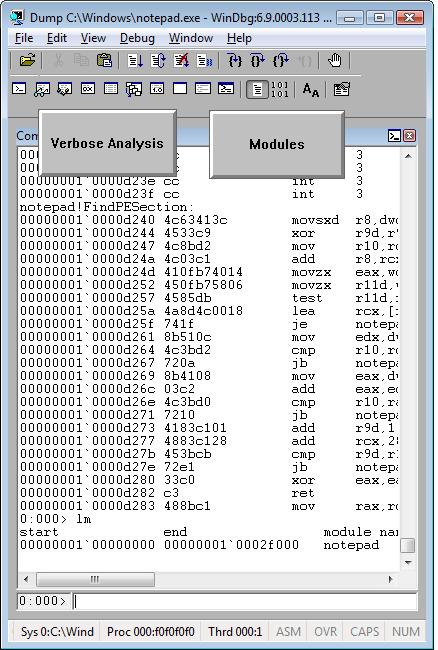
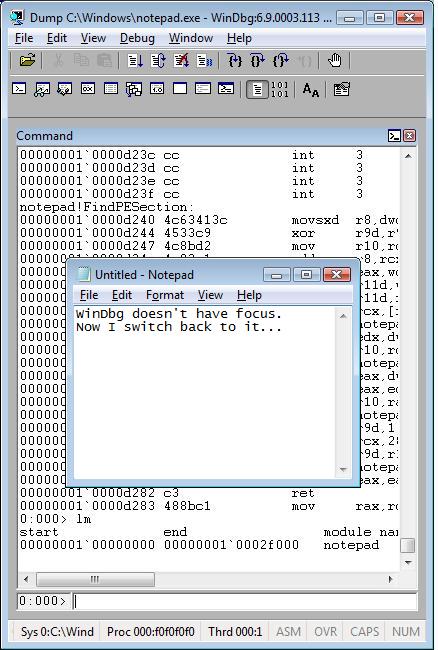
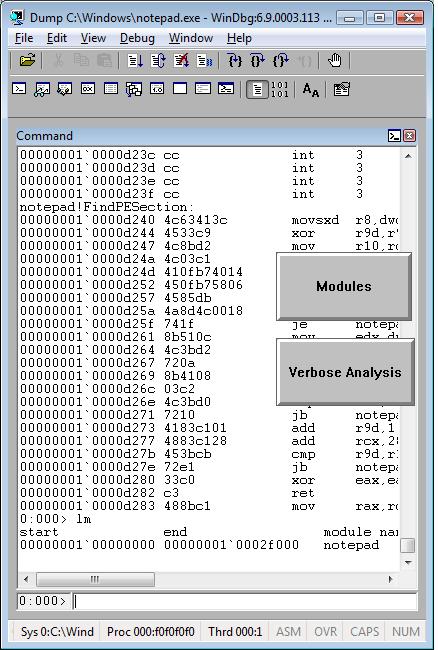
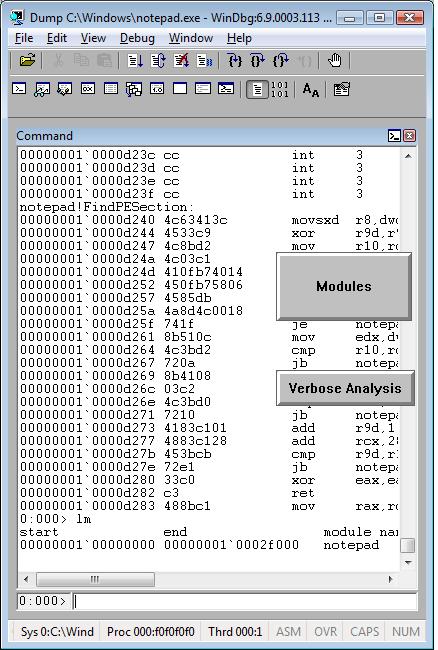
I needed to quickly check preferred load address for one DLL and recalled that I once used WinDbg as a binary editor. So I loaded that DLL as a crash dump:
Loading Dump File [C:\kktools\userdump8.1\x64\usrxcptn.dll]
Symbol search path is: srv*c:\mss*http://msdl.microsoft.com/download/symbols
Executable search path is:
ModLoad: 00000000`00400000 00000000`00406000 C:\kktools\userdump8.1\x64\usrxcptn.dll
usrxcptn!DllMainCRTStartupForGS:
00000000`00401200 4883ec28 sub rsp,28h
0:000> lm
start end module name
00000000`00400000 00000000`00406000 usrxcptn (pdb symbols) c:\mss\usrxcptn.pdb\[…]\usrxcptn.pdb
lm command already shows that but we can also check formatted PE headers as well:
0:000> !dh 00000000`00400000
File Type: DLL
FILE HEADER VALUES
8664 machine (X64)
5 number of sections
45825DE6 time date stamp Fri Dec 15 08:33:42 2006
0 file pointer to symbol table
0 number of symbols
F0 size of optional header
2022 characteristics
Executable
App can handle >2gb addresses
DLL
OPTIONAL HEADER VALUES
20B magic #
8.00 linker version
E00 size of code
1200 size of initialized data
0 size of uninitialized data
1200 address of entry point
1000 base of code
----- new -----
0000000000400000 image base
1000 section alignment
200 file alignment
3 subsystem (Windows CUI)
5.02 operating system version
5.02 image version
5.02 subsystem version
6000 size of image
400 size of headers
DA18 checksum
0000000000040000 size of stack reserve
0000000000001000 size of stack commit
0000000000100000 size of heap reserve
0000000000001000 size of heap commit
1AB0 [ 213] address [size] of Export Directory
18B4 [ 3C] address [size] of Import Directory
4000 [ 418] address [size] of Resource Directory
3000 [ 48] address [size] of Exception Directory
1E00 [ 2580] address [size] of Security Directory
5000 [ 10] address [size] of Base Relocation Directory
1080 [ 1C] address [size] of Debug Directory
0 [ 0] address [size] of Description Directory
0 [ 0] address [size] of Special Directory
0 [ 0] address [size] of Thread Storage Directory
0 [ 0] address [size] of Load Configuration Directory
0 [ 0] address [size] of Bound Import Directory
1000 [ 78] address [size] of Import Address Table Directory
0 [ 0] address [size] of Delay Import Directory
0 [ 0] address [size] of COR20 Header Directory
0 [ 0] address [size] of Reserved Directory
SECTION HEADER #1
.text name
CC3 virtual size
1000 virtual address
E00 size of raw data
400 file pointer to raw data
0 file pointer to relocation table
0 file pointer to line numbers
0 number of relocations
0 number of line numbers
60000020 flags
Code
(no align specified)
Execute Read
Debug Directories(1)
Type Size Address Pointer
cv 25 10b0 4b0 Format: RSDS, guid, 1, usrxcptn.pdb
SECTION HEADER #2
.data name
744 virtual size
2000 virtual address
200 size of raw data
1200 file pointer to raw data
0 file pointer to relocation table
0 file pointer to line numbers
0 number of relocations
0 number of line numbers
C0000040 flags
Initialized Data
(no align specified)
Read Write
SECTION HEADER #3
.pdata name
48 virtual size
3000 virtual address
200 size of raw data
1400 file pointer to raw data
0 file pointer to relocation table
0 file pointer to line numbers
0 number of relocations
0 number of line numbers
40000040 flags
Initialized Data
(no align specified)
Read Only
SECTION HEADER #4
.rsrc name
418 virtual size
4000 virtual address
600 size of raw data
1600 file pointer to raw data
0 file pointer to relocation table
0 file pointer to line numbers
0 number of relocations
0 number of line numbers
40000040 flags
Initialized Data
(no align specified)
Read Only
SECTION HEADER #5
.reloc name
34 virtual size
5000 virtual address
200 size of raw data
1C00 file pointer to raw data
0 file pointer to relocation table
0 file pointer to line numbers
0 number of relocations
0 number of line numbers
42000040 flags
Initialized Data
Discardable
(no align specified)
Read Only
- Dmitry Vostokov @ DumpAnalysis.org -