Trace Analysis Patterns (Part 237)
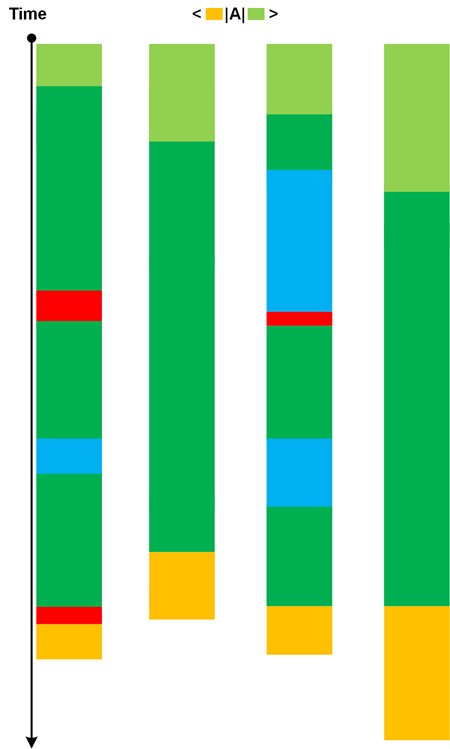
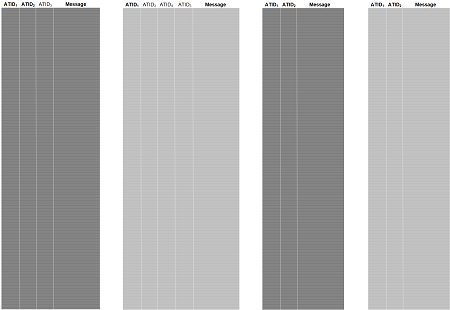
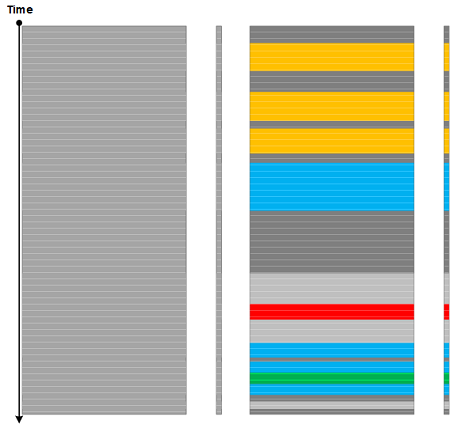
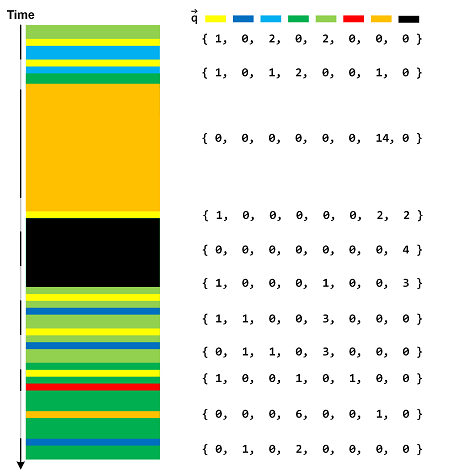
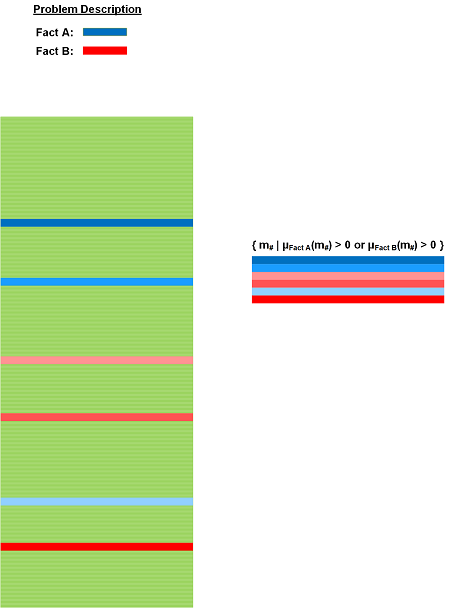
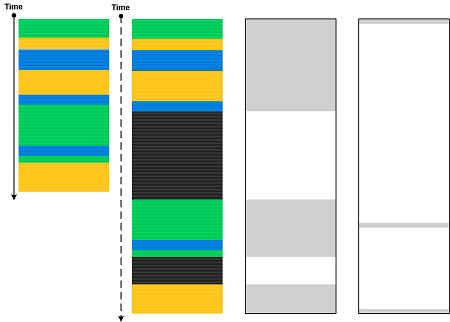
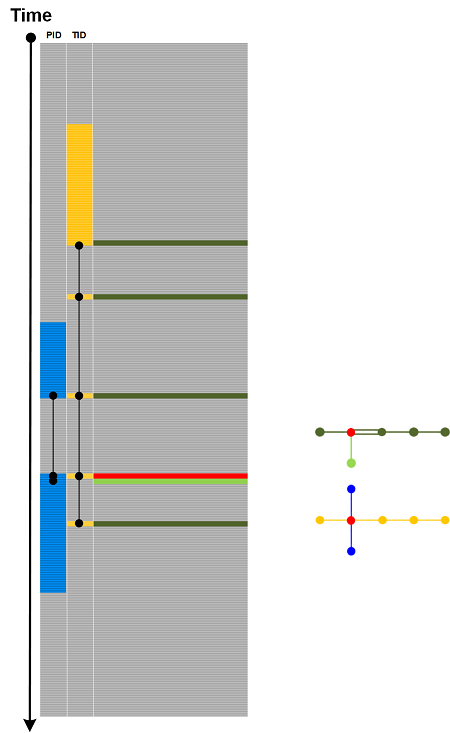
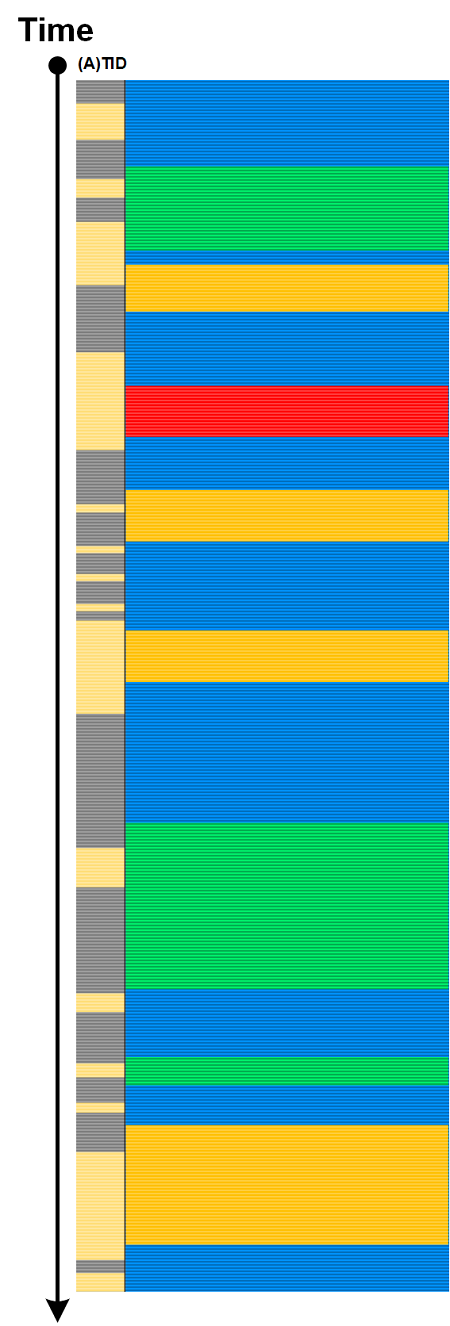
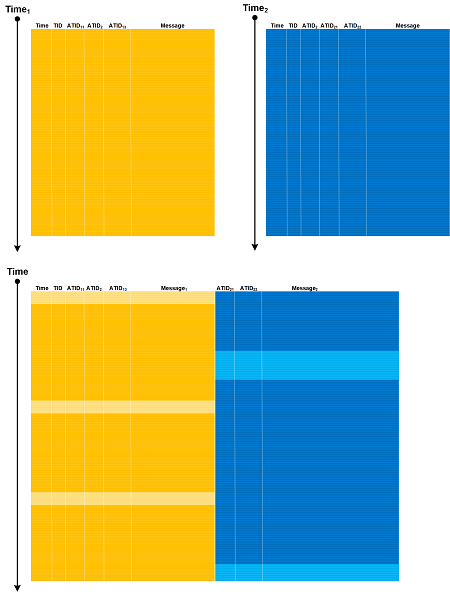
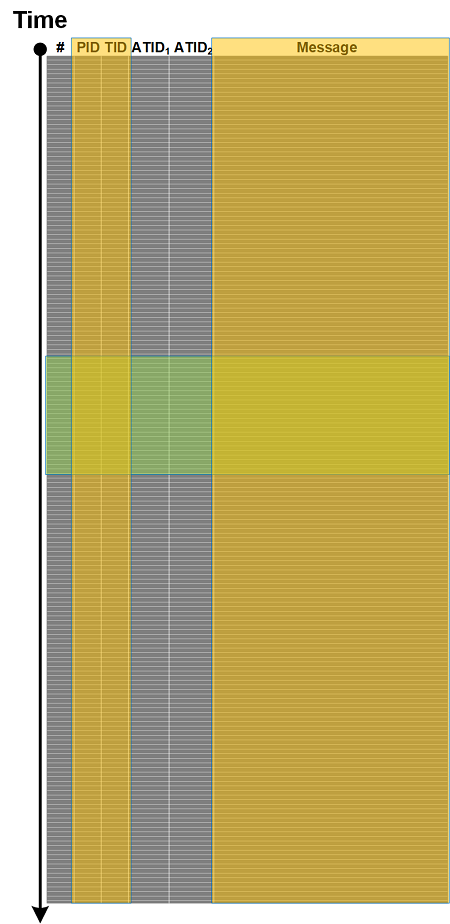
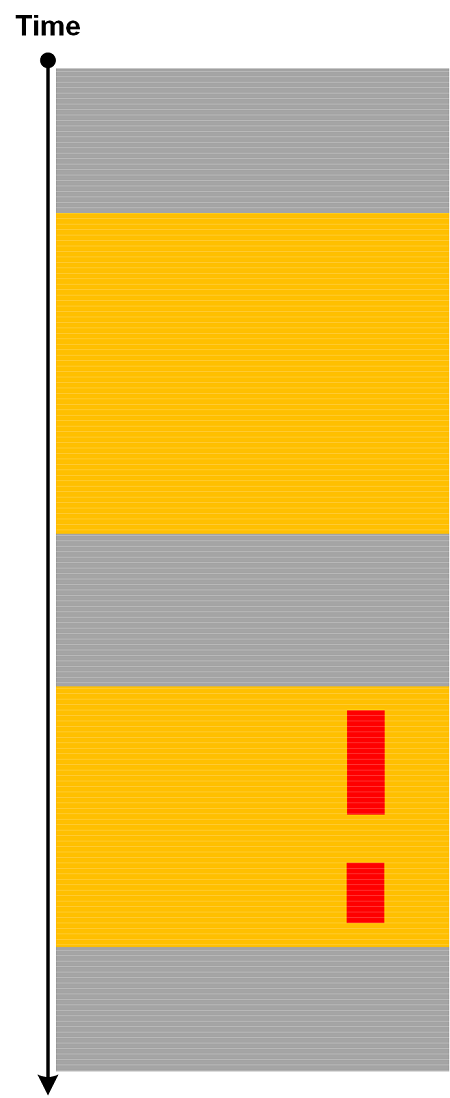
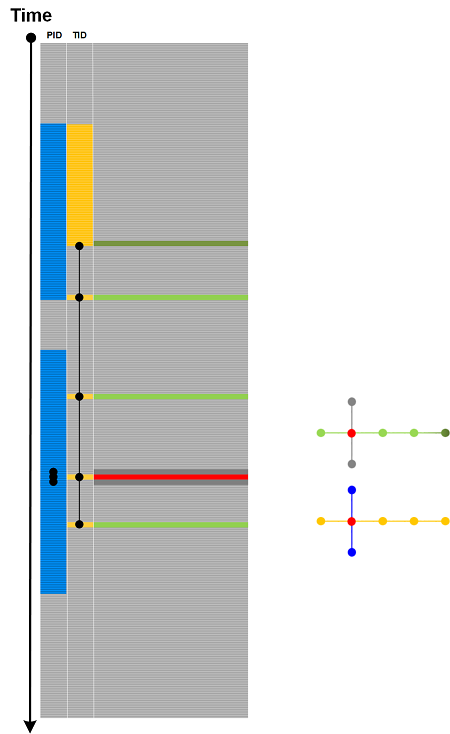
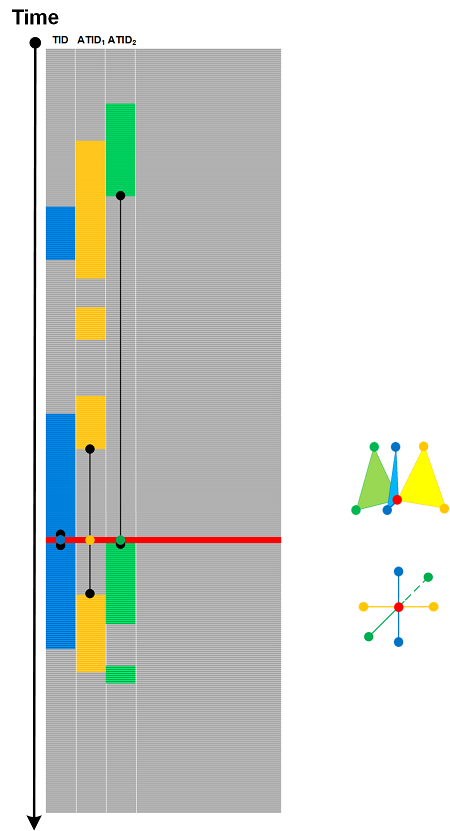
Saturday, November 18th, 2023How can we view traces and logs to facilitate there classification? One of the possible avenues is to view traces and logs consisting of the very large conceptual units, bricks, or bases to avoid combinatorial explosion. The natural candidates are Activity Region, Discontinuity, and Error Message or Exception Stack Trace Characteristic Message Block (Crash metaphor). So we have A, C, D, and we add B for Bad Activity Region whatever that means. For example, a typical trace that starts with some activity, then we have an exception stack trace belongs to AC Trace Class. Another trace that starts with some activity, then doesn’t show any messaged till the end can be classified as AD. A more elaborate class is ABCABCABCBC with periodicity of normal and bad activities culminating with error messages and finally with the last bad activity and exception. These three Trace Classes are depicted in the following diagram:
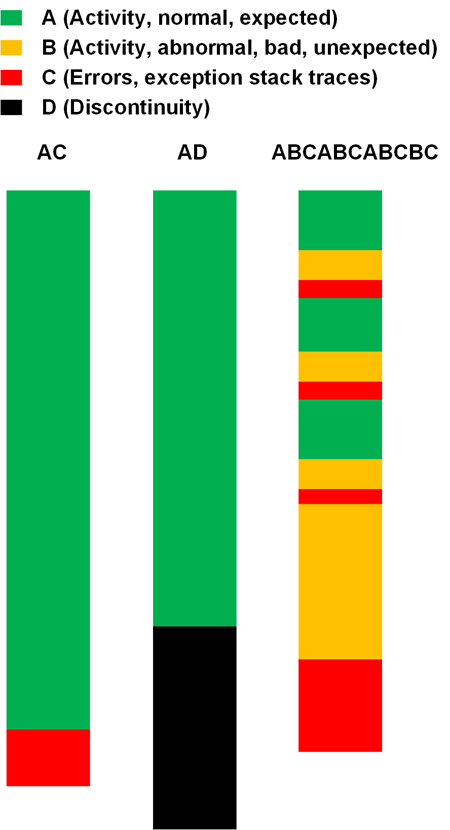
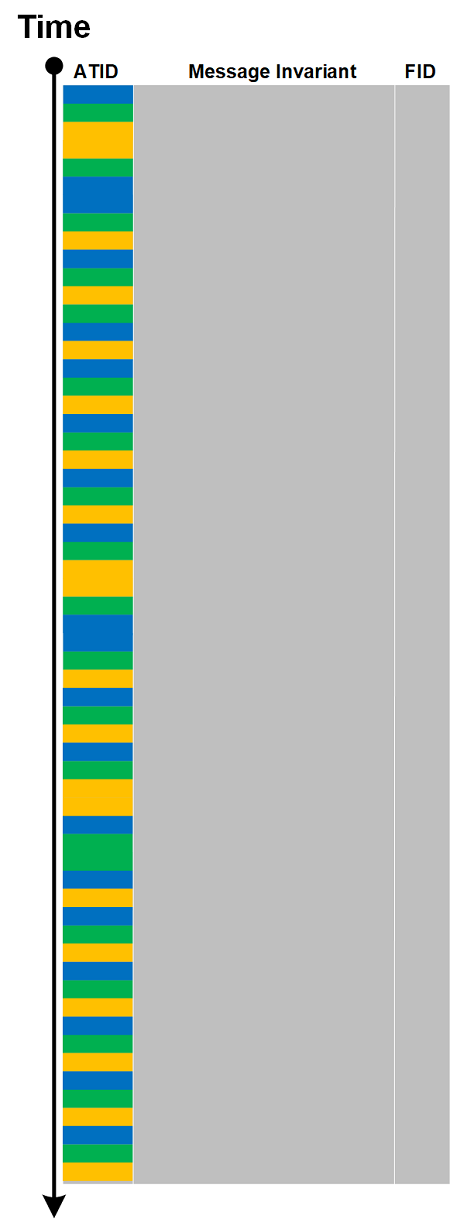
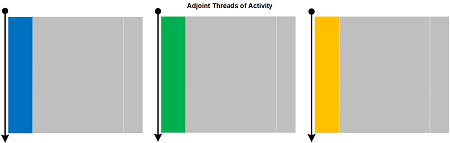
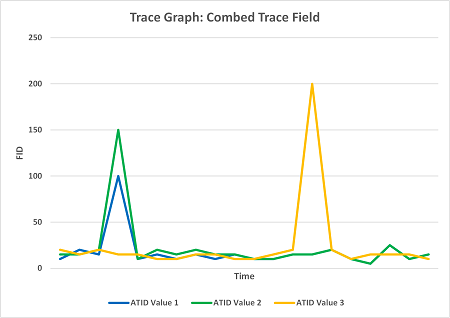
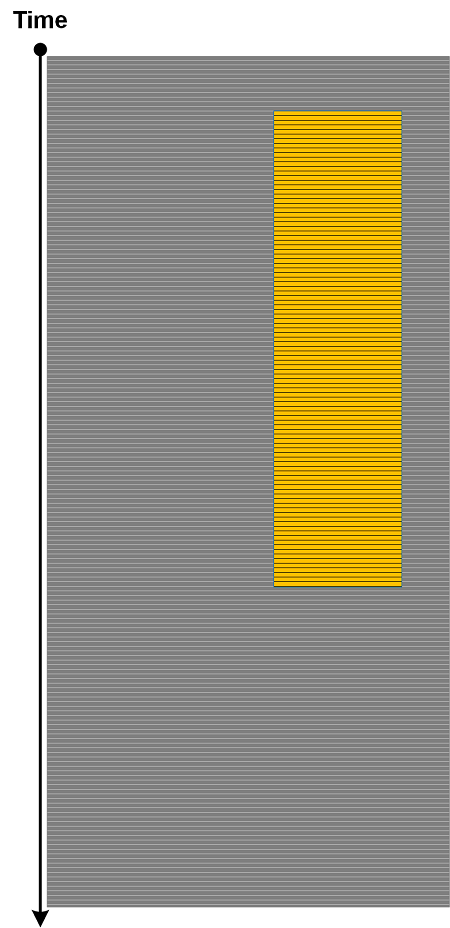
We combine sequences of the same bases into one, for example, AAAAA as just A, thus abstracting from semantic and syntactical differences between normal Activity Regions. The same is with other bases and can be considered as an extreme version of Quotient Trace. This classification can also be applied to individual Threads of Activity and Adjoint Threads of Activity.
This genetic-like description parallels the earlier proposal for DNA and RNA of Ruptured Computation.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -