK_INIT_FAILURE
|
0
|
|
BugCheck 8B: MBR_CHECKSUM_MISMATCH
|
0
|
|
BugCheck 8F: PP0_INITIALIZATION_FAILED
|
0
|
|
BugCheck 90: PP1_INITIALIZATION_FAILED
|
0
|
|
BugCheck 92: UP_DRIVER_ON_MP_SYSTEM
|
0
|
|
BugCheck 94: KERNEL_STACK_LOCKED_AT_EXIT
|
0
|
|
BugCheck 97: BOUND_IMAGE_UNSUPPORTED
|
0
|
|
BugCheck 98: END_OF_NT_EVALUATION_PERIOD
|
0
|
|
BugCheck 9A: SYSTEM_LICENSE_VIOLATION
|
0
|
|
BugCheck 9B: UDFS_FILE_SYSTEM
|
0
|
|
BugCheck A2: MEMORY_IMAGE_CORRUPT
|
0
|
|
BugCheck A3: ACPI_DRIVER_INTERNAL
|
0
|
|
BugCheck A4: CNSS_FILE_SYSTEM_FILTER
|
0
|
|
BugCheck A5: ACPI_BIOS_ERROR
|
0
|
|
BugCheck A7: BAD_EXHANDLE
|
0
|
|
BugCheck AC: HAL_MEMORY_ALLOCATION
|
0
|
|
BugCheck AD: VIDEO_DRIVER_DEBUG_REPORT_REQUEST
|
0
|
|
BugCheck B4: VIDEO_DRIVER_INIT_FAILURE
|
0
|
|
BugCheck B9: CHIPSET_DETECTED_ERROR
|
0
|
|
BugCheck BB: NETWORK_BOOT_INITIALIZATION_FAILED
|
0
|
|
BugCheck BC: NETWORK_BOOT_DUPLICATE_ADDRESS
|
0
|
|
BugCheck C6: DRIVER_CAUGHT_MODIFYING_FREED_POOL
|
0
|
|
BugCheck C7: TIMER_OR_DPC_INVALID
|
0
|
|
BugCheck C8: IRQL_UNEXPECTED_VALUE
|
0
|
|
BugCheck D7: DRIVER_UNMAPPING_INVALID_VIEW
|
0
|
|
BugCheck D8: DRIVER_USED_EXCESSIVE_PTES
|
0
|
|
BugCheck DC: DRIVER_INVALID_STACK_ACCESS
|
0
|
|
BugCheck DF: IMPERSONATING_WORKER_THREAD
|
0
|
|
BugCheck E0: ACPI_BIOS_FATAL_ERROR
|
0
|
|
BugCheck E9: ACTIVE_EX_WORKER_THREAD_TERMINATION
|
0
|
|
BugCheck EB: DIRTY_MAPPED_PAGES_CONGESTION
|
0
|
|
BugCheck EC: SESSION_HAS_VALID_SPECIAL_POOL_ON_EXIT
|
0
|
|
BugCheck EF: CRITICAL_PROCESS_DIED
|
0
|
|
BugCheck F1: SCSI_VERIFIER_DETECTED_VIOLATION
|
0
|
|
BugCheck F3: DISORDERLY_SHUTDOWN
|
0
|
|
BugCheck F5: FLTMGR_FILE_SYSTEM
|
0
|
|
BugCheck F6: PCI_VERIFIER_DETECTED_VIOLATION
|
0
|
|
BugCheck F8: RAMDISK_BOOT_INITIALIZATION_FAILED
|
0
|
|
BugCheck F9: DRIVER_RETURNED_STATUS_REPARSE_FOR_VOLUME_OPEN
|
0
|
|
BugCheck FA: HTTP_DRIVER_CORRUPTED
|
0
|
|
BugCheck FF: RESERVE_QUEUE_OVERFLOW
|
0
|
|
BugCheck 105: AGP_GART_CORRUPTION
|
0
|
|
BugCheck 10A: APP_TAGGING_INITIALIZATION_FAILED
|
0
|
|
BugCheck 10C: FSRTL_EXTRA_CREATE_PARAMETER_VIOLATION
|
0
|
|
BugCheck 10F: RESOURCE_MANAGER_EXCEPTION_NOT_HANDLED
|
0
|
|
BugCheck 112: MSRPC_STATE_VIOLATION
|
0
|
|
BugCheck 113: VIDEO_DXGKRNL_FATAL_ERROR
|
0
|
|
BugCheck 114: VIDEO_SHADOW_DRIVER_FATAL_ERROR
|
0
|
|
BugCheck 115: AGP_INTERNAL
|
0
|
|
BugCheck 119: VIDEO_SCHEDULER_INTERNAL_ERROR
|
0
|
|
BugCheck 11A: EM_INITIALIZATION_FAILURE
|
0
|
|
BugCheck 11B: DRIVER_RETURNED_HOLDING_CANCEL_LOCK
|
0
|
|
BugCheck 11C: ATTEMPTED_WRITE_TO_CM_PROTECTED_STORAGE
|
0
|
|
BugCheck 11D: EVENT_TRACING_FATAL_ERROR
|
0
|
|
BugCheck 127: PAGE_NOT_ZERO
|
0
|
|
BugCheck 12B: FAULTY_HARDWARE_CORRUPTED_PAGE
|
0
|
|
BugCheck 12C: EXFAT_FILE_SYSTEM
|
0
|
|
BugCheck C0000221: STATUS_IMAGE_CHECKSUM_MISMATCH
|
0
|