Archive for the ‘Software Trace Analysis’ Category
Saturday, November 9th, 2013
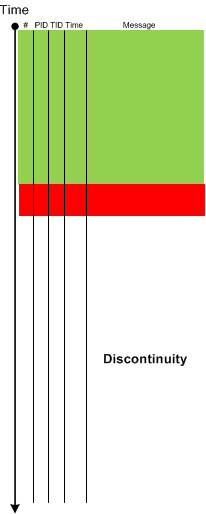
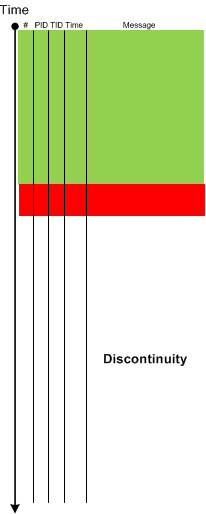
When analysing Inter-Correlation or Intra-Correlation and finding Discontinuities in one part or in a different trace (for example, in client-server environments) it is useful to see if there are corresponding Correlated Discontinuities in another part of the same trace (for example, a different Thread of Activity) or in a different trace. Such pattern may point to the underlying communication problem and may suggest to gather a different trace (for example, a network trace) for further analysis.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Network Trace Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Monday, August 19th, 2013
While working on Mobile Software Diagnostics webinar and exploring the richness of Android platform and similarity of its LogCat traces (Eclipse representation) to Minimal Trace Graphs (see a corresponding slide in trace analysis pattern reference) we recognized the time has come to provide a Java implementation for a general software narratological pattern-oriented trace analysis approach and also see what memory analysis patterns can also be applied there. Here by implementation we mean concrete platform examples. For example, in the past we did similar implementations of memory analysis patterns (originally developed for unmanaged and native Windows code) for .NET (WinDbg) and Mac OS X (GDB). The first trace analysis pattern we cover here is very obvious and simple and is called Exception Stack Trace. In the original pattern example a stack trace was inside a single trace message but can also be split such as each frame has its own message (date and time columns were removed for clarity):
E/AndroidRuntime(31416): java.lang.NullPointerException
E/AndroidRuntime(31416): at android.view.MotionEvent.writeToParcel(MotionEvent.java:1596)
E/AndroidRuntime(31416): at com.example.nullpointer.FullscreenActivity$1.onTouch(FullscreenActivity.java:139)
E/AndroidRuntime(31416): at android.view.View.dispatchTouchEvent(View.java:3881)
E/AndroidRuntime(31416): at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:869)
E/AndroidRuntime(31416): at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:869)
E/AndroidRuntime(31416): at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:869)
E/AndroidRuntime(31416): at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:869)
E/AndroidRuntime(31416): at android.view.ViewGroup.dispatchTouchEvent(ViewGroup.java:869)
E/AndroidRuntime(31416): at com.android.internal.policy.impl.PhoneWindow$DecorView. superDispatchTouchEvent(PhoneWindow.java:1750)
E/AndroidRuntime(31416): at com.android.internal.policy.impl.PhoneWindow. superDispatchTouchEvent(PhoneWindow.java:1135)
E/AndroidRuntime(31416): at android.app.Activity.dispatchTouchEvent(Activity.java:2096)
E/AndroidRuntime(31416): at com.android.internal.policy.impl.PhoneWindow$DecorView. dispatchTouchEvent(PhoneWindow.java:1734)
E/AndroidRuntime(31416): at android.view.ViewRoot.deliverPointerEvent(ViewRoot.java:2216)
E/AndroidRuntime(31416): at android.view.ViewRoot.handleMessage(ViewRoot.java:1887)
E/AndroidRuntime(31416): at android.os.Handler.dispatchMessage(Handler.java:99)
E/AndroidRuntime(31416): at android.os.Looper.loop(Looper.java:130)
E/AndroidRuntime(31416): at android.app.ActivityThread.main(ActivityThread.java:3687)
E/AndroidRuntime(31416): at java.lang.reflect.Method.invokeNative(Native Method)
E/AndroidRuntime(31416): at java.lang.reflect.Method.invoke(Method.java:507)
E/AndroidRuntime(31416): at com.android.internal.os.ZygoteInit$MethodAndArgsCaller.run(ZygoteInit.java:867)
E/AndroidRuntime(31416): at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:625)
E/AndroidRuntime(31416): at dalvik.system.NativeStart.main(Native Method)
Since many memory analysis patterns are based on stack traces here we also have similarity with the following patterns names as Managed Code Exception and Managed Stack Trace. We hope that in the subsequent pattern implementation examples we show more complex patterns of abnormal software behaviour and may also discover any missing ones.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Android Trace Corner, Debugging, Java Debugging, LogCat Trace Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Friday, July 19th, 2013
Most of the time when we look at software trace fragments we recognize certain Motifs* such as client-server interaction, publisher-subscriber notifications, database queries, plugin sequence initialization, etc. This pattern is different from Master Trace which corresponds to a normal use-case or working software scenario and may actually contain several Motifs as it is usually happens in complex software environments. On the other side of the spectrum there are software narremes (basic narrative units) and Macrofunctions (single semantic units). Motifs help to further bridge the great divide between software construction and software diagnostics with software narremes corresponding to implementation patterns, macrofunctions to design patterns, and motifs to architectural patterns although an overlap between these categories is possible.
* The idea of a pattern name comes from motives in mathematics.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Software Diagnostics, Software Narratology, Software Narremes, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Wednesday, June 12th, 2013
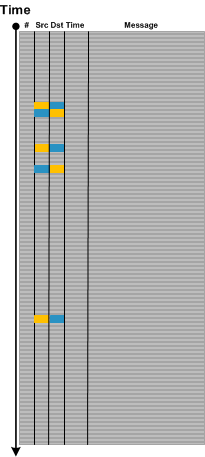
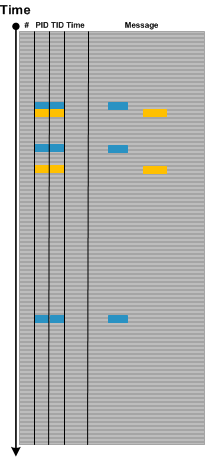
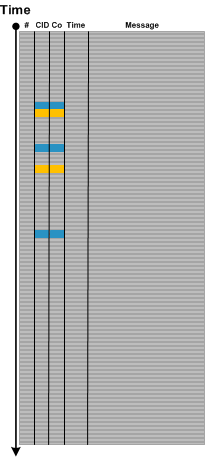
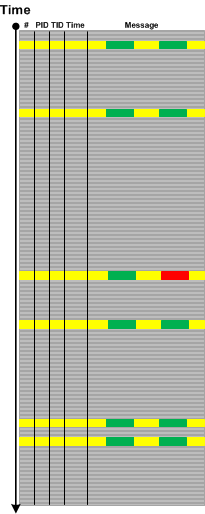
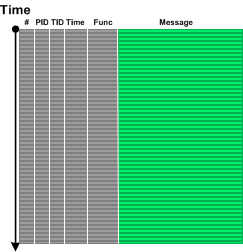
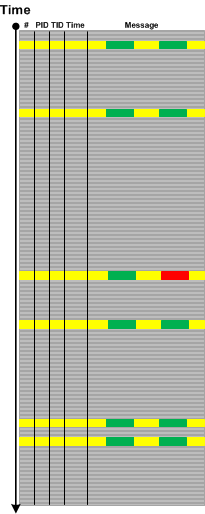
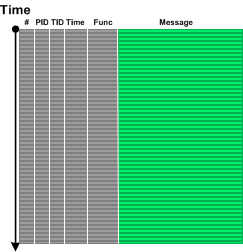
Dialogue is an important pattern especially in network trace analysis. It usually involves a message source, a different message target (although both can be the same) and some alternation between them as shown on this abstract trace diagram:
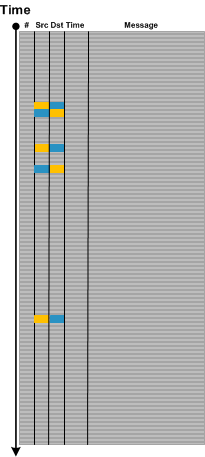
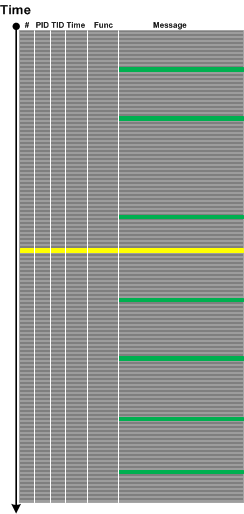
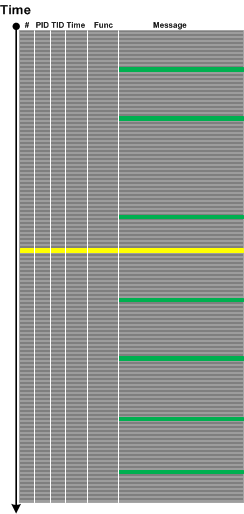
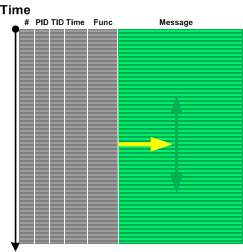
Message and source are not only IP addresses or port numbers. They can be window handles, for example. Sometimes, the roles of source and target play different Process ID and Thread ID combinations (Client ID, CID). In such cases some parts of a message text may signify reply and response as shown graphically:
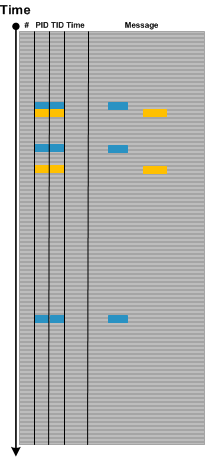
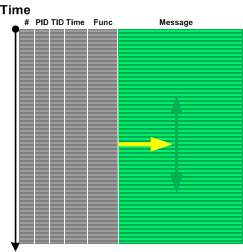
The similar illustration can be done for multi-computer trace, for example, when several traces from different servers are combined into one, where a combination of CID and a computer ID (Co) or just Co can play the roles of source and target.
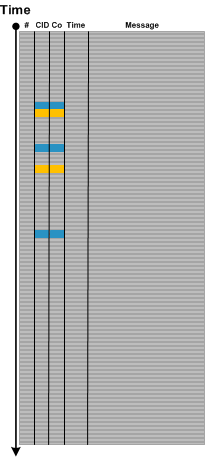
Note that on all illustrations above the 3rd request doesn’t have a reply message: a possible Incomplete History pattern.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Network Trace Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Tuesday, May 21st, 2013
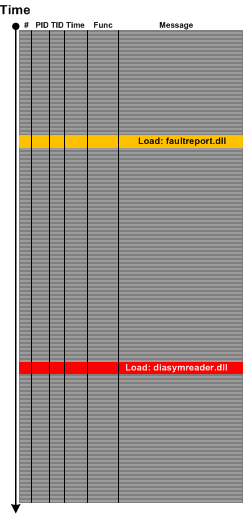
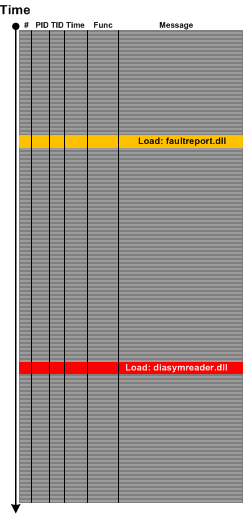
Sometimes we look at a trace or log and instead of Error Messages we only see their “signs” such as a DLL load event for an error or fault reporting module or a module that is related to symbol files such diasymreader.dll. We call this pattern Hidden Error by an analogy to Hidden Exception in memory dump analysis pattern catalogue although sometimes we can see such modules in memory dump Module Collection. For example, the presence of diasymreader module may signify an unreported .NET exception and suggest a dump collection strategy.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in .NET Debugging, CDF Analysis Tips and Tricks, Log Analysis, Process Monitor Log Analysis, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Sunday, May 12th, 2013
Sometimes we need to analyse Last Activity before Significant Event or Discontinuity. By this pattern we mean a loose semantic collection of messages before process exit, for example. This might give some clues to further troubleshooting. In one incident a process was suddenly exiting. Its own detailed trace didn’t have any messages explaining that probably due to insufficient tracing coverage (Sparse Trace). Fortunately, a different external trace (from Process Monitor) was collected (Inter-Correlation) and it had LDAP network communication messages just before thread and process exit events.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Saturday, May 4th, 2013
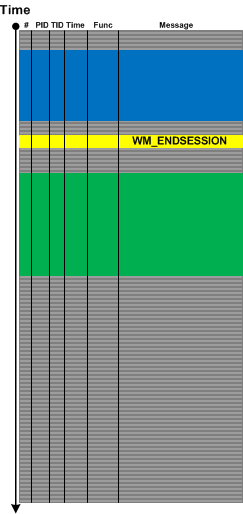
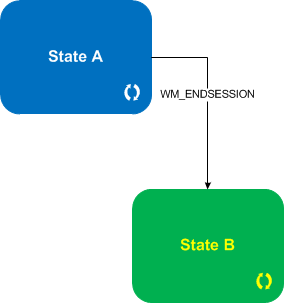
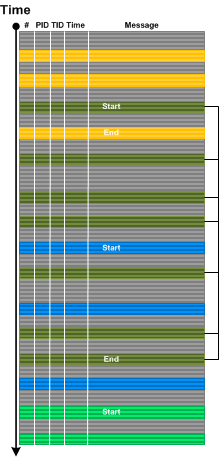
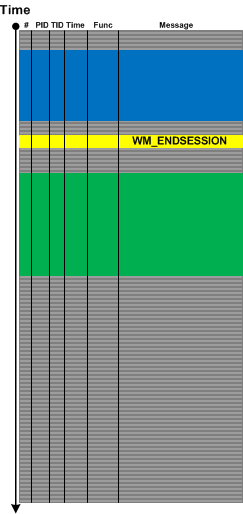
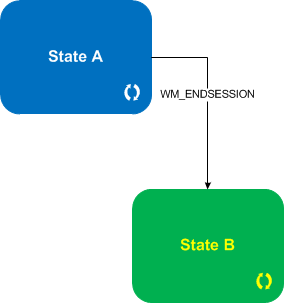
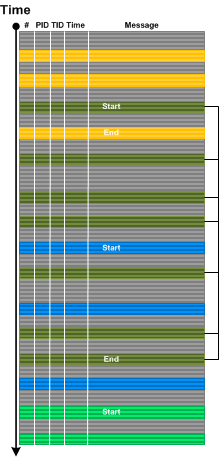
For event- or message-driven architectures it is important to differentiate between event and state messages (including state transition). For example, a system may be doing some work while being in some particular state with a lot of tracing and respond to various external events with each of them having a corresponding trace message. Upon such an event the system transitions to some other state with its own set of possible trace messages. We call such a pattern State and Event. Typical example here is a windowing terminal services system and WM_ENDSESSION event illustrated in the following abstract trace diagram with a corresponding state transition diagram below it:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in CDF Analysis Tips and Tricks, Log Analysis, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Thursday, April 25th, 2013
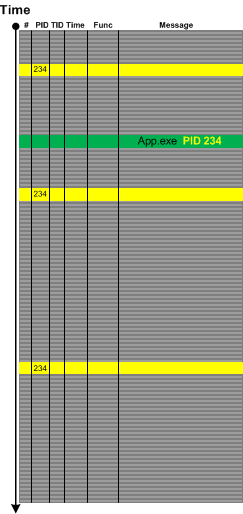
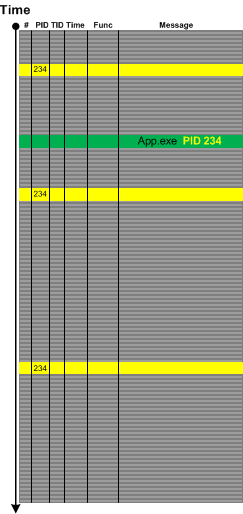
Sometimes in the case of missing Basic Facts we can discern Indirect Facts from message text and even from other patterns. For example, in one incident we were interested in all messages from the certain process name but its PID was missing from the problem description. Fortunately we were able to get its PID from one of individual messages from completely different source:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Monday, March 25th, 2013
In the past we viewed software traces and logs as temporarily ordered event sequences. Since events are just memory data we have a map
T -> M
as can be seen in the definition of a software trace. Here we generalize the domain to any arbitrary set, for example, it can be a list of indexes or pointers or even memory itself. The latter map can give us narrative chains such as
M -> M -> M -> M
and even give us a grand unification of memory and log analysis and the possibility to apply software narratology to memory dump analysis as well. We talk about it soon and provide some generalized software narrative examples.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Crash Dump Analysis, Crash Dump Patterns, Log Analysis, Software Narrative Science, Software Narratology, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Saturday, March 23rd, 2013
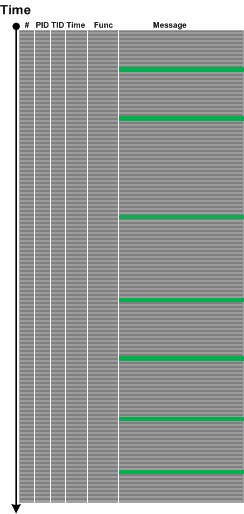
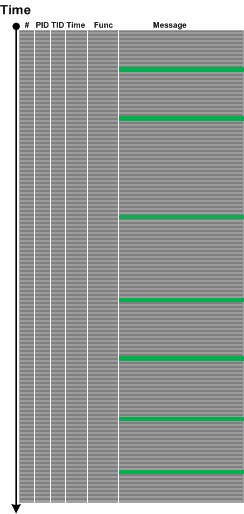
While preparing a presentation on malware narratives we found that one essential pattern is missing from the current log analysis pattern catalog. Most of the time we see some abnormal or unexpected value in a software trace or log such as a network address outside expected range and this triggers further investigation. The message structure may be the same having the same Message Invariant but variable part may contain such values as depicted graphically:
We call this pattern Abnormal Value and plan to add the similar one to memory dump analysis pattern catalog. Please not that we also have Significant Event pattern that is more general and also covers messages without variable part or just suspicious log entries.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Debugging, Log Analysis, Malware Analysis, Network Trace Analysis, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Wednesday, March 20th, 2013
Sometimes we have insufficiently detailed problem description and/or there are several similar parallel user activities going on simultaneously, for example, several session are launched in a terminal services environment. In such cases when tracing is done for the duration of specific user activity Dominant Event Sequence pattern may help. Here we select the most full sequence of events or event sequence based on some Basic Facts. For example, if session id was missing in problem description we can choose the most long and full process launch seqence and assume that its session id was the one missing:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in CDF Analysis Tips and Tricks, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Saturday, March 16th, 2013
Suppose we form an adjoint thread based on some message or operation type or some other attribute:
But we do not know where to start to look backwards for any anomalies relevant to our problem:
We go back to our full trace and find a problem message:
Although it is not in our adjoint thread we formed previously it is still considered as Pivot Message helping us to go backwards there:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Thursday, March 14th, 2013
If Implementation Discourse focuses on objective technology specific discourse then Traces of Individuality pattern focuses on subjective elements in a software log and its messages. Here we mean some specific naming or tracing conventions either from an individual engineer habit or from some corporate coding standard. As an example of it consider a trace message from a catch statement:
"Surprise, surprise, should have never been caught"
More examples for this pattern will be added later.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Software Trace Analysis, Software Trace Deconstruction, Software Trace Linguistics, Software Trace Reading, Software Trace Stylistics, Trace Analysis Patterns | No Comments »
Friday, February 15th, 2013
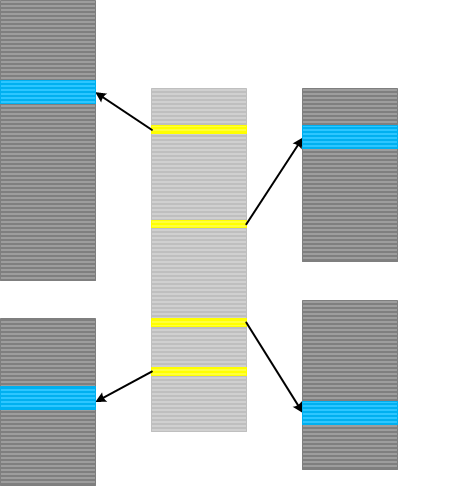
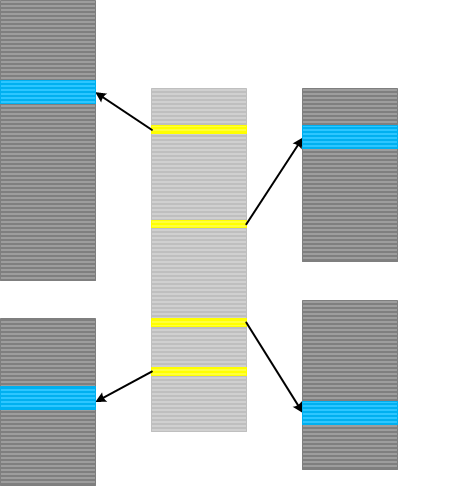
Inter-Correlation analysis between a normal and a problem logs to find a Bifurcation Point (and a possible root cause) becomes a difficult task when both traces come from different environments with widely differing Background Components. Here a new analysis pattern called Sheaf of Activities (borrowed from sheaves from mathematics) can help. Basically this pattern is also a tool in tracking properties of trace message subsets. First we find out important message types around some Activity Region where we hope to find a difference between two traces:

Then we create several Adjoint Threads from different message types, for example, based on operation type or function name:

Then we analyze subtraces separately to find out a bifurcation point in each of them and then use this knowledge to find out differences between the original full traces.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Debugging, Process Monitor Log Analysis, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Friday, February 8th, 2013
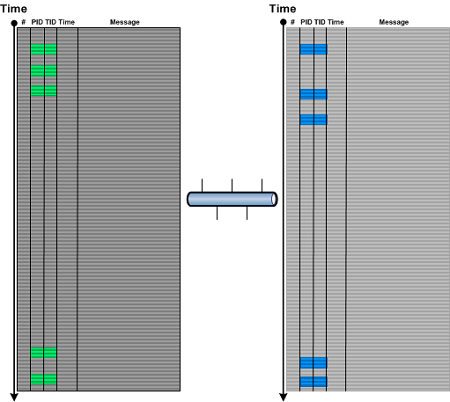
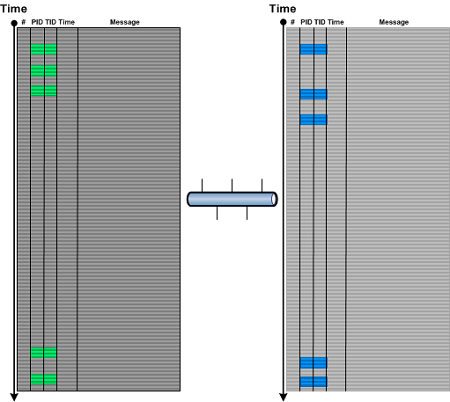
Indexical Trace pattern describes an Inter-Correlation pattern variant when we have a trace that has messages of interest pointing to specific activity regions in another trace. The latter trace can be very huge, from another computer and split into many parts (Split Trace). This pattern is very helpful when the problem needs to be diagnosed in the large split trace but we don’t know when it happened. Then an index trace that may have recorded software execution account (for example, in the case of a broker-like architecture) and can point to the right trace fragment from the split trace.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in CDF Analysis Tips and Tricks, Debugging, Software Architecture, Software Trace Analysis, Software Trace Reading, Trace Analysis Patterns | No Comments »
Friday, January 11th, 2013
Static program analysis is used to eliminate certain coding errors that may lead to abnormal software behaviour. So it is naturally a part of software diagnostics but at source code level. Our goal here is to identify certain patterns directly linkable to patterns we see in memory dumps and software logs and collect them into a catalog. One such pattern candidate is called Loop Construct. It covers conditional and unconditional loops, for example, in one of modern languages:
extern bool soonToBeTrue;
int mediumValue = ...;
while (true)
{
TRACE("Waiting");
sleep(mediumValue);
if (soonToBeTrue)
{
break;
}
doHeavyWork();
}
while (--pControl->aFewPasses)
{
TRACE("Waiting");
sleep(mediumValue);
doHeavyWork();
}
Such loops may potentially lead to Spiking Thread memory dump analysis and High Message Current and Density trace analysis patterns. Of course, we shouldn’t suspect every loop but only some that have potential to be altered by Local Buffer Overflow (for mediumValue) or Shared Buffer Overwrite (for Control.aFewPasses) or by a race condition (soonToBeTrue).
We expect things to get more interesting when we start associating source code that uses certain API with patterns of abnormal behavior.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in C and C++, Code Reading, Core Dump Analysis, Crash Dump Analysis, Crash Dump Patterns, Debugging, Security, Software Behavior Patterns, Software Diagnostics, Software Trace Analysis, Static Code Analysis Patterns, Trace Analysis Patterns, Victimware Analysis | No Comments »
Wednesday, January 9th, 2013
If you need to get various real life software traces with millions of lines from complex software environments to learn pattern-driven software log analysis you can us Process Monitor as a modeling tool. Here you can abstract from their “monitoring” and API interception context and consider trace messages as emitted from various processes and threads (like Citrix CDF traces). This approach was used in Accelerated Windows Software Trace Analysis training and Debugging TV Frames episode 0×19.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Software Trace Analysis, Software Trace Modeling, Trace Analysis Patterns | No Comments »
Friday, January 4th, 2013
Before deciding on whether to retrospect on 2012 we found that since March 14, 2008 this site has had more than 1 million visitors with more than 33% returning. So instead of just 2012 we decided to retrospect on that interval up to December 31, 2012. Google Analytics has improved since last January, 2012 and now made our task easier. So we start with the first one hundred sites referring to us:
| Source / Medium |
Visits
|
| google |
698156
|
| (direct) |
164142
|
| bing |
27923
|
| google.com |
17868
|
| windbg.org |
12994
|
| yahoo |
8682
|
| stackoverflow.com |
7194
|
| yandex |
5985
|
| windbg.dumpanalysis.org |
5375
|
| dumpanalysis.com |
5369
|
| live |
5310
|
| google.co.in |
4598
|
| blogs.msdn.com |
4385
|
| baike.baidu.com |
3475
|
| twitter.com |
2972
|
| facebook.com |
2733
|
| dumpanalysis.org |
2708
|
| images.google.com |
2314
|
| t.co |
2095
|
| baidu |
1916
|
| winvistaclub.com |
1862
|
| google.co.uk |
1449
|
| advancedwindowsdebugging.com |
1427
|
| jasonhaley.com |
1370
|
| search |
1328
|
| rsdn.ru |
1294
|
| en.wikipedia.org |
1276
|
| msn |
1256
|
| nynaeve.net |
1256
|
| blog.codeimproved.net |
1213
|
| google.de |
1074
|
| google.ca |
979
|
| reddit.com |
951
|
| bytetalk.net |
908
|
| citrixblogger.org |
819
|
| stumbleupon.com |
819
|
| linkedin.com |
780
|
| social.technet.microsoft.com |
774
|
| analyze-v.com |
757
|
| naver |
750
|
| forum.sysinternals.com |
735
|
| google.ru |
710
|
| blogs.microsoft.co.il |
693
|
| kumo.com |
678
|
| google.co.kr |
658
|
| google.com.au |
654
|
| blog.naver.com |
646
|
| reconstructer.org |
645
|
| community.citrix.com |
632
|
| blog.not-a-kernel-guy.com |
604
|
| itdatabase.com |
601
|
| advanceddotnetdebugging.com |
581
|
| serverfault.com |
564
|
| voneinem-windbg.blogspot.com |
561
|
| support.citrix.com |
555
|
| debuggingexperts.com |
549
|
| blog.miniasp.com |
527
|
| google.fr |
495
|
| caloni.com.br |
488
|
| google.com.br |
479
|
| ask |
459
|
| msuiche.net |
439
|
| insidewindows.kr |
432
|
| google.es |
430
|
| gynvael.coldwind.pl |
430
|
| blog.flexilis.com |
429
|
| aol |
418
|
| netfxharmonics.com |
416
|
| advdbg.org |
413
|
| images.google.co.uk |
401
|
| google.it |
391
|
| images.google.co.in |
391
|
| google.nl |
354
|
| serious-code.net |
340
|
| admin.itdatabase.com |
337
|
| blogs.technet.com |
334
|
| brianmadden.com |
327
|
| google.pl |
319
|
| google.com.ua |
318
|
| experts-exchange.com |
316
|
| delicious.com |
312
|
| images.google.de |
305
|
| opentask.com |
301
|
| codemachine.com |
296
|
| driveronline.org |
287
|
| google.com.tw |
282
|
| wasm.ru |
275
|
| debuglab.com |
265
|
| isisaka.com |
262
|
| literatescientist.com |
261
|
| blog.zoller.lu |
258
|
| shellexecute.wordpress.com |
257
|
| google.com.hk |
256
|
| managementbits.com |
253
|
| d.hatena.ne.jp |
251
|
| bloglines.com |
249
|
| google.com.tr |
248
|
| clausbrod.de |
246
|
| bing.com |
243
|
Next table is distribution of visits among countries:
| Country / Territory |
Visits
|
| United States |
342291
|
| India |
89303
|
| United Kingdom |
76131
|
| Russia |
46472
|
| Germany |
44472
|
| China |
40155
|
| Canada |
34781
|
| Japan |
24985
|
| France |
24084
|
| South Korea |
21056
|
| Australia |
20606
|
| Taiwan |
17949
|
| Netherlands |
15607
|
| Ireland |
15579
|
| Israel |
13514
|
| Ukraine |
13449
|
| Italy |
12542
|
| Brazil |
11834
|
| Spain |
11786
|
| Singapore |
11703
|
| Sweden |
11201
|
| Poland |
10340
|
| Romania |
9423
|
| (not set) |
8909
|
| Czech Republic |
8355
|
| Belgium |
6731
|
| Switzerland |
6624
|
| Finland |
6596
|
| Norway |
5585
|
| Malaysia |
5289
|
| Philippines |
5052
|
| Austria |
5046
|
| Denmark |
4980
|
| Hong Kong |
4914
|
| Turkey |
4728
|
| Slovakia |
4599
|
| New Zealand |
4369
|
| Portugal |
4228
|
| Argentina |
3712
|
| Belarus |
3518
|
| Hungary |
3465
|
| Bulgaria |
3301
|
| Mexico |
2960
|
| South Africa |
2945
|
| Vietnam |
2721
|
| Greece |
2712
|
| Indonesia |
2527
|
| Croatia |
1881
|
| Serbia |
1843
|
| Iran |
1842
|
| Thailand |
1726
|
| Pakistan |
1660
|
| Egypt |
1519
|
| Malta |
1422
|
| Estonia |
1385
|
| Slovenia |
1334
|
| Lithuania |
1304
|
| United Arab Emirates |
1167
|
| Chile |
1104
|
| Saudi Arabia |
1096
|
| Colombia |
1067
|
| Latvia |
922
|
| Kazakhstan |
725
|
| Peru |
649
|
| Morocco |
585
|
| Sri Lanka |
516
|
| Luxembourg |
516
|
| Moldova |
439
|
| Uruguay |
435
|
| Venezuela |
431
|
| Jordan |
425
|
| Tunisia |
425
|
| Bolivia |
418
|
| Armenia |
371
|
| Algeria |
362
|
| Costa Rica |
355
|
| Iceland |
353
|
| Panama |
352
|
| Macedonia [FYROM] |
347
|
| Bosnia and Herzegovina |
327
|
| Cyprus |
317
|
| Bangladesh |
314
|
| Nigeria |
298
|
| Puerto Rico |
296
|
| Jamaica |
251
|
| Ecuador |
248
|
| Kuwait |
239
|
| Lebanon |
218
|
| Qatar |
217
|
| Kenya |
195
|
| Georgia |
194
|
| Mongolia |
189
|
| Dominican Republic |
163
|
| Macau |
156
|
| Trinidad and Tobago |
147
|
| Bahrain |
143
|
| Uzbekistan |
142
|
| Guatemala |
141
|
| Azerbaijan |
134
|
| Mauritius |
128
|
| Oman |
117
|
| Nepal |
110
|
| El Salvador |
106
|
| Syria |
103
|
| Iraq |
102
|
| Ghana |
96
|
| Kyrgyzstan |
86
|
| Cambodia |
72
|
| Albania |
71
|
| Serbia and Montenegro |
63
|
| Ethiopia |
63
|
| Uganda |
61
|
| Brunei |
57
|
| Honduras |
55
|
| Isle of Man |
55
|
| Yemen |
55
|
| Cuba |
54
|
| Sudan |
54
|
| Palestinian Territories |
52
|
| Barbados |
49
|
| Myanmar [Burma] |
48
|
| Paraguay |
45
|
| Liechtenstein |
43
|
| Montenegro |
43
|
| Rwanda |
42
|
| Libya |
41
|
| Namibia |
41
|
| Jersey |
40
|
| Maldives |
40
|
| Turks and Caicos Islands |
39
|
| Bermuda |
38
|
| Zimbabwe |
34
|
| Fiji |
32
|
| Nicaragua |
32
|
| Tanzania |
29
|
| Réunion |
27
|
| Gibraltar |
26
|
| New Caledonia |
26
|
| Bahamas |
25
|
| Monaco |
25
|
| Netherlands Antilles |
24
|
| Aruba |
24
|
| Botswana |
24
|
| Cayman Islands |
23
|
| Angola |
22
|
| Madagascar |
20
|
| Guam |
19
|
| Afghanistan |
17
|
| Côte d’Ivoire |
17
|
| Papua New Guinea |
17
|
| Dominica |
16
|
| Guernsey |
16
|
| Guyana |
16
|
| Suriname |
16
|
| Andorra |
14
|
| Belize |
14
|
| Congo [DRC] |
14
|
| Lesotho |
14
|
| Mozambique |
13
|
| Antigua and Barbuda |
12
|
| Laos |
12
|
| French Polynesia |
11
|
| Zambia |
11
|
| Saint Lucia |
10
|
| San Marino |
10
|
| Senegal |
10
|
| Saint Vincent and the Grenadines |
10
|
| Benin |
9
|
| Guinea |
9
|
| Guadeloupe |
9
|
| Malawi |
9
|
| Turkmenistan |
9
|
| U.S. Virgin Islands |
8
|
| Faroe Islands |
7
|
| Grenada |
7
|
| Haiti |
7
|
| British Virgin Islands |
7
|
| Cameroon |
6
|
| French Guiana |
6
|
| Greenland |
6
|
| Martinique |
6
|
| Seychelles |
6
|
| Timor-Leste |
6
|
| Mali |
5
|
| Tajikistan |
5
|
| Gabon |
4
|
| Anguilla |
3
|
| Å land Islands |
3
|
| Swaziland |
3
|
| Burundi |
2
|
| Congo [Republic] |
2
|
| Cape Verde |
2
|
| Djibouti |
2
|
| Saint Kitts and Nevis |
2
|
| Liberia |
2
|
| Somalia |
2
|
| Togo |
2
|
| Vanuatu |
2
|
| Burkina Faso |
1
|
| Bhutan |
1
|
| Falkland Islands [Islas Malvinas] |
1
|
| Gambia |
1
|
| Equatorial Guinea |
1
|
| Guinea-Bissau |
1
|
| Comoros |
1
|
| Mauritania |
1
|
| Palau |
1
|
| Sierra Leone |
1
|
| Vatican City |
1
|
| Samoa |
1
|
Then the first 100 network locations:
| Service Provider |
Visits
|
| microsoft corp |
33646
|
| comcast cable communications inc. |
18544
|
| road runner holdco llc |
16529
|
| internet service provider |
12815
|
| comite gestor da internet no brasil |
10995
|
| hewlett-packard company |
10961
|
| deutsche telekom ag |
9889
|
| japan network information center |
9746
|
| verizon internet services inc. |
7851
|
| network of citrix systems inc |
6945
|
| intel corporation |
6873
|
| symantec corporation |
6812
|
| chunghwa telecom data communication business group |
6381
|
| ip pools |
6314
|
| insignium llc |
6206
|
| reliance communications ltd |
5870
|
| charter communications |
5583
|
| uunet non-portable customer assignment |
4931
|
| verizon online llc |
4900
|
| comcast cable communications holdings inc |
4700
|
| at&t internet services |
4617
|
| eircom |
4567
|
| cox communications |
4540
|
| proxad / free sas |
4451
|
| korea telecom |
4397
|
| abts (karnataka) |
4251
|
| nib (national internet backbone) |
4243
|
| chinanet guangdong province network |
4189
|
| comcast cable communications |
3896
|
| unknown |
3279
|
| xo communications |
3274
|
| chinanet shanghai province network |
3248
|
| shaw communications inc. |
3179
|
| qwest communications company llc |
3156
|
| telstra internet |
3130
|
| tw telecom holdings inc. |
3091
|
| citrix systems inc. |
3029
|
| data general corporation |
2998
|
| cox communications inc. |
2946
|
| bellsouth.net inc. |
2925
|
| optimum online (cablevision systems) |
2853
|
| china unicom beijing province network |
2850
|
| chtd chunghwa telecom co. ltd. |
2791
|
| krnic |
2786
|
| ntt communications corporation |
2779
|
| psinet inc. |
2599
|
| emc corporation |
2499
|
| comcast cable communications ip services |
2435
|
| arcor ag |
2371
|
| cisco systems inc. |
2364
|
| (not set) |
2335
|
| broadband multiplay project o/o dgm bb noc bsnl bangalore |
2285
|
| research in motion limited |
2283
|
| samtel |
2257
|
| rcs & rds s.a. |
2246
|
| computer associates international |
2166
|
| honeywell international inc. |
2106
|
| telus communications inc. |
2103
|
| customers ie |
1954
|
| sympatico hse |
1929
|
| comcast business communications llc |
1853
|
| telefonica de espana sau |
1843
|
| iinet limited |
1840
|
| ziggo consumers |
1810
|
| easynet ltd |
1758
|
| comcast business communications inc. |
1738
|
| microsoft |
1717
|
| kaspersky lab internet |
1698
|
| appense |
1687
|
| chinanet jiangsu province network |
1665
|
| dell computer corporation |
1656
|
| eircom ltd |
1644
|
| taipei taiwan |
1612
|
| abts tamilnadu |
1594
|
| network of ign arch. and design gb |
1578
|
| starhub cable vision ltd |
1555
|
| wipro technologies |
1537
|
| level 3 communications inc. |
1522
|
| tpg internet pty ltd. |
1510
|
| siemens ag |
1483
|
| microsoft corporation |
1478
|
| global crossing |
1433
|
| singnet pte ltd |
1429
|
| dynamic pools |
1426
|
| this space is statically assigned. |
1425
|
| videsh sanchar nigam ltd - india. |
1414
|
| provider local registry |
1403
|
| abts delhi |
1385
|
| qwest communications corporation |
1356
|
| kla instruments corp. |
1316
|
| telia network services |
1311
|
| cncgroup beijing province network |
1278
|
| frontier communications of america inc. |
1264
|
| telecom italia s.p.a. tin easy lite |
1257
|
| videotron ltee |
1255
|
| oracle datenbanksysteme gmbh |
1234
|
| neostrada plus |
1228
|
| suddenlink communications |
1214
|
| dynamic ip pool for broadband customers |
1202
|
| eset s.r.o. |
1200
|
Then the first 100 search keywords and phrases that led to us:
| Keyword |
Visits
|
| (not provided) |
53903
|
| kifastsystemcallret |
10644
|
| crash dump analysis |
10348
|
| crash dump |
9863
|
| ntdll!kifastsystemcallret |
4305
|
| dump analysis |
4143
|
| adplus |
3332
|
| win32 error 0n2 |
2553
|
| windbg commands |
2198
|
| memory dump analysis |
2183
|
| windbg |
2131
|
| crash dumps |
1825
|
| dumpanalysis.org |
1818
|
| nt!_gshandlercheck_seh |
1734
|
| dmitry vostokov |
1718
|
| crashdump |
1683
|
| symbol file could not be found |
1669
|
| bugcheck 3b |
1458
|
| memory dump analysis anthology |
1393
|
| crash dump analyzer |
1360
|
| warning: frame ip not in any known module. following frames may be wrong. |
1347
|
| windbg cheat sheet |
1318
|
| windbg crash dump analysis |
1271
|
| minidump analysis |
1259
|
| adplus download |
1214
|
| core dump analysis |
1167
|
| fnodobfm |
1159
|
| dumpanalysis |
1142
|
| windows 7 crash dump |
1142
|
| windbg analyze |
1118
|
| kisystemservicecopyend |
1066
|
| frame ip not in any known module |
1010
|
| getcontextstate failed, 0×80070026 |
949
|
| crash dump windows 7 |
930
|
| the stored exception information can be accessed via .ecxr. |
925
|
| windbg script |
922
|
| error: symbol file could not be found |
912
|
| vista crash dump |
895
|
| windows crash dump analysis |
888
|
| system_thread_exception_not_handled |
857
|
| анализ дампа памяти |
857
|
| dump analyzer |
847
|
| дамп памяти |
821
|
| pool corruption |
820
|
| time travel debugging |
776
|
| system_service_exception |
772
|
| kernel_mode_exception_not_handled |
741
|
| ntdll kifastsystemcallret |
741
|
| the stored exception information can be accessed via .ecxr |
734
|
| kmode_exception_not_handled |
726
|
| trap frame |
719
|
| idna trace |
695
|
| windbg crash dump |
694
|
| kiuserexceptiondispatcher |
691
|
| minidump analyzer |
672
|
| bugcheck 7e |
670
|
| kernel32!pnlsuserinfo |
643
|
| windbg scripts |
641
|
| rtlpwaitoncriticalsection |
635
|
| minidump |
628
|
| bugcheck system_service_exception |
621
|
| exception_double_fault |
597
|
| warning: stack unwind information not available. following frames may be wrong. |
584
|
| application_fault_status_breakpoint |
583
|
| crash dump vista |
582
|
| memory dump analysis tool |
576
|
| getcontextstate failed, 0xd0000147 |
575
|
| memoretics |
544
|
| dumpanalysis.org/asmpedia |
537
|
| failure_bucket_id |
524
|
| “dec 15″ module windbg |
511
|
| error: symbol file could not be found. |
511
|
| download adplus |
507
|
| basethreadinitthunk |
505
|
| dr watson vista |
505
|
| ntkrnlmp.exe crash dump |
499
|
| ntdll.dll!kifastsystemcallret |
492
|
| rtlplowfragheapfree |
488
|
| analyze minidump |
477
|
| adplus tutorial |
473
|
| application_hang_blockedon_fileio |
468
|
| bios disassembly ninjutsu uncovered |
460
|
| ntdll.kifastsystemcallret |
460
|
| analyze crash dump |
459
|
| windows dump analysis |
459
|
| debug_flr_image_timestamp |
456
|
| system_thread_exception_not_handled (7e) |
456
|
| windbg dump analysis |
446
|
| windbg hang |
438
|
| windows debugging: practical foundations |
434
|
| crash dump analysis windbg |
432
|
| dynamicbase aslr |
422
|
| crash dump analysis tool |
419
|
| nt!kebugcheckex |
414
|
| rtluserthreadstart |
414
|
| type referenced: kernel32!pnlsuserinfo |
407
|
| error: symbol file could not be found. defaulted to export symbols for ntkrnlmp.exe |
405
|
| memory dump |
403
|
| warning: frame ip not in any known module. following frames may be wrong |
399
|
| application_hang_busyhang |
398
|
Then browser stats (we have never thought that there are so many of them):
| Browser |
Visits
|
| Internet Explorer |
446051
|
| Firefox |
356686
|
| Chrome |
184535
|
| Opera |
45787
|
| Safari |
24123
|
| Mozilla |
3780
|
| Mozilla Compatible Agent |
2401
|
| Android Browser |
1337
|
| Konqueror |
1057
|
| IE with Chrome Frame |
982
|
| Opera Mini |
705
|
| SeaMonkey |
503
|
| Safari (in-app) |
197
|
| Lunascape |
144
|
| BlackBerry8900 |
128
|
| Camino |
126
|
| RockMelt |
124
|
| (not set) |
96
|
| Netscape |
72
|
| Playstation 3 |
36
|
| IUC |
34
|
| Googlebot |
29
|
| Lynx |
24
|
| Unsupported Browser Version |
22
|
| BlackBerry9630 |
21
|
| NetFront |
17
|
| BlackBerry9700 |
15
|
| Microsoft-Symbol-Server |
14
|
| BlackBerry9000 |
12
|
| Galeon |
11
|
| Midori |
9
|
| NokiaE63 |
9
|
| Yahoo! Slurp |
9
|
| BlackBerry8530 |
8
|
| BlackBerry8520 |
7
|
| PagePeeker.com |
7
|
| SAMSUNG-SGH-I617 |
7
|
| BlackBerry9530 |
6
|
| JUC |
6
|
| MSR-ISRCCrawler |
6
|
| OpenWave |
6
|
| anonimo |
5
|
| BlackBerry9300 |
5
|
| HTC_HD2_T8585 Opera |
5
|
| Nokia5233 |
5
|
| Space Bison |
5
|
| -Vasya |
4
|
| Blazer |
4
|
| Uzbl |
4
|
-^_^- Hello  |
3
|
| <?echo ‘<pre>’; system |
3
|
| 12345 |
3
|
| BlackBerry9330 |
3
|
| BlackBerry9650 |
3
|
| HTC_P3700 Opera |
3
|
| HTC_TyTN_II Mozilla |
3
|
| NOKIAN78 |
3
|
| Playstation Portable |
3
|
| PPC; 240×320; HTC_P3450 |
3
|
| undefined GoogleToolbarBB |
3
|
| anonymous |
2
|
| Empty |
2
|
| GreatBrowse |
2
|
| Helyi user agent |
2
|
| HTC_Touch_Pro2_T7373 Opera |
2
|
| HTC_Touch2_T3333 Opera |
2
|
| J2ME |
2
|
| Mozilla 5.0 |
2
|
| NokiaC1-01 |
2
|
| NokiaC3-00 |
2
|
| NokiaC7-00 |
2
|
| NokiaX2-01 |
2
|
| nwzfq |
2
|
| test |
2
|
| — |
1
|
| ?M5 |
1
|
| “PagePeeker.com” |
1
|
| <?include |
1
|
| <script>alert |
1
|
| <SCRIPT>window.location=’http: |
1
|
| 2.0.0.11 |
1
|
| 31337′ |
1
|
| 8900b |
1
|
| AltaVista Intranet V2.0 evreka.com crawler@evreka.com |
1
|
| annoying |
1
|
| AppEngine-Google; |
1
|
| BlackBerry9500 |
1
|
| BlackBerry9550 |
1
|
| bwh3_user_agent |
1
|
| Citrix |
1
|
| EBABrowser |
1
|
| EY |
1
|
| fake_user_agent Mozilla |
1
|
| FAST Enterprise Crawler 6 used by Reed Exhibitions |
1
|
| foo |
1
|
| General Browser |
1
|
| GOOGLEBOT |
1
|
| HD_mini_T5555 Opera |
1
|
| Hellbrowser 6.66 |
1
|
| holy_teacher FirePHP |
1
|
| HTC_P3490 Opera |
1
|
| HTC_P4550 Mozilla |
1
|
| HTC_Polaris Mozilla |
1
|
| HTC_Touch_3G_T3232 Opera |
1
|
| HTC_Touch_HD_T8282 Opera |
1
|
| HTC_Touch_Pro_T7272 Opera |
1
|
| HTC_Touch2_T3320 Opera |
1
|
| HTC-8900 |
1
|
| IE 8 |
1
|
| IE6 |
1
|
| iTunes |
1
|
| Keep Out |
1
|
| KraftwayBrowser2 |
1
|
| Links |
1
|
| Maemo Browser |
1
|
| Medusa |
1
|
| MERONG |
1
|
| Motorola_ES405B |
1
|
| mozilla |
1
|
| Mozilla Firefox |
1
|
| MS-OC 4.0 |
1
|
| msie |
1
|
| NCSA Mosaic |
1
|
| NightDynamo AdminPanel v0.2.1 |
1
|
| Nokia2700c-2 |
1
|
| Nokia2730c-1 |
1
|
| Nokia305 |
1
|
| Nokia5230 |
1
|
| Nokia5310XpressMusic |
1
|
| Nokia5800 XpressMusic |
1
|
| Nokia6300 |
1
|
| Nokia6700c-1 |
1
|
| NokiaC2-01 |
1
|
| NokiaC2-02 |
1
|
| NokiaC2-03 |
1
|
| NokiaC5-03 |
1
|
| nokiac6-00 |
1
|
| NokiaC6-00 |
1
|
| NOKIAE65 |
1
|
| NokiaE66 |
1
|
| NokiaE71 |
1
|
| NokiaE71-2;Mozilla |
1
|
| NokiaE72-1 |
1
|
| NokiaN-GageQD |
1
|
| NokiaN70-1 |
1
|
| NokiaNokia 6210s |
1
|
| NoneOfYourBusiness |
1
|
| nothisname_wangxiaoyang3 |
1
|
| OmniWeb |
1
|
| Palm750 |
1
|
| Peeplo Screenshot Bot |
1
|
| PerTrUsTsQuiD |
1
|
| pippos.7 |
1
|
| PPC; 480×800; HTC_Touch_HD_T8282; OpVer 34.159.1.612 |
1
|
| PriceGoblin User Agent |
1
|
| Private |
1
|
| Privoxy |
1
|
| Read Later |
1
|
| SAMSUNG-GT-E2222 |
1
|
| samsung-gt-s3653 |
1
|
| samsung-gt-s3653 UNTRUSTED |
1
|
| SAMSUNG-S8000 |
1
|
| SAMSUNG-SGH-I637 |
1
|
| Samsung-SPHM540 Polaris |
1
|
| SmallProxy 3.5.4 |
1
|
| SonyEricssonK750 |
1
|
| Surf |
1
|
| tdhbrowser |
1
|
| TiFiC Client Z |
1
|
| union update table sd_users set userid=9 where username=’coco |
1
|
| unknown |
1
|
| Unknown |
1
|
| UNTRUSTED |
1
|
| Updownerbot |
1
|
| WIN |
1
|
| WinXP SP2 |
1
|
| Wlwap |
1
|
| WM5 PIE |
1
|
| Xda_orbit_2; 240×320 |
1
|
| Xyi znat kakoi browser MRA 5.7 |
1
|
| ZooShot 0.1a |
1
|
| ZooShot 0.42 |
1
|
and finally mobile devices stats (you may find your own device there):
| Mobile Device Info |
Visits
|
| Apple iPhone |
2292
|
| Apple iPad |
1940
|
| (not set) |
1099
|
| Samsung GT-I9100 Galaxy S II |
167
|
| Apple iPod Touch |
112
|
| Asus Eee Pad Transformer TF101 |
112
|
| SonyEricsson LT15i Xperia Arc |
94
|
| Motorola Xoom |
47
|
| Samsung Galaxy Nexus |
47
|
| Samsung GT-I9000 Galaxy S |
34
|
| Samsung GT-P7510 Galaxy Tab 10.1 |
30
|
| Google Nexus S Samsung Nexus S |
26
|
| HTC EVO 4G |
26
|
| Google Nexus 7 |
21
|
| RIM BlackBerry Bold Touch 9900 Dakota |
21
|
| Samsung GT-N7000 Galaxy Note |
21
|
| Acer A500 Picasso |
17
|
| Asus Eee Pad TF201 Transformer Prime |
17
|
| HTC Desire HD |
17
|
| Motorola DroidX |
17
|
| Motorola XT862 Droid 3 |
17
|
| Samsung GT-S5830 Galaxy Ace |
17
|
| Samsung SGH-I747 Galaxy SIII |
17
|
| Samsung SGH-i917 Omnia 7 |
17
|
| Verizon Droid2 |
17
|
| Google Nexus One |
13
|
| Google Nexus One HTC Nexus One |
13
|
| HTC ADR6300 Incredible |
13
|
| Motorola Droid 2 |
13
|
| Samsung GT-P7500 P4 |
13
|
| Samsung SHW-M250K GALAXY S II (KT) |
13
|
| Apple iPod |
9
|
| BlackBerry 9780 |
9
|
| BlackBerry 9800 Torch |
9
|
| Dell Venue Pro |
9
|
| HTC Desire |
9
|
| HTC G2 HTC Sappire |
9
|
| HTC HD7 |
9
|
| HTC T9292 HD7 |
9
|
| Motorola MB860 Atrix |
9
|
| Nokia E63 |
9
|
| RIM BlackBerry 8530 Curve |
9
|
| Samsung GT-I9001 |
9
|
| Samsung GT-I9300 Galaxy S3 |
9
|
| Samsung GT-N8000 Galaxy Note 10.1 |
9
|
| Samsung GT-P1000 Galaxy Tab |
9
|
| Sharp IS03 IS03 for KDDI |
9
|
| T-Mobile myTouch4G |
9
|
| Toshiba AT100 |
9
|
| ZTE N860 |
9
|
| Acer A101 Vangogh |
4
|
| Acer A200 Picasso_E |
4
|
| Acer Acer E310 Liquid Mini |
4
|
| Asus TF300T Transformer Pad TF300T |
4
|
| BlackBerry 8520 Curve |
4
|
| BlackBerry 9900 Dakota |
4
|
| DoCoMo L-05D Optimus it |
4
|
| DoCoMo P502i |
4
|
| Fujitsu F-12C F-12C for DoCoMo |
4
|
| Google Nexus S |
4
|
| Google Wireless Transcoder |
4
|
| HTC A8181 Desire |
4
|
| HTC ADR6350 Droid Incredible 2 |
4
|
| HTC ADR6400L Thunderbolt |
4
|
| HTC ADR6400L Thunderbolt 4G |
4
|
| HTC APC715CKT EVO Design 4G |
4
|
| HTC Bravo |
4
|
| HTC Desire X0H6T |
4
|
| HTC Glacier |
4
|
| HTC Incredible S Incredible S |
4
|
| HTC Inspire 4G |
4
|
| HTC ISW12HT EVO 3D ISW12HT for KDDI |
4
|
| HTC Mozart 7 Mozart |
4
|
| HTC PC36100 EVO 4G |
4
|
| HTC PJ83100 One X |
4
|
| HTC Radar 4G |
4
|
| HTC S510e Desire S |
4
|
| HTC T7380 TouchFLO |
4
|
| HTC X515 EVO 3D |
4
|
| Huawei M860 Ascend |
4
|
| Huawei u8800 Ideos X5 |
4
|
| kddi ISW11HT HTC EVO WiMAX ISW11HT for KDDI |
4
|
| LG C900 Quantum |
4
|
| LG E900 Optimus 7 |
4
|
| LG LS670 Optimus S |
4
|
| LG MS690 Optimus M |
4
|
| LG VM670 Optimus V |
4
|
| LG VS910 4G Revolution |
4
|
| Motorola A953 MILESTONE 2 |
4
|
| Motorola ISW11M PHOTON ISW11M for KDDI |
4
|
| Motorola MB501 |
4
|
| Motorola MB525 DEFY |
4
|
| Motorola MB611 |
4
|
| Motorola MOTXT912B Droid Razr 4G |
4
|
| Motorola MZ601 Xoom |
4
|
| Motorola MZ604 Xoom |
4
|
| Motorola MZ605 Xoom |
4
|
| Motorola xt875 Droid Bionic |
4
|
| Nokia 5800d XpressMusic |
4
|
| Nokia C3-00 |
4
|
| Nokia C5-03 C5 |
4
|
| Nokia C6-00 |
4
|
| Nokia Lumia 710 |
4
|
| Nokia Lumia 800 |
4
|
| RIM BlackBerry 9300 Curve 3G |
4
|
| RIM BlackBerry 9700 Bold |
4
|
| RIM BlackBerry 9800 Torch |
4
|
| RIM Blackberry Bold Touch 9930 |
4
|
| Samsung GT i5700 Galaxy Spica |
4
|
| Samsung GT I9000T Galaxy S |
4
|
| Samsung GT-I9100G Galaxy S II |
4
|
| Samsung GT-I9100P Galaxy S II NFC |
4
|
| Samsung GT-I9103 |
4
|
| Samsung GT-I9300 Galaxy SIII |
4
|
| Samsung GT-N8010 Galaxy Note 10.1 |
4
|
| Samsung GT-P7500 Galaxy Tab 10.1 |
4
|
| Samsung SCH-I500 Fascinate |
4
|
| Samsung SCH-I535 4G Galaxy SIII |
4
|
| Samsung SGH-i717 Galaxy Note |
4
|
| Samsung SGH-I747 Galaxy S3 |
4
|
| Samsung SGH-I777 |
4
|
| Samsung SGH-I777 Galaxy S II |
4
|
| Samsung SGH-I897 Galaxy S Captivate |
4
|
| Samsung SHW-M250S GALAXY S II (SKT) |
4
|
| Samsung SPH-D700 Epic 4G |
4
|
| Samsung SWH-M110S |
4
|
| Sharp 003SH Sharp Galapagos 003SH for SoftBank |
4
|
| Softbank 001DL DELL Streak |
4
|
| SonyEricsson LT26i Xperia Arc HD |
4
|
| Xiaomi MI-ONE Plus M1 Plus |
4
|
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Announcements, Crash Dump Analysis, Debugging, DumpAnalysis.org Statistics, History, Malware Analysis, Software Diagnostics, Software Diagnostics Institute, Software Engineering, Software Technical Support, Software Trace Analysis, Victimware Analysis | No Comments »
Friday, December 14th, 2012
This pattern is called Opposition Messages (borrowed from binary opposition originated in Saussure’s structuralism). It covers the following pairs of messages usually found in software traces and logs such as:
- open / close
- create / destroy
- allocate / free (deallocate)
- call / return
- enter / exit (leave)
- load / unload
- save / load
- lock / unlock
- map / unmap
The absence of an opposite may point to some problems such as synchronization and leaks or Incomplete History (wait chains). There can always be a possibility that a second term is missing due to Sparse Trace but this is a poor implementation choice that leads to confusion during troubleshooting and debugging.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Debugging, Software Trace Analysis, Software Trace Reading, Software Tracing Implementation Patterns, Trace Analysis Patterns | No Comments »
Thursday, December 13th, 2012
Some tracing tools such as Citrix CDFControl have an option to split software traces and logs into several files during long recording. Although this should be done judiciously it is really necessary sometimes. We call this pattern Split Trace. What to do if we get several trace files and we want to use some other analysis tool such as Citrix CDFAnalyzer? If we know that the problem happened just before the tracing was stopped we can look at the last few such files from the file sequence (although we recommend a circular trace here). Otherwise we can convert them into CVS files and import into Excel which also supports adjoint threading.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in CDF Analysis Tips and Tricks, Debugging, Software Trace Analysis, Software Trace Analysis Tips and Tricks, Software Trace Reading, Trace Analysis Patterns | No Comments »