Icons for Memory Dump Analysis Patterns (Part 19)
Wednesday, April 7th, 2010Today we introduce an icon for Incorrect Stack Trace pattern:
B/W
![]()
Color
![]()
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Today we introduce an icon for Incorrect Stack Trace pattern:
B/W
![]()
Color
![]()
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Crash Dump Analysis, Crash Dump Patterns, Debugging, Pattern Icons, Visual Dump Analysis | No Comments »
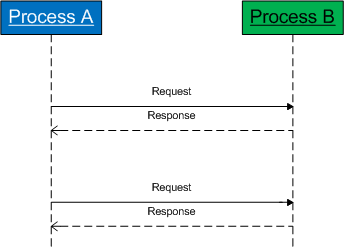
Previously introduced Coupled Processes pattern involves an active request (or an action) and an active wait for a response (or the action status):
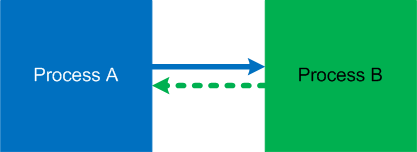
It is illustrated on this simple UML sequence diagram (process timeline represent collective request-response threads):
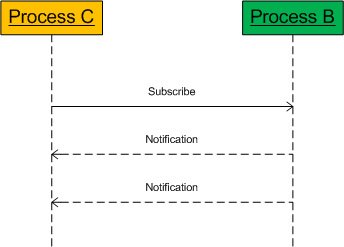
However, there is so called weak coupling when a process subscribes for notifications. Such threads most of the time are passive and processes are not blocked:

The coupling manifests itself when notifier threads start spiking CPU and bring their share of CPU consumption to the notified threads:
Here is an example of such threads from the forthcoming pattern interaction case study:
5 Id: 61018.dbec Suspend: 1 Teb: 7ffae000 Unfrozen
ChildEBP RetAddr
01e3fa68 7c82787b ntdll!KiFastSystemCallRet
01e3fa6c 77c80a6e ntdll!NtRequestWaitReplyPort+0xc
01e3fab8 77c7fcf0 rpcrt4!LRPC_CCALL::SendReceive+0x230
01e3fac4 77c80673 rpcrt4!I_RpcSendReceive+0x24
01e3fad8 77ce315a rpcrt4!NdrSendReceive+0x2b
01e3fec0 771f4fbd rpcrt4!NdrClientCall2+0x22e
01e3fed8 771f4f60 winsta!RpcWinStationWaitSystemEvent+0x1c
01e3ff20 6582116c winsta!WinStationWaitSystemEvent+0x51
[...]
01e3ffec 00000000 kernel32!BaseThreadStart+0x34
In cases of synchronous notifications if a notified thread is blocked we have an instance of a reversed strong coupling.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Crash Dump Analysis, Crash Dump Patterns, Debugging | 3 Comments »
Software Diagnostics Library is proudly powered by
WordPress
Entries (RSS)
and Comments (RSS).