Crash Dump Analysis Patterns (Part 85b)
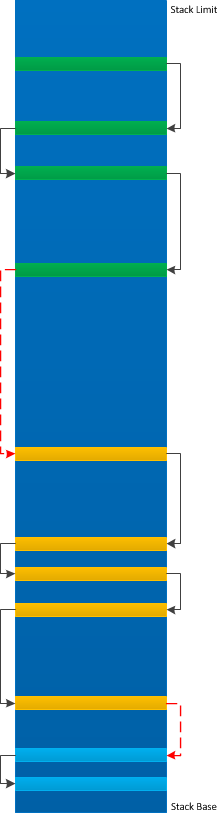
Friday, May 31st, 2013This is a kernel space counterpart of Ubiquitous Component pattern. Such a component especially when it is Top Module can be a sign of Wait Chain(s) and Blocking Module and if it is present in the same process names - a sign of Distributed Wait Chain.
0: kd> !stacks 0 ModuleA
Proc.Thread .Thread Ticks ThreadState Blocker
[fffffa800e673b30 svchost.exe]
534.006240 fffffa801388f5f0 fffd41d9 Blocked ModuleA+0x12468
[fffffa800e705b30 svchost.exe]
630.000e14 fffffa800edacb50 fffdcf7a Blocked ModuleA+0x12468
630.000f04 fffffa8012c2fb50 fffdcf49 Blocked ModuleA+0x12468
630.006610 fffffa80134f5b50 fffdcf46 Blocked ModuleA+0x12468
630.001cfc fffffa800f55a2d0 fffdcf44 Blocked ModuleA+0x12468
630.003db8 fffffa80121f1540 fffdcf43 Blocked ModuleA+0x12468
630.000b9c fffffa80133d1780 fffdcf3c Blocked ModuleA+0x12468
630.0041c4 fffffa8013c77b50 fffdcf43 Blocked ModuleA+0x12468
630.00641c fffffa8012476b50 fffdcf43 Blocked ModuleA+0x12468
630.006424 fffffa8013207b50 fffdcf40 Blocked ModuleA+0x12468
630.002fcc fffffa80128f9060 fffdcf3e Blocked ModuleA+0x12468
630.003de8 fffffa80139edb50 fffdcf3d Blocked ModuleA+0x12468
630.0062c4 fffffa800f5ff2d0 fffdcf3c Blocked ModuleA+0x12468
630.0065e8 fffffa80139dcb50 fffdcf3b Blocked ModuleA+0x12468
630.004524 fffffa8011e51b50 fffdcf3a Blocked ModuleA+0x12468
630.004570 fffffa801346b060 fffdcf39 Blocked ModuleA+0x12468
630.00173c fffffa8010b99b50 fffdcf39 Blocked ModuleA+0x12468
[fffffa800f63db30 iexplore.exe]
24c4.0024c8 fffffa800fe854e0 fffcb6cf Blocked ModuleA+0x12468
[fffffa8010b9ab30 explorer.exe]
2b64.0043d0 fffffa8012e8ab00 fffd9095 Blocked ModuleA+0x12468
[fffffa800fe55060 explorer.exe]
2c80.002e58 fffffa8012e75060 fffba7af Blocked ModuleA+0x12468
[fffffa8010c54b30 iexplore.exe]
2e3c.002e98 fffffa8010c75620 fffcbb7f Blocked ModuleA+0x12468
[fffffa80111c3720 iexplore.exe]
32d8.003230 fffffa80111b1b00 fffd41d9 Blocked ModuleA+0x12468
[fffffa80110cb690 iexplore.exe]
2e74.002854 fffffa8011121b00 fffbe8a4 Blocked ModuleA+0x12468
[fffffa801146cb30 OUTLOOK.EXE]
35cc.0035e8 fffffa8013831b00 fffaf33a Blocked ModuleA+0x12468
[fffffa80105a5640 OUTLOOK.EXE]
3858.00385c fffffa801133ab00 fffd3691 Blocked ModuleA+0x12468
[fffffa8011998060 explorer.exe]
3d70.004a0c fffffa80139ddb00 fffd0482 Blocked ModuleA+0x12468
[fffffa8010ff5850 OUTLOOK.EXE]
3540.000458 fffffa8011052b00 fffbd007 Blocked ModuleA+0x12468
[fffffa8011d3d060 OUTLOOK.EXE]
49f8.0049fc fffffa8011c78060 fffdbbf9 Blocked ModuleA+0x12468
[fffffa801241b060 OUTLOOK.EXE]
4888.005af0 fffffa8012e8eab0 fffae442 Blocked ModuleA+0x12468
4888.003d24 fffffa800eca7b00 fffae443 Blocked ModuleA+0x12468
[fffffa8012687b30 explorer.exe]
5048.0051fc fffffa801129cb00 fffca8bf Blocked ModuleA+0x12468
[fffffa8011c1e060 OUTLOOK.EXE]
52c4.00117c fffffa80130f8710 fffaa157 Blocked ModuleA+0x12468
52c4.0045fc fffffa801374f060 fffaa15e Blocked ModuleA+0x12468
[fffffa8011c42b30 explorer.exe]
5898.0001ec fffffa80137a1b00 fffd8da0 Blocked ModuleA+0x12468
[fffffa8012e04b30 OUTLOOK.EXE]
5a74.004954 fffffa8012e05060 fffa9ff8 Blocked ModuleA+0x12468
[fffffa8010908b30 spoolsv.exe]
2724.004190 fffffa8011ea1060 fffdcafb Blocked ModuleA+0x12468
[fffffa801206eb30 WerFault.exe]
3e50.005424 fffffa8013c5eb00 fffdcf39 Blocked ModuleA+0x12468
[fffffa800f8cf2a0 WerFault.exe]
9f4.00570c fffffa8013c8ab00 fffdca9f Blocked ModuleA+0x12468
[fffffa8013af1060 WerFault.exe]
3c74.002b80 fffffa8013c5c060 fffd9dc8 Blocked ModuleA+0x12468
[fffffa800f8053a0 WINWORD.EXE]
3dd0.0066a8 fffffa800ce618c0 fffd7c02 Blocked ModuleA+0x12468
[fffffa8010b66b30 WINWORD.EXE]
62a4.001934 fffffa801368c430 fffd7ce7 Blocked ModuleA+0x12468
[fffffa80141dc060 WerFault.exe]
17d0.0052e4 fffffa801347a060 fffd57b8 Blocked ModuleA+0x12468
[fffffa8012629760 WerFault.exe]
621c.005b64 fffffa8011e395d0 fffc8dc2 Blocked ModuleA+0x12468
[fffffa80131a75d0 explorer.exe]
4884.002b34 fffffa8013dc3b00 fffd67bc Blocked ModuleA+0x12468
[...]
Threads Processed: 5948
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -