Archive for the ‘Log Analysis’ Category
Thursday, October 17th, 2019
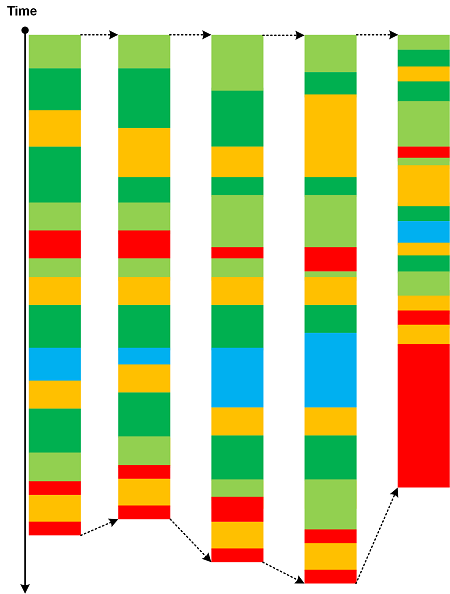
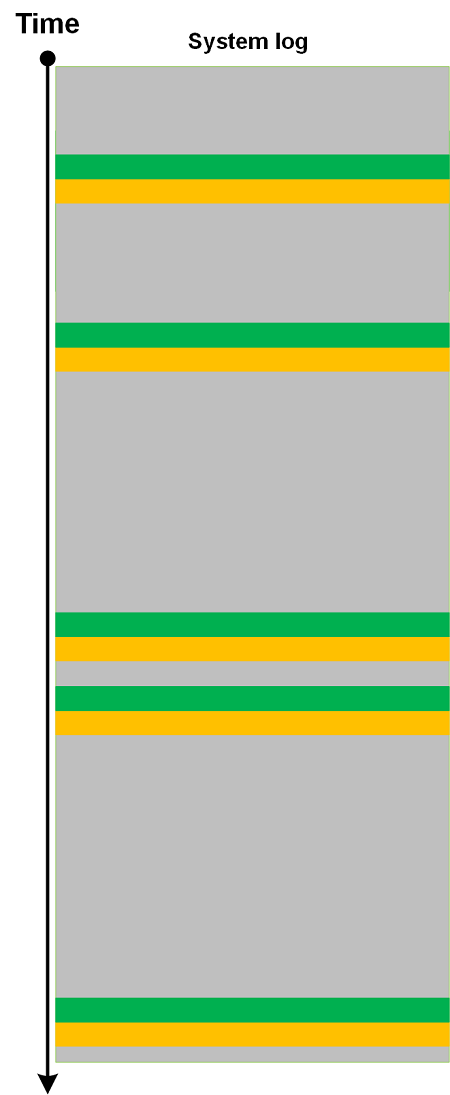
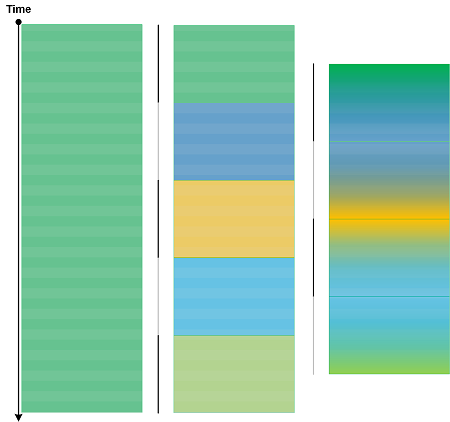
Traces and logs may show drastic qualitative and quantitative pattern changes. We call this analysis pattern Phase Transition by analogy with phase transitions in physical, biological and other complex systems. Usually the goal of the analysis is to find a parameter that caused such transition. Here are a few examples which are self-explanatory.
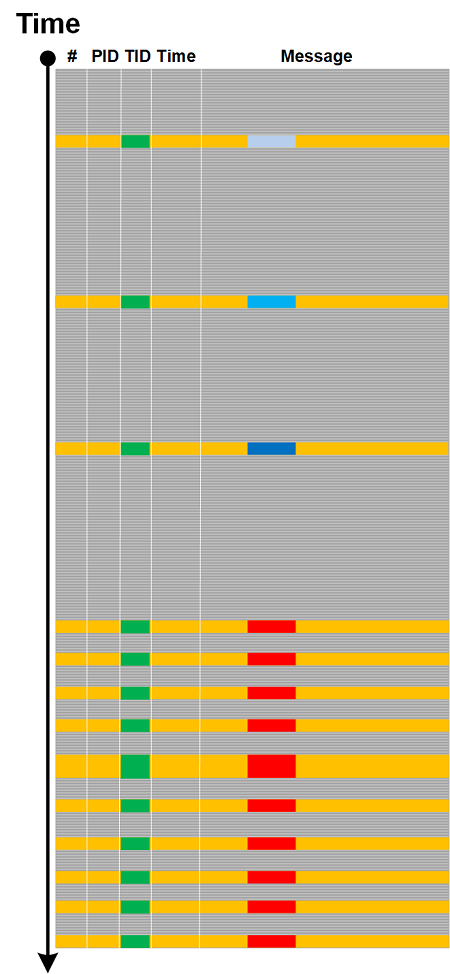
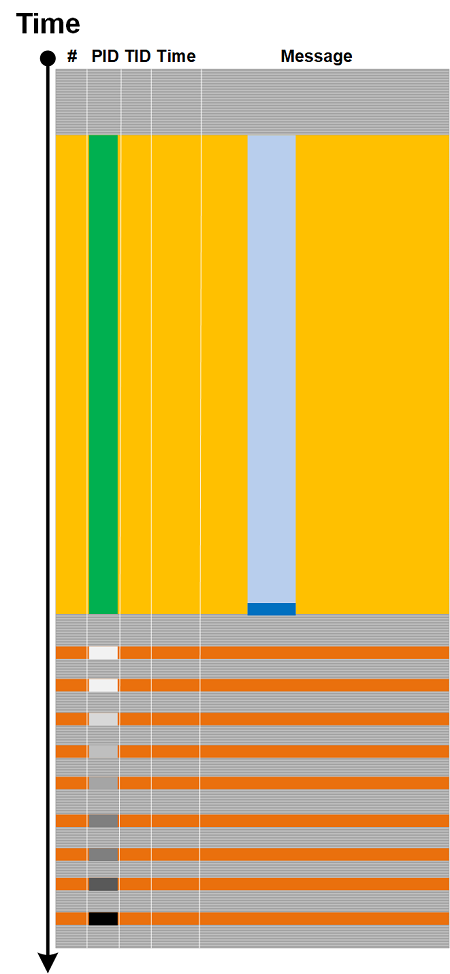
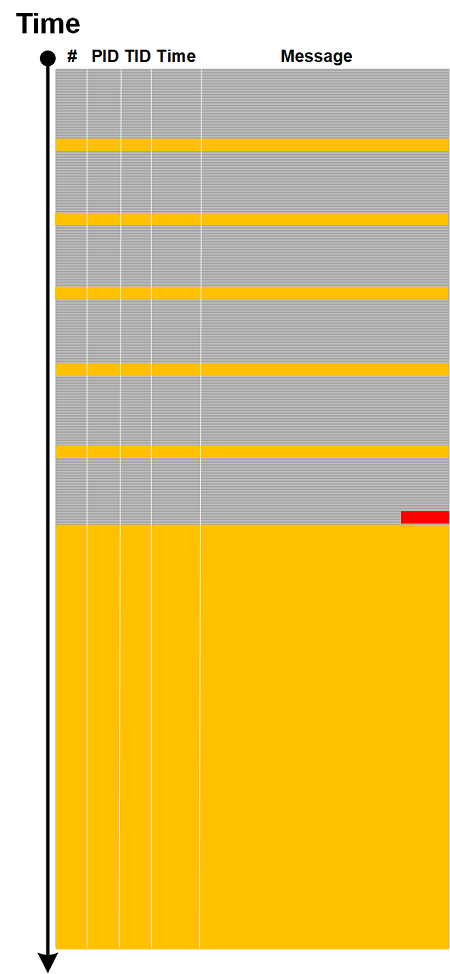
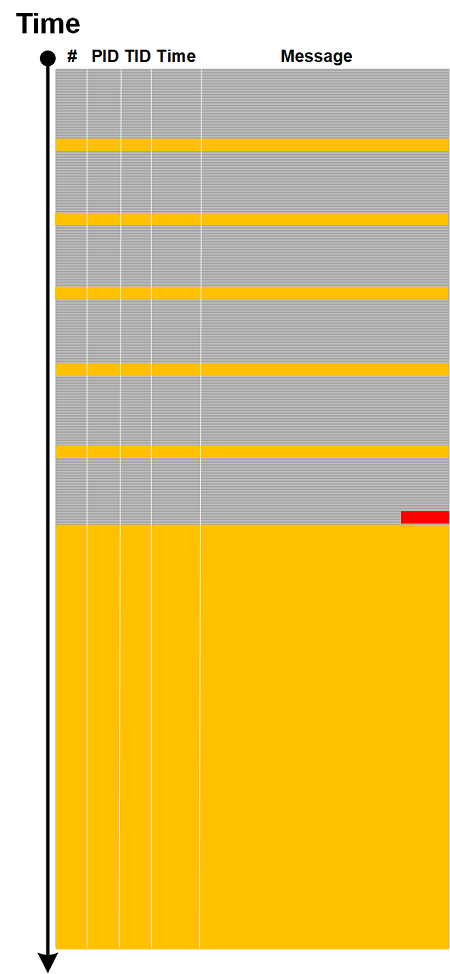
Change in Statement Density and Current:
Sudden proliferation of (Adjoint) Threads of Activity:
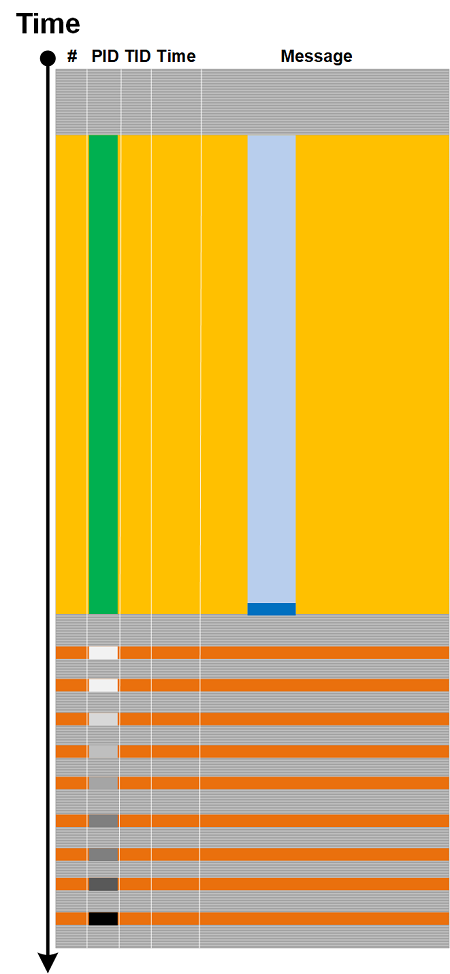
Discontinuity of Activity Region with only Drone Messages left:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Physics | No Comments »
Wednesday, October 2nd, 2019
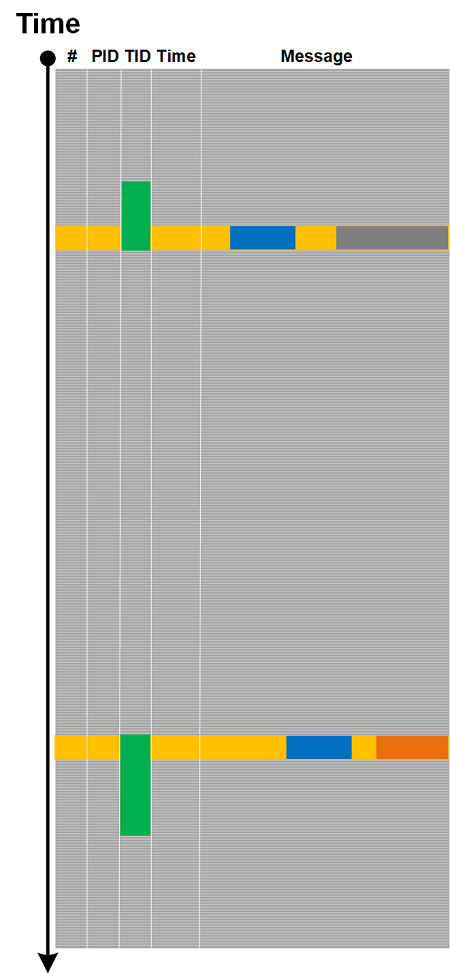
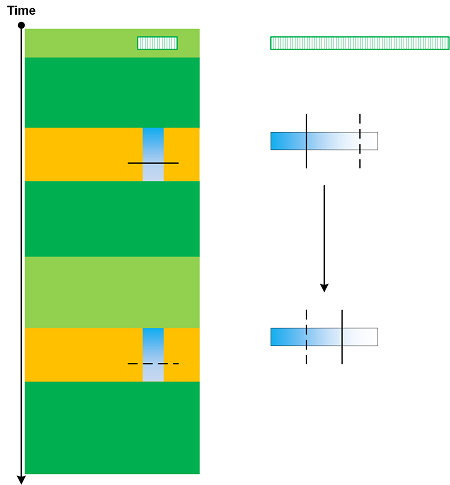
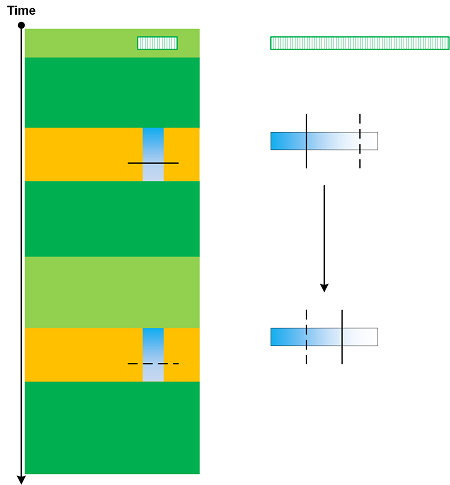
Depending on tracing architecture we may have trace or log messages split into several statements. For example, some API and library tracing tools may log a function call after it returns with a result, but some tools or tracing libraries may log calls in the context of corresponding threads and, therefore, be preempted by other tracing and logging threads, and even interrupted. In the latter cases we may have Split Message like depicted in the following diagram:
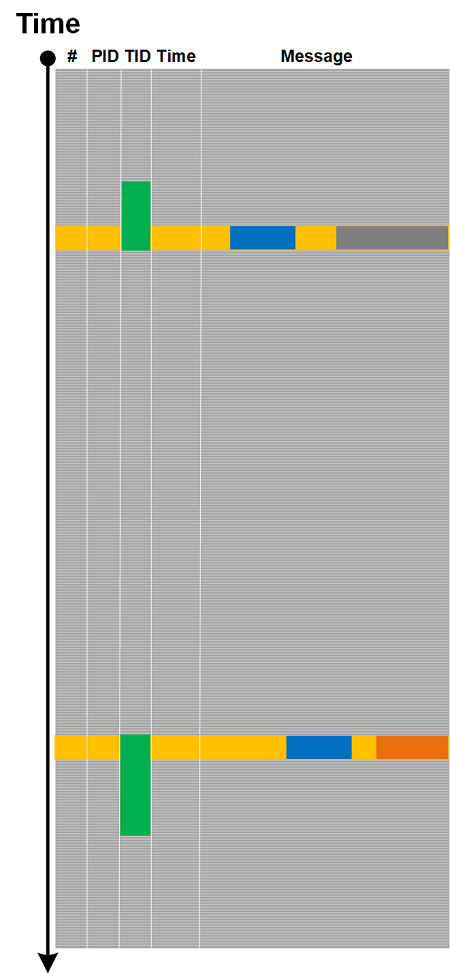
Typical example here is Linux strace. We can recognize such messages by their Message Invariant and Ornament.
Split Message is different from Opposition Messages analysis pattern where we have messages logged from different source code tracing statements, when, for example, a function call result is logged separately. But, in the same vein, when we see an unfinished Split Message we may assume some sort of Discontinuity.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Linux Tracing and Logging, Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Sunday, September 15th, 2019
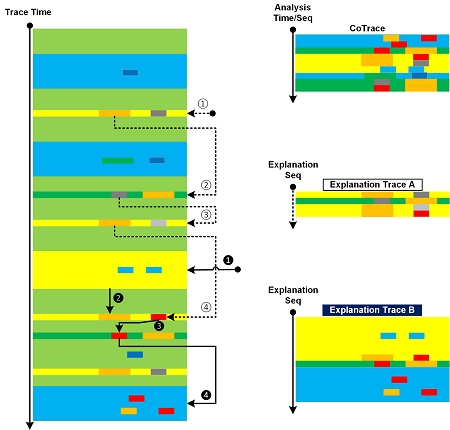
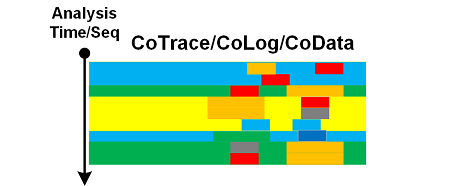
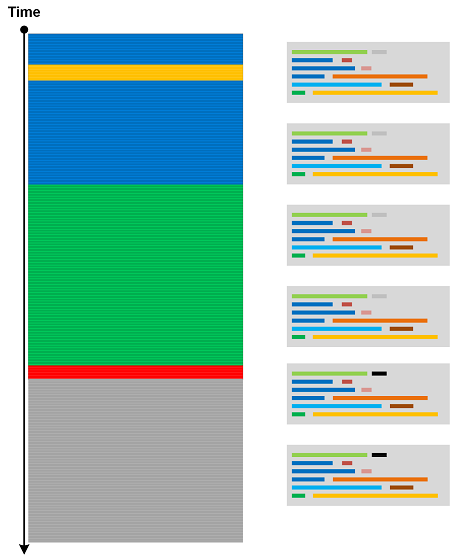
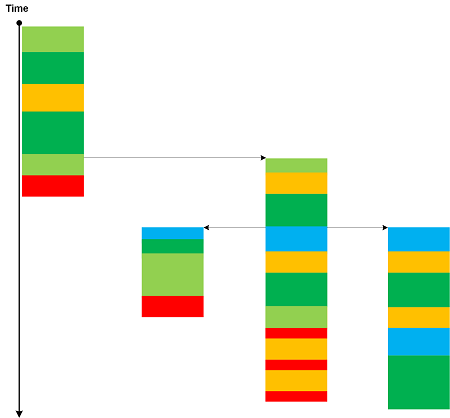
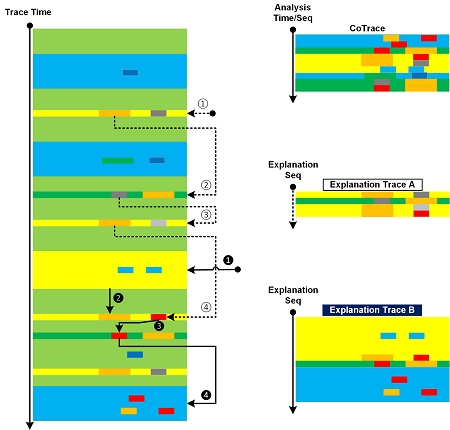
When we analyze a trace or log we may produce CoTrace of analyzed messages and visited regions. But the ultimate goal of any trace and log analysis is to construct the explanation of the observed behavoir to justify the root cause analysis and the proposed mechanism. There may be several proposed explanations each having a different set of messages from the analyzed trace that illustrate them. We call them Explanation Traces. This is illustrated in the picture where we use the same trace from CoTrace analysis pattern.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Pathology, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Tuesday, July 30th, 2019
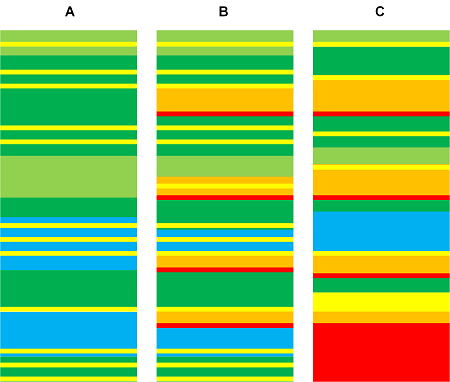
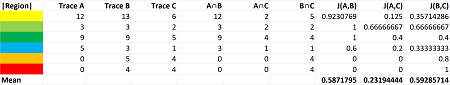
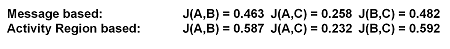
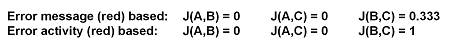
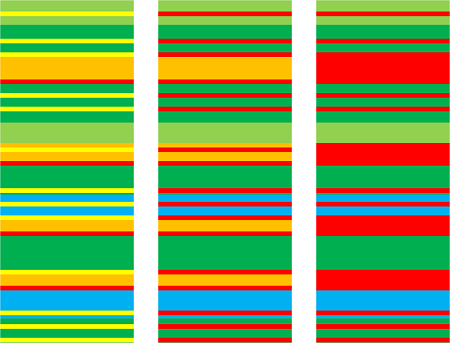
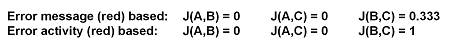
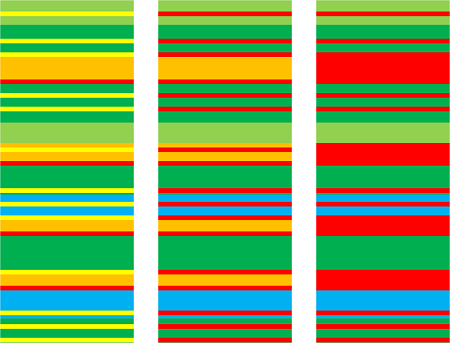
Trace Similarity analysis pattern uses various similarity measures to assess the closeness of one trace or log to another. Here we provide an illustrative example using Jaccard index. Consider three simple logs where sample sets consist from Activity Regions:
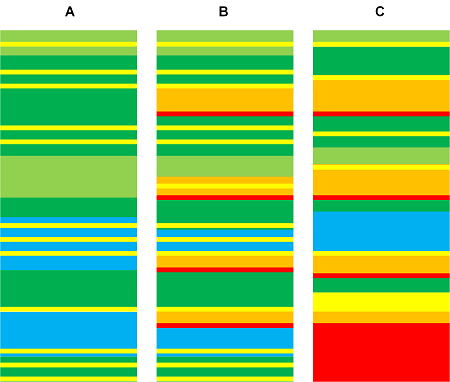
The following table shows calculation of similarity between A and B, A and C, and B and C:
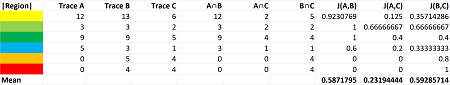
It’s possible to use sample sets consisting of messages instead. For our toy example we get similar index numbers:
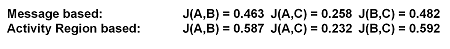
We get different indexes though for individual regions and messages, for example:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Anomaly Detection, Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Topology | No Comments »
Saturday, July 27th, 2019
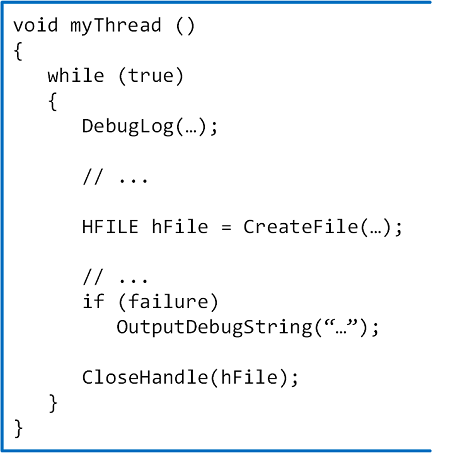
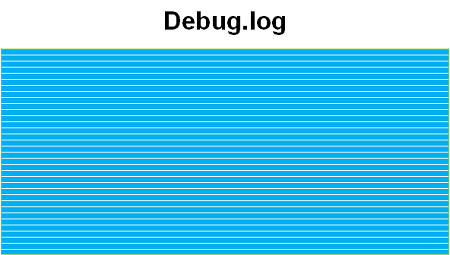
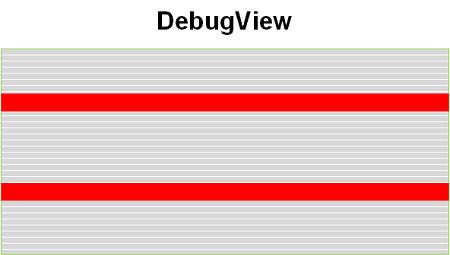
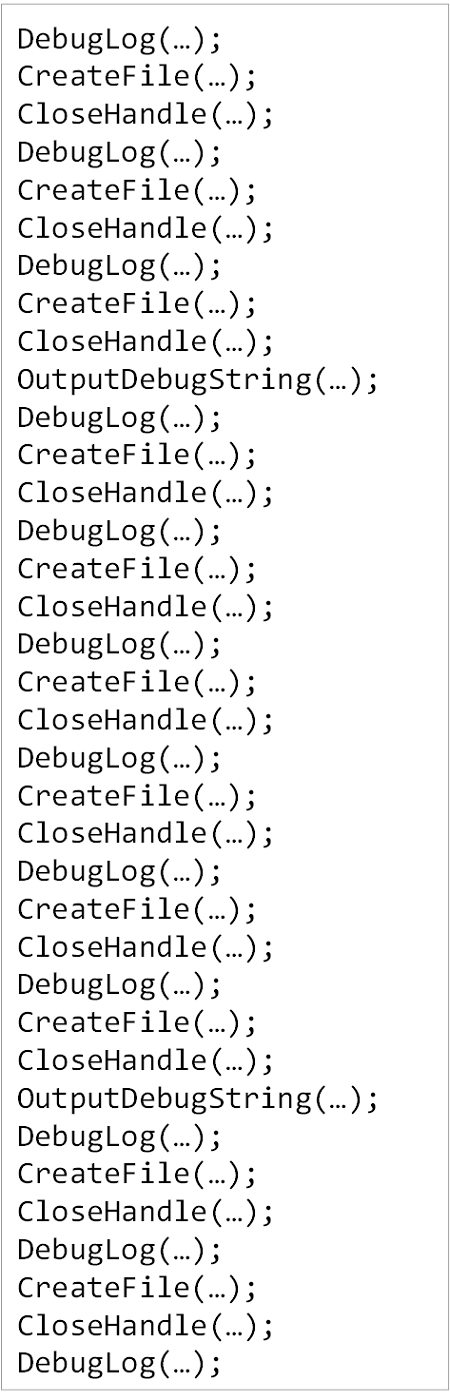
In addition to Declarative Trace we have code statements that may be intercepted by external API tracing tools (CreateFile, CloseHandle):
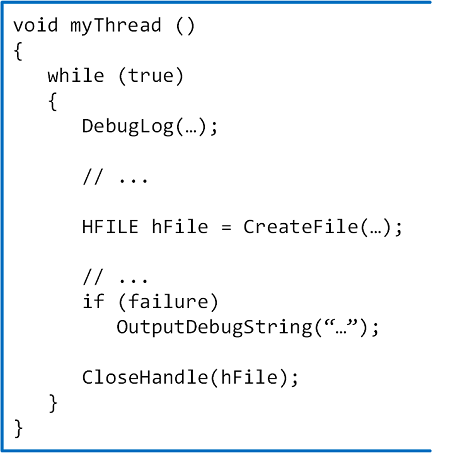
In the sample code above we have different logs resulted from Declarative Trace (DebugLog, OutputDebugString):
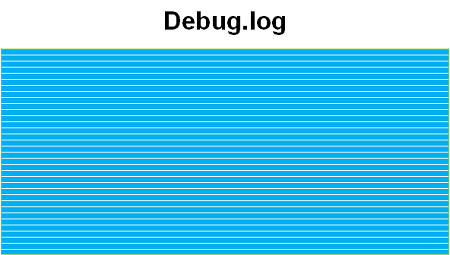
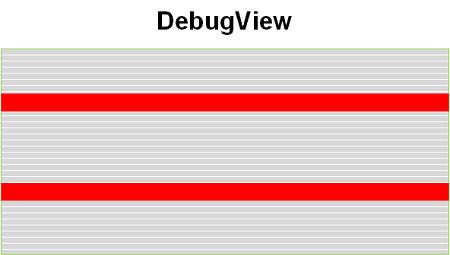
In addition, we have a log saved by an external tracing tool (for example, Process Monitor) that includes our API calls:
All such trace-generating source code statements form Moduli Trace as soon as they are executed:
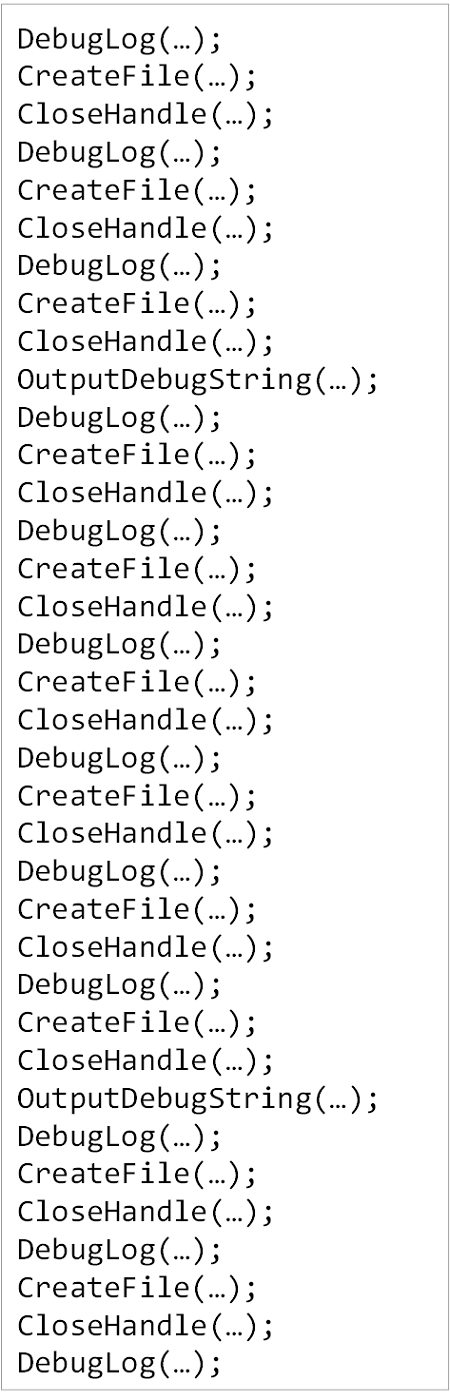
Such a trace can also be analyzed using trace and log analysis patterns like other trace types. We took the idea of this analysis pattern from moduli spaces in mathematics that parametrize other spaces.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Topology | No Comments »
Sunday, July 21st, 2019
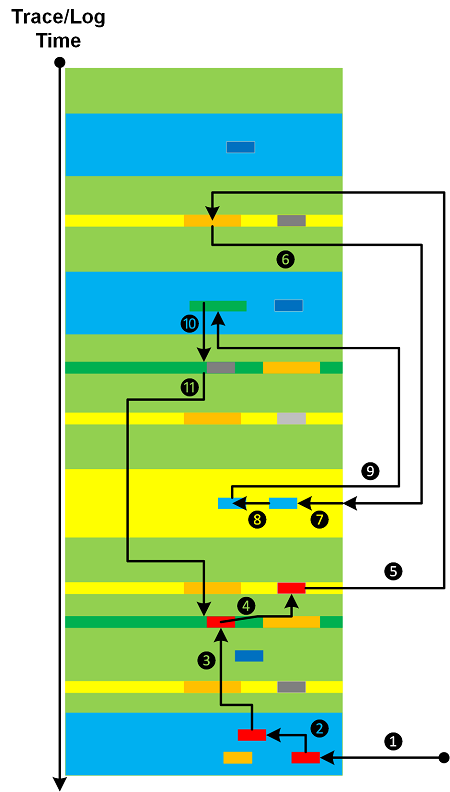
When we do trace and log analysis (and software data in general) we look at specific messages found from search (Message Patterns), Error Messages, Significant Events, visit Activity Regions, filter Message Sets, walk through (Adjoint) Threads of Activity, and do other actions necessitated by trace and log analysis patterns. All these can be done in random order (starting from some analysis point), not necessarily representing the flow of Time or some other metric:
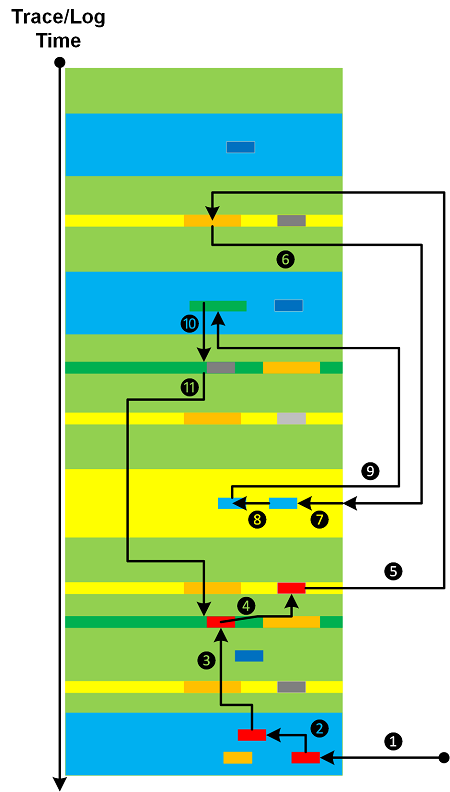
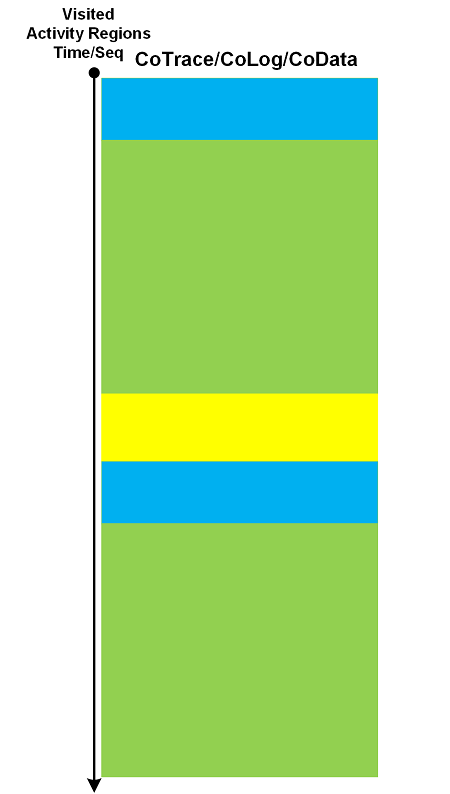
Analyzed messages form their own analysis trace that we call CoTrace (CoLog, CoData) where the prefix Co- denotes a space dual to trace (log, data) space:
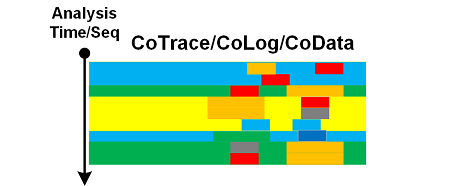
Instead of messages (or in addition to) we can also form CoTraces consisting of visited Activity Regions or some other areas:
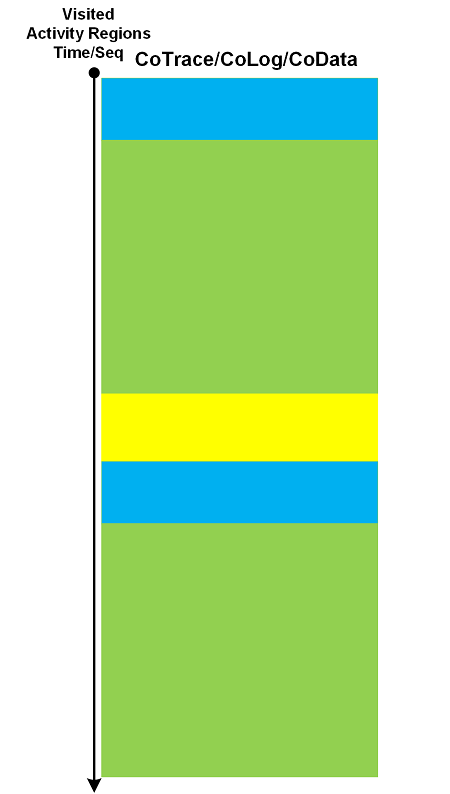
We can apply trace analysis patterns to CoTraces as well. The latter can also be used in creation of higher-order pattern narratives.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Narratology, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Saturday, July 20th, 2019
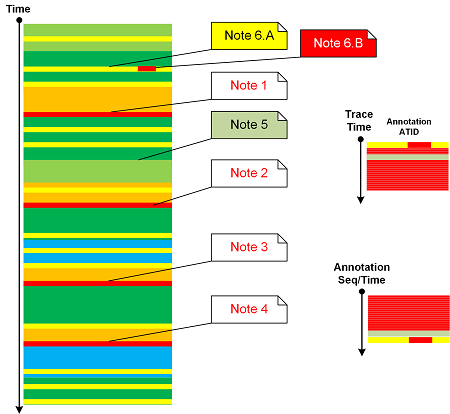
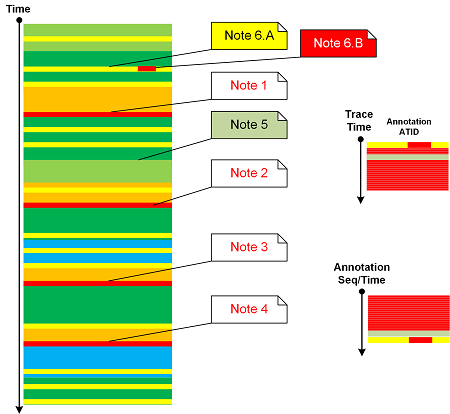
Message Annotations analysis pattern was on our list for years so it’s time to add it to trace and log analysis pattern catalog. We also allow several annotations per trace message done at different times and annotating different parts depending on the analysis flow (the topic of the next analysis pattern). Attached to log messages annotations form their own Adjoint Thread of Activity. However, sorted by their annotation time or sequence we get a different trace that we call Annotation Trace (an example of analysis narrative). We can apply all relevant analysis patterns to both traces. A sketch of this pattern is depicted in the following diagram:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Tuesday, July 16th, 2019
Cartesian Trace analysis pattern has its analogical roots in Cartesian product. It covers a case where we have a long trace and a few Small DA+TA configuration traces (files). The former trace messages are associated with the latter messages (content or content changes) as depicted in the following diagram:
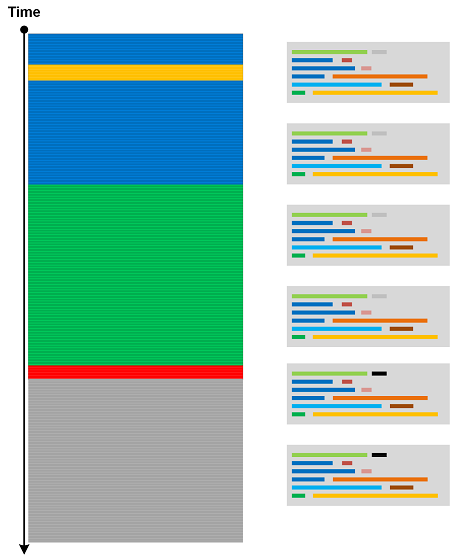
Think about a rectangle as a product of two line fragments or a cylinder as a product of a circle and a line fragment. Both traces are completely independent in comparison to Fiber Bundle, Trace Presheaf, or Trace Extension.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Sunday, July 14th, 2019
Some trace and log messages may have different grammatical structure and content but similar semantics. Therefore, we can create a table listing equivalent messages (using some equivalence relation) and use it to construct simpler traces and logs as depicted in this picture:
One trivial example of Equivalent Messages analysis pattern is Quotient Trace. Another example is Inter-Correlational analysis of logs that have different structure and format. In such a case Equivalent Messages simplify the analysis of higher Trace Dimensions.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Topology | No Comments »
Wednesday, July 10th, 2019
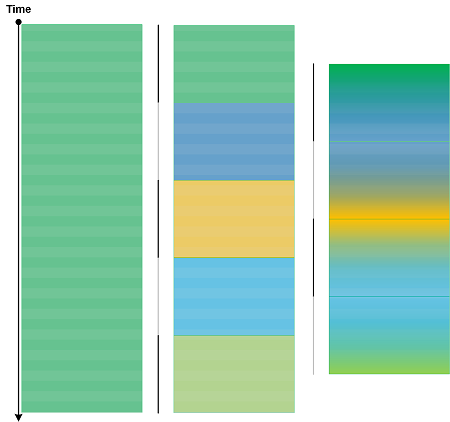
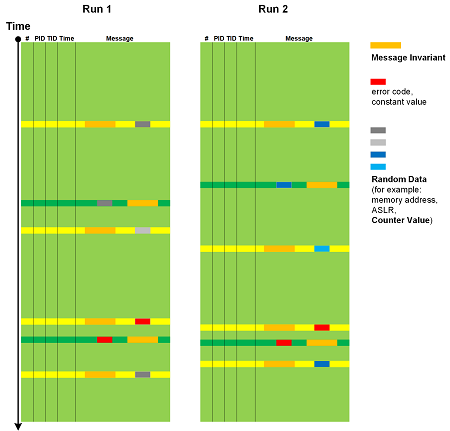
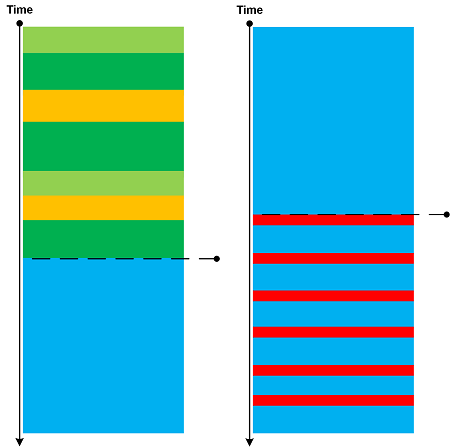
Log message “frequencies” in time domain (Statement Current part) are addressed by Fourier Activity analysis pattern. However, we may have varying message density (Statement Density part) across different trace runs (space domain, irrespective of time irregularities):
According to OED, in computing and mathematics a string means “a linear sequence of records or data” and “a sequence of symbols or linguistic elements in a definite order”. So we propose to name this pattern that analyzes densities of messages or Activity Regions as Trace String. Such longitudinal “vibrations” can be compared and analyzed for anomalies across different log runs (Inter-Correlation) or across similar regions in the same log (Intra-Correlation). Here we consider message density change as a one-dimensional displacement. The analogy for this pattern came from one-dimensional vibrating strings (dual resonance model from 1969-70 by Nambu, Nielsen, and Leonard Susskind).
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Physics | No Comments »
Monday, May 27th, 2019
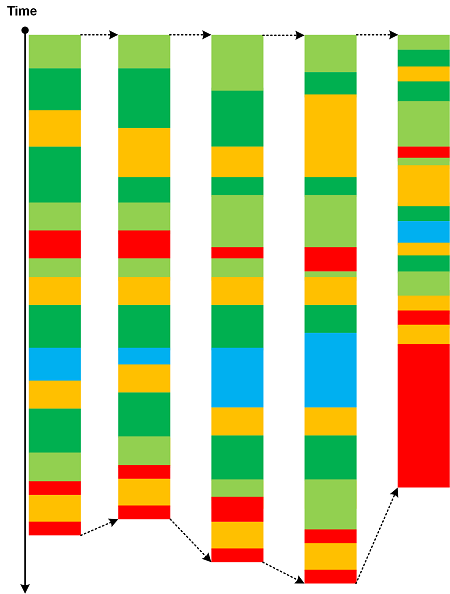
The advent of virtualization simplified the debugging of complex issues by allowing to save the snapshot of the execution environment and then resume it from the save point of execution. This allows continuing tracing using a different set of environmental conditions and input data. New tracing continuations constitute a network that we call Polytrace:
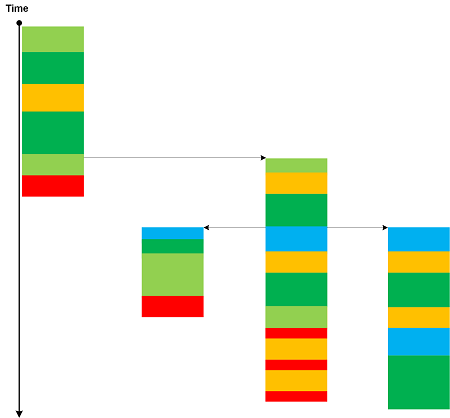
Bifurcation Point for two identical trace beginnings may be considered as an example of a simple Polytrace.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns, Virtualization | 1 Comment »
Monday, May 6th, 2019
Every trace and log has its own set of constants, values that belong to global namespace such as true/false, NULL, Abnormal Values, and common error constants such as “access denied”. Trace Constants may be dependent upon Implementation Discourse. There are also constant values that are local to each trace, for example, user names and IP addresses. They may be constantly repeated in one log but may change for another log. Constants that belong to local namespace may be a part of Vocabulary Index and Basic Facts. Usually Trace Constant is not considered Message Invariant.

- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Sunday, April 7th, 2019
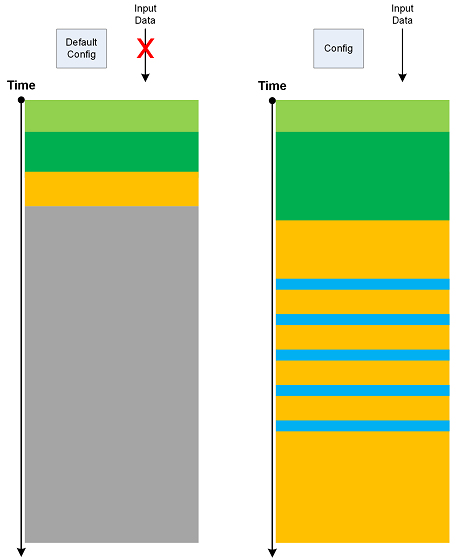
If we run software with its default configuration and no interaction (input data) we get its Minimal Trace:
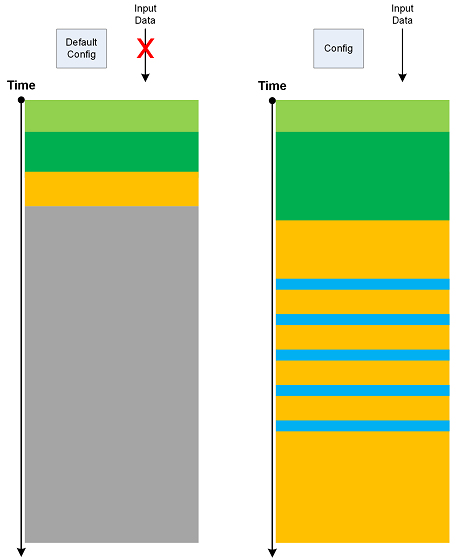
Such traces may have their own Master Trace. Also, Minimal Trace is a specific Use Case Trail. Metaphorically, they can be considered as minimal surfaces.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Geometry | No Comments »
Sunday, March 31st, 2019
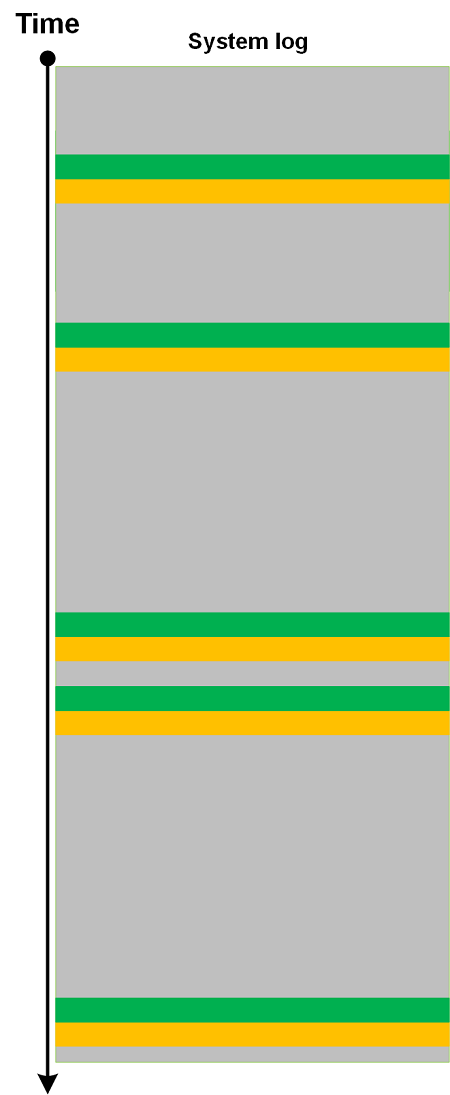
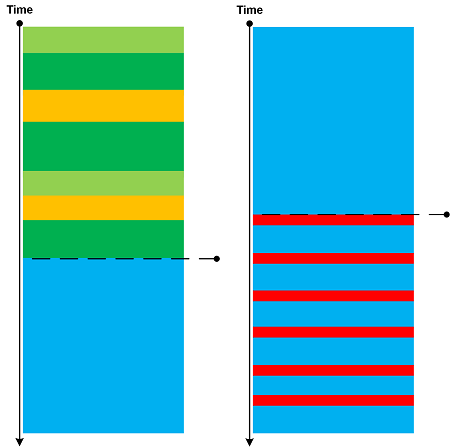
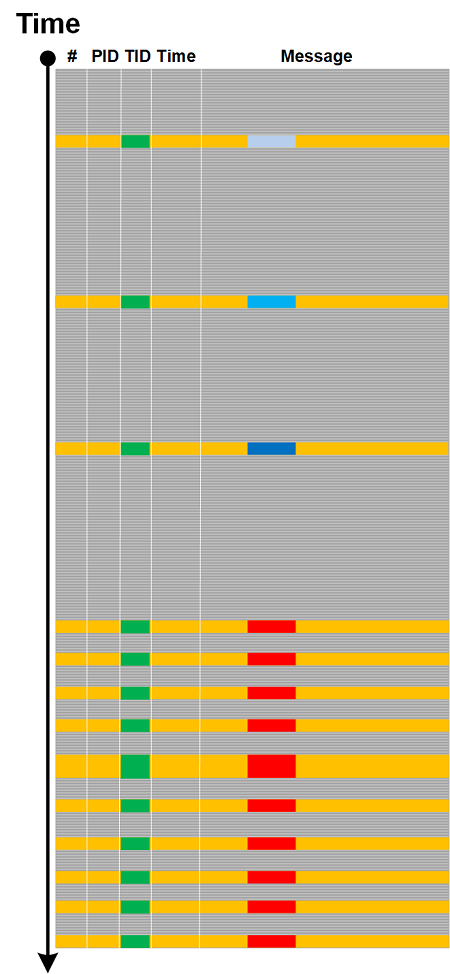
Sometimes we see a constantly repeated message throughout a trace or log (a trivial Periodic Message Block) with constant Time Delta. In certain trace forms (without explicit timing information) such messages may indicate internal time references as illustrated in the following diagram:

We name this pattern Drone Message based on analogy with Drone effect in music.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Music | No Comments »
Tuesday, March 26th, 2019
Based on a mathematical analogy with critical points in topology (Morse theory) we introduce Critical Points in trace and log analysis where they signify the change of trace or log “shape” (topological or “geometric” properties) as illustrated in the following diagram:
Such a point may be an individual message, its Message Context, or Activity Region.
Critical Points are examples of Intra-Correlation whereas Bifurcation Points are examples of Inter-Correlation.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Mathematics of Debugging, Software Trace Analysis, Trace Analysis Patterns, Trace Analysis and Topology | No Comments »
Saturday, November 17th, 2018
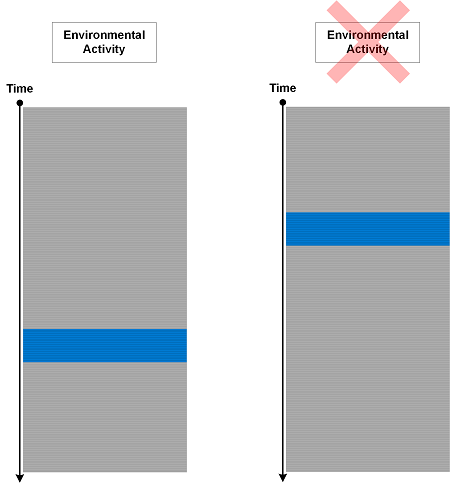
Sometimes we put trace statements to track responses to certain environmental actions and conditions but surprised to see them in logs when nothing happened outside that could have triggered them:
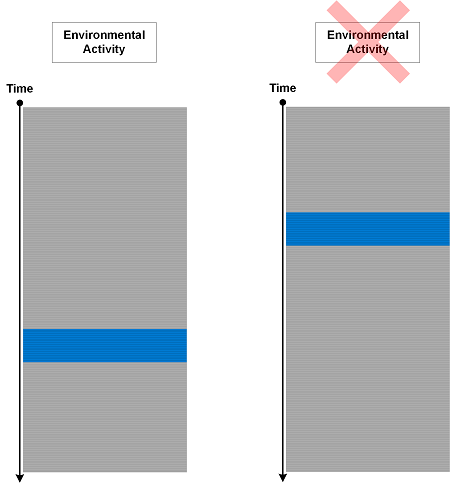
We call such an analysis pattern Phantom Activity. This is an indicator that internal program state was not updated correctly. The difference between such activities and Defamiliarizing Effect is that the former messages are expected but not in their current Message Context.
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Debugging, Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Sunday, October 14th, 2018
When we have very large traces (including Split Traces) we can use the concept of sharding to split a log into several shards for parallel processing. However, some patterns may require the analysis across the boundary of shards. Trace Sharding is illustrated in the following diagram:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Saturday, October 13th, 2018
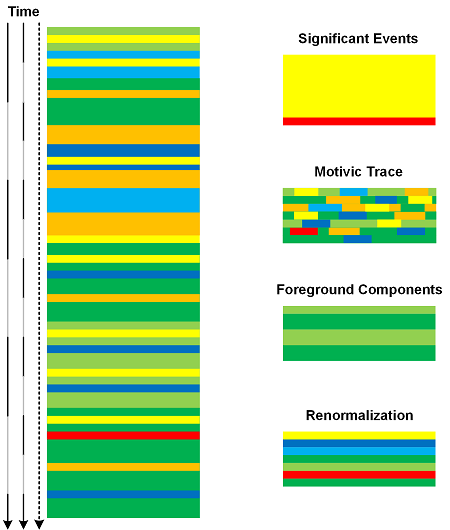
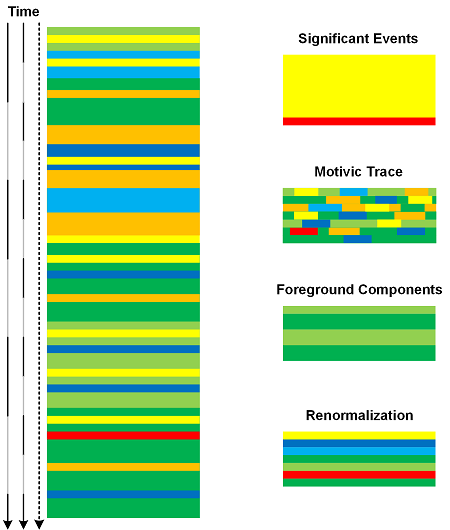
A software trace or log can be analyzed using different Time Scales. The coarser the scale the more messages are included in time intervals. Such per interval Message Sets can be analyzed and transformed into one message using analysis patterns such as Significant Event, Motivic Trace, Background and Foreground Components, and Renormalization. The resulted new trace will be a scaled version of the original trace as depicted in the following diagram:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Sunday, October 7th, 2018
The data in individual messages and in State Dump message blocks may be truncated. This is similar to Visibility Limit at the log message level. When data values are sorted and resorted this may result in “hidden” data replacing the previously “visible” data and vice versa as shown in the following diagram:
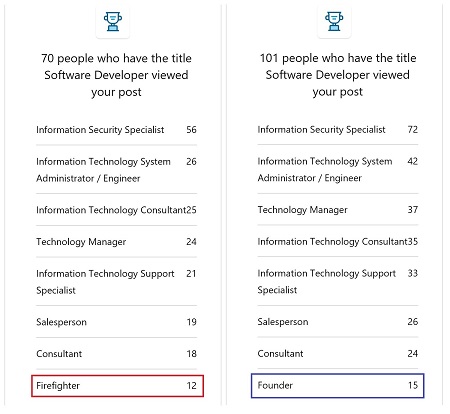
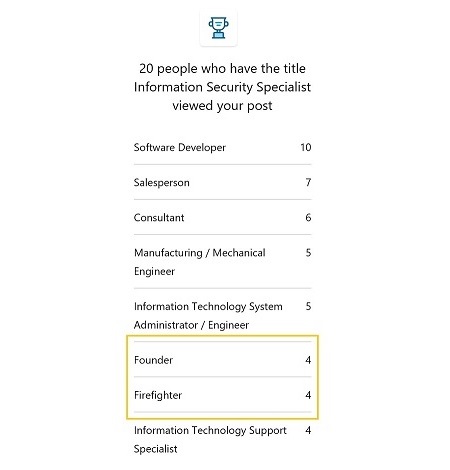
This pattern (Truncated Data) was conceived after we observed the change of data key in sequence of a LinkedIn post (not related to firefighting) stats sorted by value and thought that was “strange”:
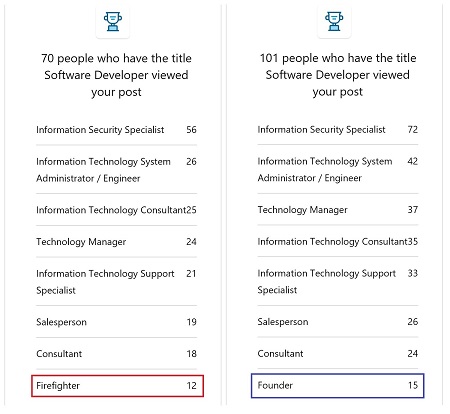
However, stats from the other post showed the both keys were valid:
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »
Saturday, September 29th, 2018
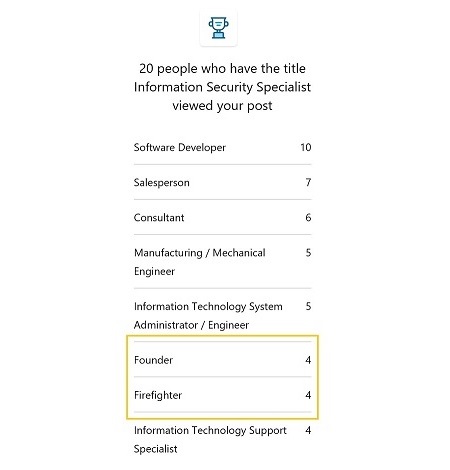
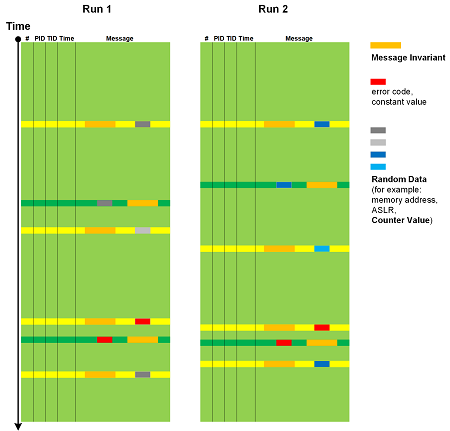
Trace and log message text usually consists of constant unchanging Message Invariants and some varying data. The latter can be classified into Random Data such as memory addresses, especially when ASLR is enabled, Counter Values, and variable data but constant in nature, such as error values and NULL pointer. Individual values from Signals are not considered random but their sequence can be. This analysis pattern is depicted in the following diagram (adopted from Data Association analysis pattern):
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -
Posted in Log Analysis, Software Trace Analysis, Trace Analysis Patterns | No Comments »