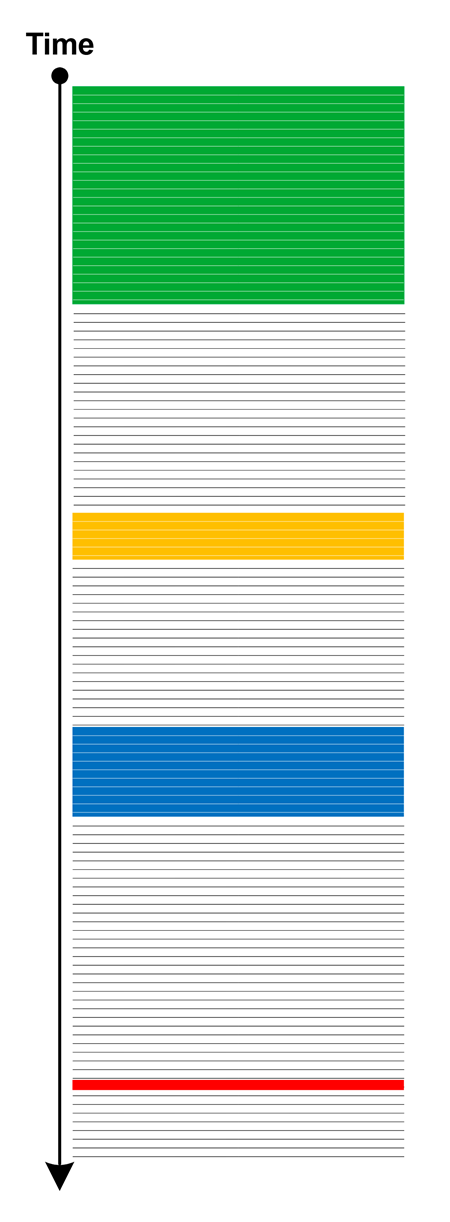
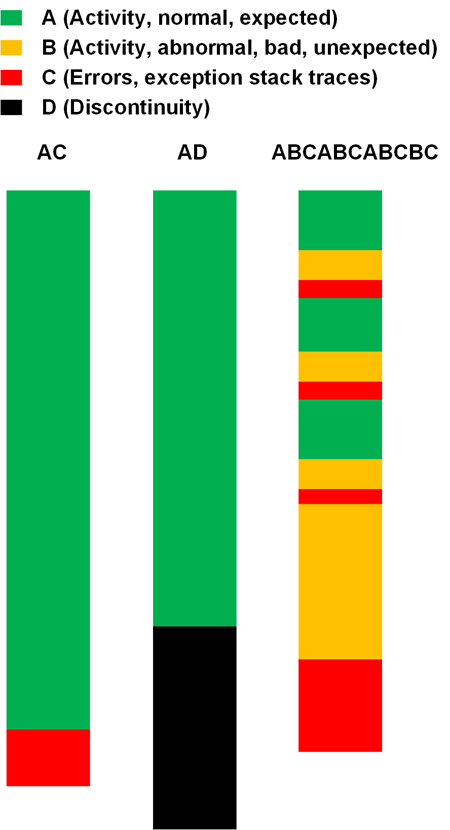
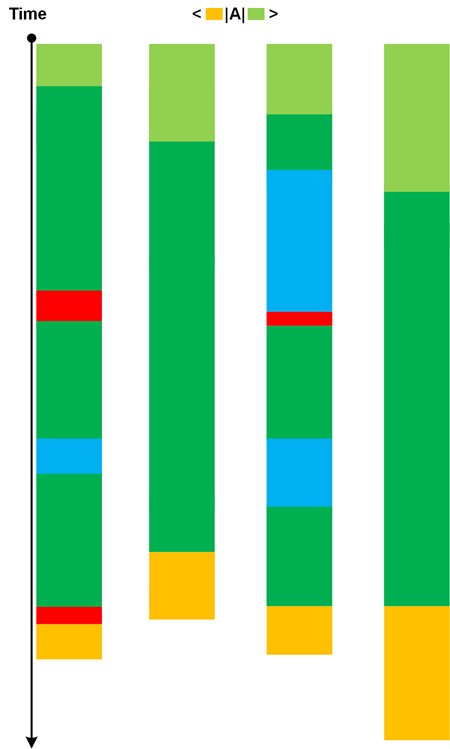
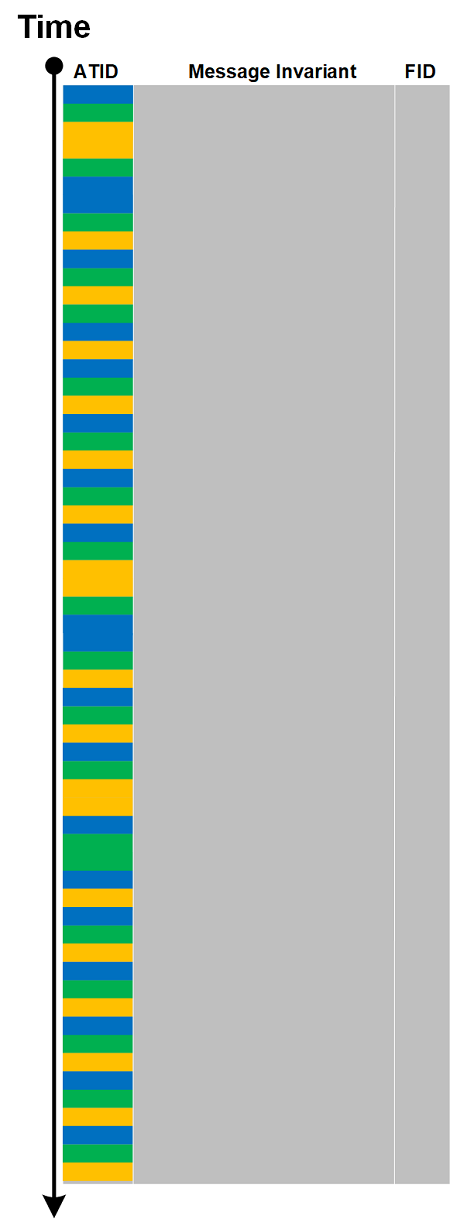
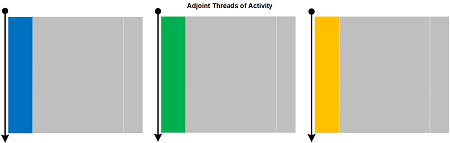
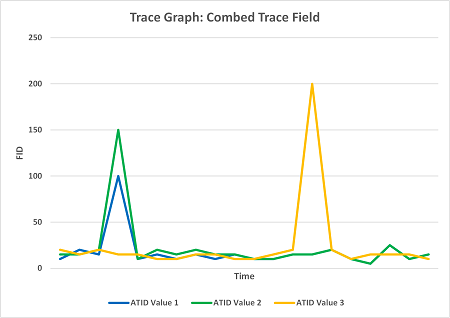
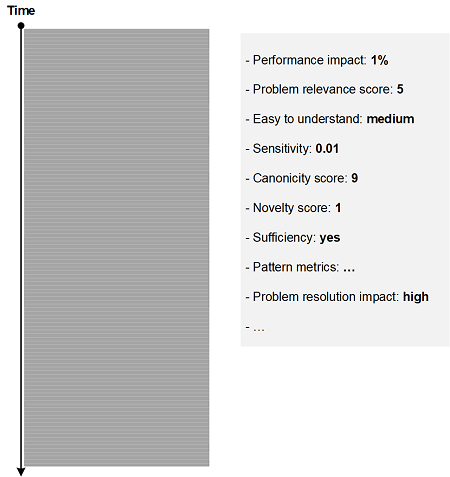
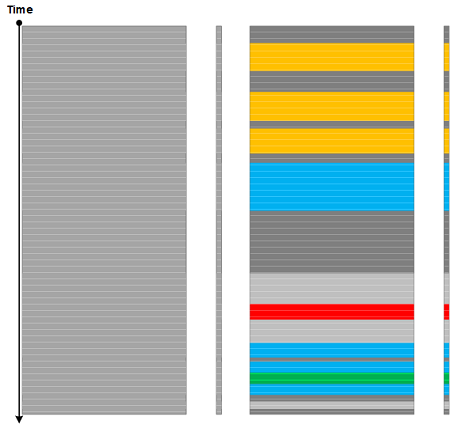
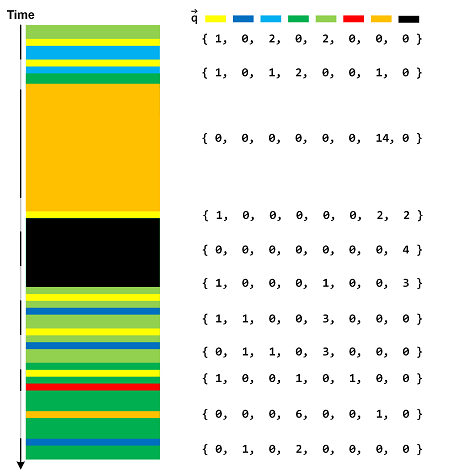
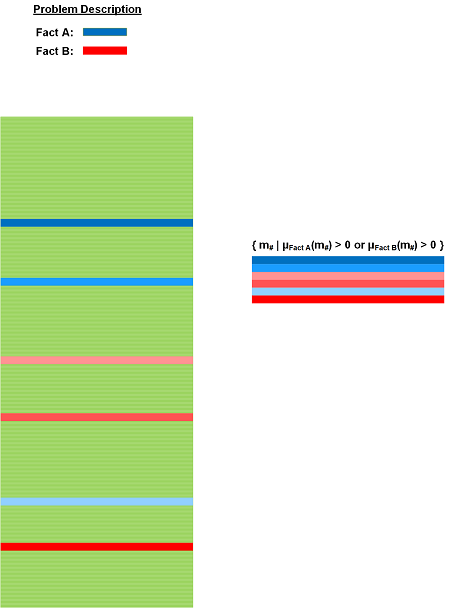
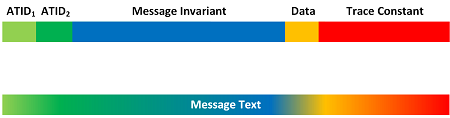
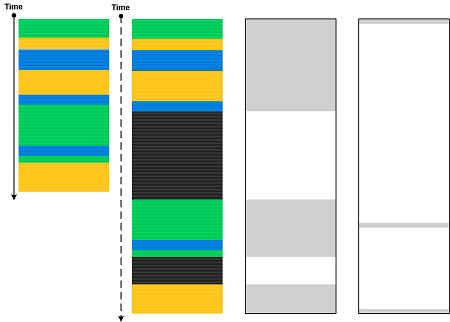
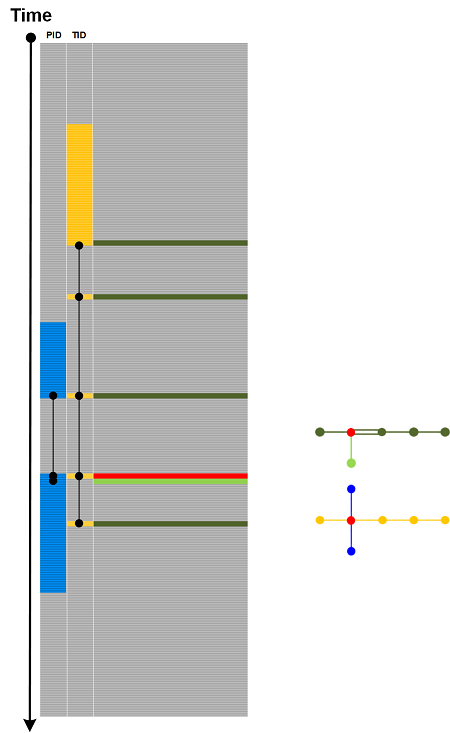
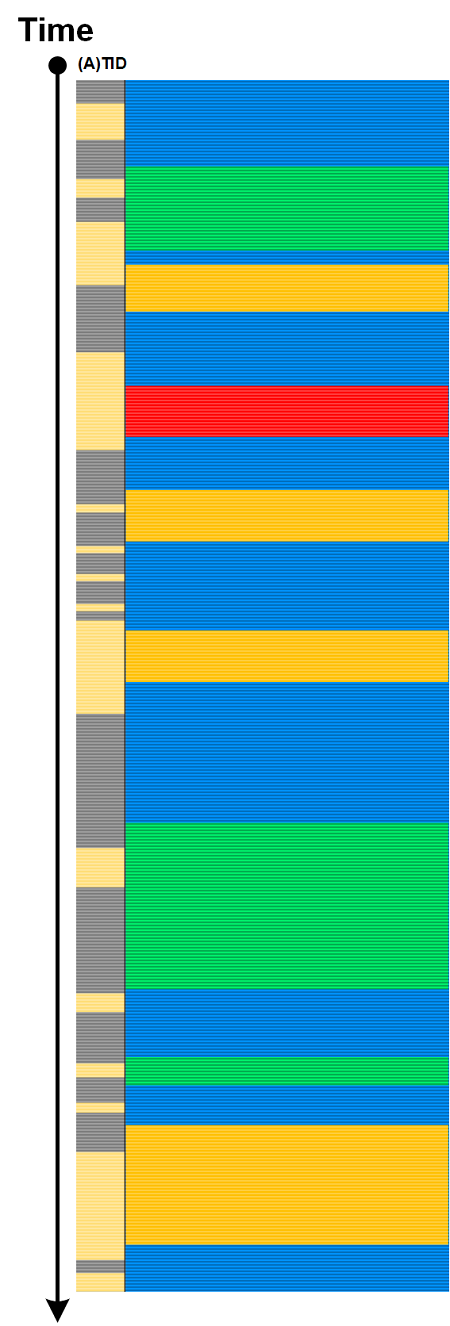
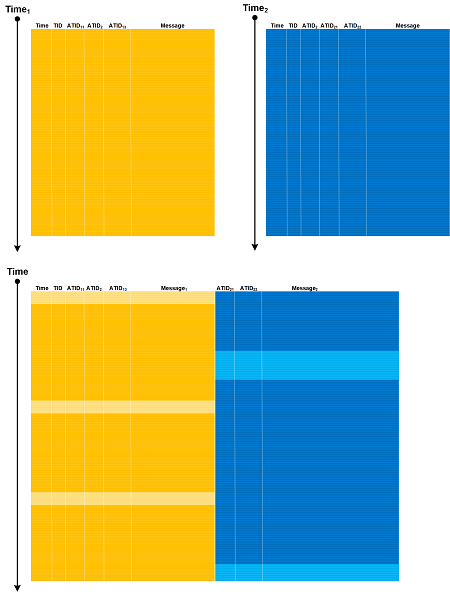
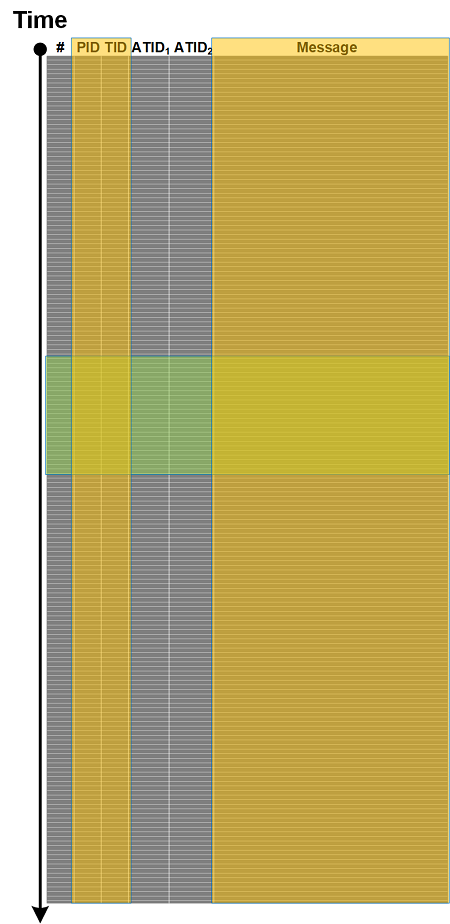
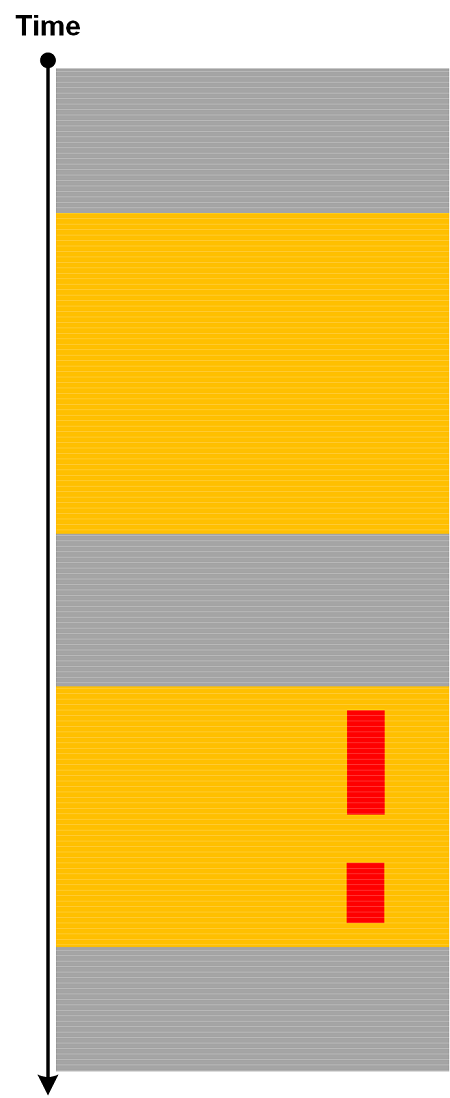
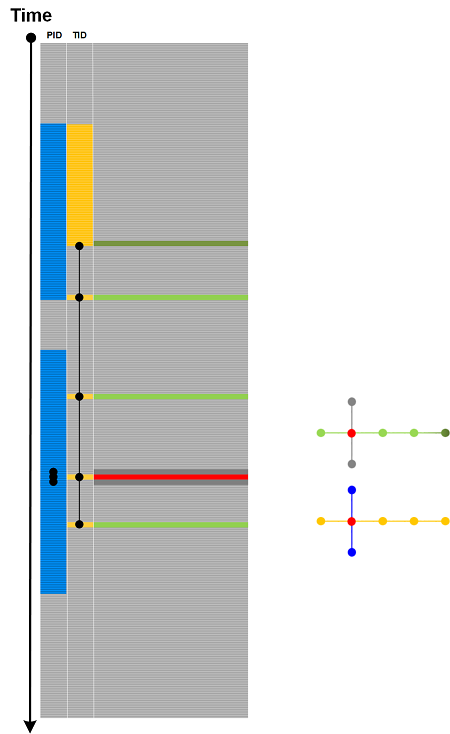
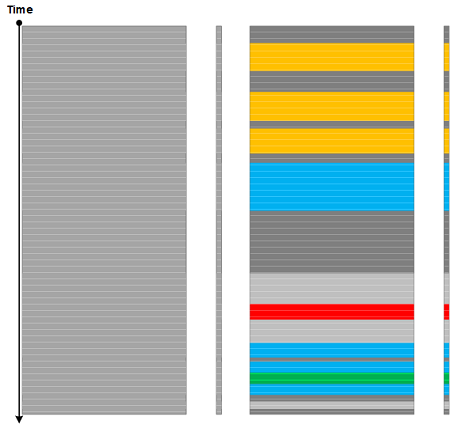
Most trace and log diagrams we use for analysis pattern illustration are 1-dimensional if we ignore the structure of individual trace messages despite being looking as 2-dimensional. It is, therefore, natural to consider them as periodic and aperiodic tessellations of a line using a set of segments of different lengths and colors. A Trace Tessellation analysis pattern is such an arrangement based on some criteria, for example, a combination of trace and log analysis patterns or simply some A(TID) mapping.
GPT-4 suggests the following outline for 1-dimensional tessellation:
Tessellating a one-dimensional space like a line is fundamentally simpler than tessellating a two-dimensional space. Given that a line segment is the only basic shape you can use to tessellate a line, at first glance, it may seem there isn’t much room for diverse or “interesting” patterns. However, we can introduce variability by considering the following:
Varying Lengths: Instead of using uniform line segments, use segments of varying lengths. For instance, alternating between short and long segments can create a rhythmic pattern.
Color or Texture Variations: Even though it’s a one-dimensional space, you can vary colors or textures. For example, alternate between black and white line segments.
Spacing: While traditional tessellation has no gaps, you could introduce regular or irregular spacing between line segments for a more abstract approach.
Pattern Interruption: Repeating a set pattern and then deliberately interrupting it can be visually interesting. For instance, having three short segments followed by one long segment, and then repeating.
Associative Representation: You can use tessellated patterns on a line to represent data or other concepts. For example, Morse code uses a combination of short (”dots”) and long (”dashes”) signals, essentially tessellating a line with two types of segments to convey information.
Fractals and Recursive Patterns: While not “tessellation” in the traditional sense, you can create patterns on a line using recursive rules. The Cantor set is an example of this, where you take a line segment, remove the middle third, and then repeat the process for the remaining segments ad infinitum.
These are just a few ways to introduce interest and complexity into the “tessellation” of a one-dimensional space. While it’s fundamentally simpler than two-dimensional tessellation, with some creativity, you can still achieve intriguing and meaningful patterns.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -