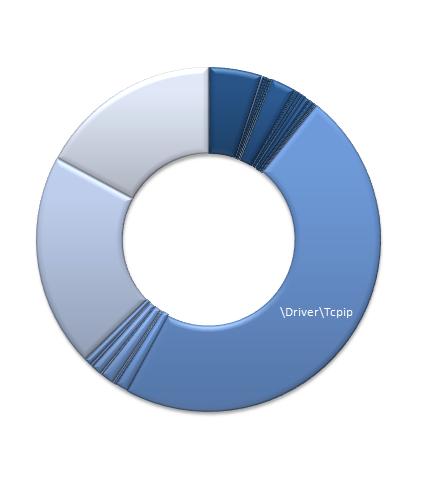
Google Analytics shows the following crash dump analysis pattern frequencies to be fully analyzed later next week:
|
Page
|
Pageviews
|
|
http://www.dumpanalysis.org/blog/index.php/2006/10/30/crash-dump-analysis-patterns-part-1/
|
8086
|
|
http://www.dumpanalysis.org/blog/index.php/2006/10/31/crash-dump-analysis-patterns-part-2/
|
7709
|
|
http://www.dumpanalysis.org/blog/index.php/2007/07/20/crash-dump-analysis-patterns-part-17/
|
6131
|
|
http://www.dumpanalysis.org/blog/index.php/2007/04/03/crash-dump-analysis-patterns-part-11/
|
5000
|
|
http://www.dumpanalysis.org/blog/index.php/2008/03/13/crash-dump-analysis-patterns-part-2b/
|
4651
|
|
http://www.dumpanalysis.org/blog/index.php/2007/02/09/crash-dump-analysis-patterns-part-9a/
|
3881
|
|
http://www.dumpanalysis.org/blog/index.php/2008/01/24/crash-dump-analysis-patterns-part-43/
|
3782
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/12/crash-dump-analysis-patterns-part-59b/
|
3666
|
|
http://www.dumpanalysis.org/blog/index.php/2007/12/17/crash-dump-analysis-patterns-part-41b/
|
3446
|
|
http://www.dumpanalysis.org/blog/index.php/2007/08/06/crash-dump-analysis-patterns-part-20a/
|
3190
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/02/crash-dump-analysis-patterns-part-13c/
|
2785
|
|
http://www.dumpanalysis.org/blog/index.php/2007/02/02/crash-dump-analysis-patterns-part-8/
|
2673
|
|
http://www.dumpanalysis.org/blog/index.php/2007/06/21/crash-dump-analysis-patterns-part-16a/
|
2629
|
|
http://www.dumpanalysis.org/blog/index.php/2007/09/14/crash-dump-analysis-patterns-part-27/
|
2461
|
|
http://www.dumpanalysis.org/blog/index.php/2006/11/01/crash-dump-analysis-patterns-part-3/
|
2442
|
|
http://www.dumpanalysis.org/blog/index.php/2008/04/28/crash-dump-analysis-patterns-part-6a/
|
2377
|
|
http://www.dumpanalysis.org/blog/index.php/2008/04/03/crash-dump-analysis-patterns-part-57/
|
2376
|
|
http://www.dumpanalysis.org/blog/index.php/2008/03/18/crash-dump-analysis-patterns-part-13e/
|
2279
|
|
http://www.dumpanalysis.org/blog/index.php/2007/09/11/crash-dump-analysis-patterns-part-26/
|
2264
|
|
http://www.dumpanalysis.org/blog/index.php/2006/12/18/crash-dump-analysis-patterns-part-6/
|
2257
|
|
http://www.dumpanalysis.org/blog/index.php/2007/09/10/crash-dump-analysis-patterns-part-25/
|
2185
|
|
http://www.dumpanalysis.org/blog/index.php/2007/10/17/crash-dump-analysis-patterns-part-31/
|
2126
|
|
http://www.dumpanalysis.org/blog/index.php/2008/10/15/crash-dump-analysis-patterns-part-1b/
|
1982
|
|
http://www.dumpanalysis.org/blog/index.php/2007/07/15/crash-dump-analysis-patterns-part-13b/
|
1891
|
|
http://www.dumpanalysis.org/blog/index.php/2007/08/19/crash-dump-analysis-patterns-part-23a/
|
1846
|
|
http://www.dumpanalysis.org/blog/index.php/2007/08/19/crash-dump-analysis-patterns-part-20b/
|
1699
|
|
http://www.dumpanalysis.org/blog/index.php/2006/12/15/crash-dump-analysis-patterns-part-5/
|
1520
|
|
http://www.dumpanalysis.org/blog/index.php/2007/12/12/crash-dump-analysis-patterns-part-41a/
|
1511
|
|
http://www.dumpanalysis.org/blog/index.php/2007/07/28/crash-dump-analysis-patterns-part-9c/
|
1485
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/21/crash-dump-analysis-patterns-part-37/
|
1457
|
|
http://www.dumpanalysis.org/blog/index.php/2007/05/09/crash-dump-analysis-patterns-part-13a/
|
1388
|
|
http://www.dumpanalysis.org/blog/index.php/2007/05/11/crash-dump-analysis-patterns-part-14/
|
1366
|
|
http://www.dumpanalysis.org/blog/index.php/2007/07/03/crash-dump-analysis-patterns-part-9b/
|
1336
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/05/crash-dump-analysis-patterns-part-33/
|
1314
|
|
http://www.dumpanalysis.org/blog/index.php/2008/04/09/crash-dump-analysis-patterns-part-58a/
|
1293
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/29/crash-dump-analysis-patterns-part-9d/
|
1213
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/10/crash-dump-analysis-patterns-part-16b/
|
1213
|
|
http://www.dumpanalysis.org/blog/index.php/2008/07/11/crash-dump-analysis-patterns-part-71/
|
1156
|
|
http://www.dumpanalysis.org/blog/index.php/2008/05/20/crash-dump-analysis-patterns-part-61/
|
1131
|
|
http://www.dumpanalysis.org/blog/index.php/2007/12/19/crash-dump-analysis-patterns-part-42b/
|
1063
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/27/crash-dump-analysis-patterns-part-53/
|
1061
|
|
http://www.dumpanalysis.org/blog/index.php/2007/01/24/crash-dump-analysis-patterns-part-7/
|
1031
|
|
http://www.dumpanalysis.org/blog/index.php/2008/10/25/crash-dump-analysis-patterns-part-9e/
|
1016
|
|
http://www.dumpanalysis.org/blog/index.php/2007/07/22/crash-dump-analysis-patterns-part-19/
|
998
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/23/crash-dump-analysis-patterns-part-39/
|
979
|
|
http://www.dumpanalysis.org/blog/index.php/2007/08/25/crash-dump-analysis-patterns-part-23b/
|
955
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/04/crash-dump-analysis-patterns-part-13d/
|
948
|
|
http://www.dumpanalysis.org/blog/index.php/2007/10/15/crash-dump-analysis-patterns-part-30/
|
923
|
|
http://www.dumpanalysis.org/blog/index.php/2008/10/21/crash-dump-analysis-patterns-part-77/
|
905
|
|
http://www.dumpanalysis.org/blog/index.php/2006/11/03/crash-dump-analysis-patterns-part-4/
|
889
|
|
http://www.dumpanalysis.org/blog/index.php/2007/07/20/crash-dump-analysis-patterns-part-18/
|
879
|
|
http://www.dumpanalysis.org/blog/index.php/2007/04/20/crash-dump-analysis-patterns-part-5b/
|
870
|
|
http://www.dumpanalysis.org/blog/index.php/2007/04/20/crash-dump-analysis-patterns-part-12/
|
820
|
|
http://www.dumpanalysis.org/blog/index.php/2007/05/24/crash-dump-analysis-patterns-part-15/
|
798
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/20/crash-dump-analysis-patterns-part-31a/
|
769
|
|
http://www.dumpanalysis.org/blog/index.php/2008/04/29/crash-dump-analysis-patterns-part-60/
|
758
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/19/crash-dump-analysis-patterns-part-51/
|
714
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/22/crash-dump-analysis-patterns-part-38/
|
712
|
|
http://www.dumpanalysis.org/blog/index.php/2008/03/11/crash-dump-analysis-patterns-part-55/
|
702
|
|
http://www.dumpanalysis.org/blog/index.php/2007/12/14/crash-dump-analysis-patterns-part-42a/
|
693
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/13/crash-dump-analysis-patterns-part-49/
|
678
|
|
http://www.dumpanalysis.org/blog/index.php/2008/04/22/crash-dump-analysis-patterns-part-59/
|
676
|
|
http://www.dumpanalysis.org/blog/index.php/2009/01/05/crash-dump-analysis-patterns-part-13f/
|
624
|
|
http://www.dumpanalysis.org/blog/index.php/2007/08/30/crash-dump-analysis-patterns-part-24/
|
621
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/12/crash-dump-analysis-patterns-part-48/
|
619
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/24/crash-dump-analysis-patterns-part-67/
|
618
|
|
http://www.dumpanalysis.org/blog/index.php/2007/10/23/crash-dump-analysis-patterns-part-32/
|
616
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/28/crash-dump-analysis-patterns-part-54/
|
611
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/22/crash-dump-analysis-patterns-part-52/
|
610
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/06/crash-dump-analysis-patterns-part-63/
|
596
|
|
http://www.dumpanalysis.org/blog/index.php/2007/08/12/crash-dump-analysis-patterns-part-21/
|
576
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/25/crash-dump-analysis-patterns-part-67b/
|
547
|
|
http://www.dumpanalysis.org/blog/index.php/2007/12/10/crash-dump-analysis-patterns-part-40a/
|
531
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/14/crash-dump-analysis-patterns-part-36/
|
529
|
|
http://www.dumpanalysis.org/blog/index.php/2008/07/10/crash-dump-analysis-patterns-part-19b/
|
516
|
|
http://www.dumpanalysis.org/blog/index.php/2007/08/16/crash-dump-analysis-patterns-part-22/
|
511
|
|
http://www.dumpanalysis.org/blog/index.php/2007/10/08/crash-dump-analysis-patterns-part-29/
|
506
|
|
http://www.dumpanalysis.org/blog/index.php/2008/08/07/crash-dump-analysis-patterns-part-75/
|
500
|
|
http://www.dumpanalysis.org/blog/index.php/2008/01/22/crash-dump-analysis-patterns-part-42c/
|
496
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/20/crash-dump-analysis-patterns-part-66/
|
493
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/19/crash-dump-analysis-patterns-part-64/
|
492
|
|
http://www.dumpanalysis.org/blog/index.php/2007/03/19/crash-dump-analysis-patterns-part-10/
|
450
|
|
http://www.dumpanalysis.org/blog/index.php/2009/04/14/crash-dump-analysis-patterns-part-6b/
|
448
|
|
http://www.dumpanalysis.org/blog/index.php/2009/05/15/crash-dump-analysis-patterns-part-84/
|
432
|
|
http://www.dumpanalysis.org/blog/index.php/2008/07/09/crash-dump-analysis-patterns-part-69/
|
427
|
|
http://www.dumpanalysis.org/blog/index.php/2007/09/26/crash-dump-analysis-patterns-part-28/
|
426
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/15/crash-dump-analysis-patterns-part-50/
|
410
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/19/crash-dump-analysis-patterns-part-65/
|
378
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/12/crash-dump-analysis-patterns-part-35/
|
371
|
|
http://www.dumpanalysis.org/blog/index.php/2008/01/25/crash-dump-analysis-patterns-part-44/
|
371
|
|
http://www.dumpanalysis.org/blog/index.php/2008/06/27/crash-dump-analysis-patterns-part-68/
|
370
|
|
http://www.dumpanalysis.org/blog/index.php/2008/08/05/crash-dump-analysis-patterns-part-74/
|
369
|
|
http://www.dumpanalysis.org/blog/index.php/2008/12/17/crash-dump-analysis-patterns-part-42e/
|
351
|
|
http://www.dumpanalysis.org/blog/index.php/2008/07/29/crash-dump-analysis-patterns-part-73/
|
345
|
|
http://www.dumpanalysis.org/blog/index.php/2009/06/23/crash-dump-analysis-patterns-part-85/
|
340
|
|
http://www.dumpanalysis.org/blog/index.php/2008/05/28/crash-dump-analysis-patterns-part-62/
|
337
|
|
http://www.dumpanalysis.org/blog/index.php/2009/07/10/crash-dump-analysis-patterns-part-87/
|
336
|
|
http://www.dumpanalysis.org/blog/index.php/2008/12/01/crash-dump-analysis-patterns-part-78a/
|
330
|
|
http://www.dumpanalysis.org/blog/index.php/2008/07/10/crash-dump-analysis-patterns-part-70/
|
323
|
|
http://www.dumpanalysis.org/blog/index.php/2008/02/06/crash-dump-analysis-patterns-part-47/
|
322
|
|
http://www.dumpanalysis.org/blog/index.php/2008/03/27/crash-dump-analysis-patterns-part-56/
|
317
|
|
http://www.dumpanalysis.org/blog/index.php/2007/11/06/crash-dump-analysis-patterns-part-34/
|
310
|
|
http://www.dumpanalysis.org/blog/index.php/2008/07/26/crash-dump-analysis-patterns-part-72/
|
307
|
|
http://www.dumpanalysis.org/blog/index.php/2008/01/31/crash-dump-analysis-patterns-part-46/
|
299
|
|
http://www.dumpanalysis.org/blog/index.php/2008/11/07/crash-dump-analysis-patterns-part-42d/
|
293
|
|
http://www.dumpanalysis.org/blog/index.php/2008/10/06/crash-dump-analysis-patterns-part-76/
|
288
|
|
http://www.dumpanalysis.org/blog/index.php/2008/01/30/crash-dump-analysis-patterns-part-45/
|
286
|
|
http://www.dumpanalysis.org/blog/index.php/2008/09/10/crash-dump-analysis-patterns-part-29b/
|
270
|
|
http://www.dumpanalysis.org/blog/index.php/2009/02/13/crash-dump-analysis-patterns-part-80/
|
250
|
|
http://www.dumpanalysis.org/blog/index.php/2009/03/09/crash-dump-analysis-patterns-part-82/
|
246
|
|
http://www.dumpanalysis.org/blog/index.php/2009/02/09/crash-dump-analysis-patterns-part-79/
|
231
|
|
http://www.dumpanalysis.org/blog/index.php/2008/05/07/crash-dump-analysis-patterns-part-10a/
|
225
|
|
http://www.dumpanalysis.org/blog/index.php/2009/06/24/crash-dump-analysis-patterns-part-86/
|
207
|
|
http://www.dumpanalysis.org/blog/index.php/2009/02/19/crash-dump-analysis-patterns-part-81/
|
195
|
|
http://www.dumpanalysis.org/blog/index.php/2009/10/28/crash-dump-analysis-patterns-part-90/
|
151
|
|
http://www.dumpanalysis.org/blog/index.php/2009/04/14/crash-dump-analysis-patterns-part-83/
|
146
|
|
http://www.dumpanalysis.org/blog/index.php/2009/12/07/crash-dump-analysis-patterns-part-95/
|
92
|
|
http://www.dumpanalysis.org/blog/index.php/2009/11/24/crash-dump-analysis-patterns-part-93/
|
67
|
|
http://www.dumpanalysis.org/blog/index.php/2009/11/12/crash-dump-analysis-patterns-part-91/
|
46
|
|
http://www.dumpanalysis.org/blog/index.php/2009/10/23/crash-dump-analysis-patterns-part-89/
|
41
|
|
http://www.dumpanalysis.org/blog/index.php/2009/11/30/crash-dump-analysis-patterns-part-94a/
|
39
|
|
http://www.dumpanalysis.org/blog/index.php/2009/11/24/crash-dump-analysis-patterns-part-92/
|
36
|
|
http://www.dumpanalysis.org/blog/index.php/2009/10/23/crash-dump-analysis-patterns-part-88/
|
35
|
|
http://www.dumpanalysis.org/blog/index.php/2009/11/16/crash-dump-analysis-patterns-part-65b/
|
33
|
|
http://www.dumpanalysis.org/blog/index.php/2009/12/30/crash-dump-analysis-patterns-part-13g/
|
20
|