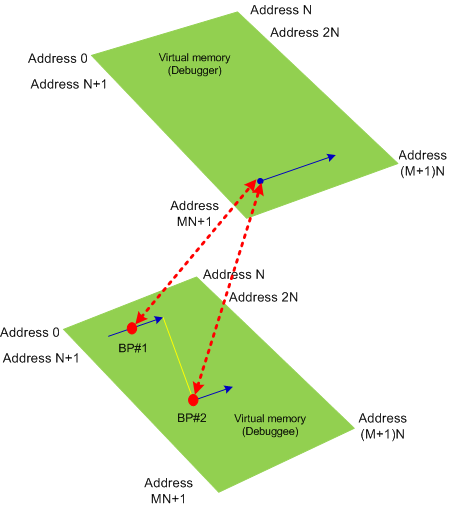
This is the first case study here that shows an interplay of memory dump analysis (DA) and software trace analysis (TA) patterns, what I call DATA analysis patterns (or DA+TA).
It was reported that one process was blocking vital server functionality. After the process restart the problem was gone away. A complete memory dump was saved on the next occurrence and it revealed critical section wait chains in that process but no critical section deadlocks:
0: kd> .process /r /p 87f76020
Implicit process is now 87f76020
Loading User Symbols
[...]
0: kd> !cs -l -o -s
-----------------------------------------
DebugInfo = 0x0016c6d8
Critical section = 0×0032be30 (+0×32BE30)
LOCKED
LockCount = 0×34
WaiterWoken = No
OwningThread = 0×00001c64
RecursionCount = 0×1
LockSemaphore = 0×624
SpinCount = 0×00000000
OwningThread = .thread 86396db0
ntdll!RtlpStackTraceDataBase is NULL. Probably the stack traces are not enabled.
[…]
The thread 86396db0 (TID 1c64) that blocked more than 50 threads (0×34) was blocked itself sleeping for more than 6 seconds:
0: kd> .thread 86396db0
Implicit thread is now 86396db0
0: kd> kL 100
*** Stack trace for last set context - .thread/.cxr resets it
ChildEBP RetAddr
ae7f8c98 8083d5b1 nt!KiSwapContext+0x26
ae7f8cc4 8083cf69 nt!KiSwapThread+0x2e5
ae7f8d0c 8092b03f nt!KeDelayExecutionThread+0x2ab
ae7f8d54 80833bef nt!NtDelayExecution+0x84
ae7f8d54 7c82860c nt!KiFastCallEntry+0xfc
1020e8ac 7c826f69 ntdll!KiFastSystemCallRet
1020e8b0 77e41ed5 ntdll!NtDelayExecution+0xc
1020e918 77e424fd kernel32!SleepEx+0x68
1020e928 67739357 kernel32!Sleep+0xf
1020e944 6773c3a2 ComponentA!DB_Driver_Command+0xa7
[…]
1020ec64 67485393 ComponentB!DatabaseSearch+0×34
[…]
1020ffb8 77e6482f msvcrt!_endthreadex+0xa3
1020ffec 00000000 kernel32!BaseThreadStart+0×34
0: kd> kv
*** Stack trace for last set context - .thread/.cxr resets it
ChildEBP RetAddr Args to Child
[...]
1020e918 77e424fd 00001b00 00000000 1020e944 kernel32!SleepEx+0x68 (FPO: [SEH])
1020e928 67739357 00001b00 00000000 0032ac6c kernel32!Sleep+0xf (FPO: [1,0,0])
[…]
0: kd> ? 1b00 / 0n1000
Evaluate expression: 6 = 00000006
Critical section it owns shows high contention count too:
0: kd> dt -r1 _RTL_CRITICAL_SECTION 0x0032be30
ProcessA!_RTL_CRITICAL_SECTION
+0x000 DebugInfo : 0x0016c6d8 _RTL_CRITICAL_SECTION_DEBUG
+0x000 Type : 0
+0x002 CreatorBackTraceIndex : 0
+0x004 CriticalSection : 0x0032be30 _RTL_CRITICAL_SECTION
+0x008 ProcessLocksList : _LIST_ENTRY [ 0x16c708 - 0x16c6b8 ]
+0x010 EntryCount : 0
+0×014 ContentionCount : 0xac352
+0×018 Spare : [2] 0×43005c
+0×004 LockCount : -210
+0×008 RecursionCount : 1
+0×00c OwningThread : 0×00001c64
+0×010 LockSemaphore : 0×00000624
+0×014 SpinCount : 0
Fortunately, that process had ETW tracing capability and its software trace recorded before the complete memory dump was saved the following recurrent periodic errorfrom different threads that confirms our observation about the possible problem with a database and explains thread delays we see (> 6 seconds for Sleep):
# PID TID Time Message
[...]
1972 2780 5992 10:05:11.005 Error: [DB Driver] Not enough space on temp disk
1973 2780 5992 10:05:11.005 Execute DB command sleeps on error (retry 26)
[...]
4513 2780 3292 10:06:02.942 Error: [DB Driver] Not enough space on temp disk
4514 2780 3292 10:06:02.942 Execute DB command sleeps on error (retry 11)
4515 2780 3292 10:06:09.598 Error: [DB Driver] Not enough space on temp disk
4516 2780 3292 10:06:09.598 Execute DB command sleeps on error (retry 12)
[…]
- Dmitry Vostokov @ DumpAnalysis.org -