Debugging the Debugger (16-bit)
After checking that Vista still has old MS-DOS real mode 16-bit debug.exe with commands similar to WinDbg ones I tried to debug notepad.exe:
C:\Users\user>debug
-?
assemble A [address]
compare C range address
dump D [range]
enter E address [list]
fill F range list
go G [=address] [addresses]
hex H value1 value2
input I port
load L [address] [drive] [firstsector] [number]
move M range address
name N [pathname] [arglist]
output O port byte
proceed P [=address] [number]
quit Q
register R [register]
search S range list
trace T [=address] [value]
unassemble U [range]
write W [address] [drive] [firstsector] [number]
allocate expanded memory XA [#pages]
deallocate expanded memory XD [handle]
map expanded memory pages XM [Lpage] [Ppage] [handle]
display expanded memory status XS
As expected it debugs the MSDOS (MZ) portion of notepad.exe:
C:\Users\user>debug c:\windows\system32\notepad.exe
-u
17DB:0000 0E PUSH CS
17DB:0001 1F POP DS
17DB:0002 BA0E00 MOV DX,000E
17DB:0005 B409 MOV AH,09
17DB:0007 CD21 INT 21
17DB:0009 B8014C MOV AX,4C01
17DB:000C CD21 INT 21
17DB:000E 54 PUSH SP
17DB:000F 68 DB 68
17DB:0010 69 DB 69
17DB:0011 7320 JNB 0033
17DB:0013 7072 JO 0087
17DB:0015 6F DB 6F
17DB:0016 67 DB 67
17DB:0017 7261 JB 007A
17DB:0019 6D DB 6D
17DB:001A 206361 AND [BP+DI+61],AH
17DB:001D 6E DB 6E
17DB:001E 6E DB 6E
17DB:001F 6F DB 6F
-t
AX=0000 BX=FFFF CX=FE00 DX=0000 SP=00B6 BP=0000 SI=0000 DI=0000
DS=17CB ES=17CB SS=17DB CS=17DB IP=0001 NV UP EI PL NZ NA PO NC
17DB:0001 1F POP DS
-t
AX=0000 BX=FFFF CX=FE00 DX=0000 SP=00B8 BP=0000 SI=0000 DI=0000
DS=17DB ES=17CB SS=17DB CS=17DB IP=0002 NV UP EI PL NZ NA PO NC
17DB:0002 BA0E00 MOV DX,000E
-t
AX=0000 BX=FFFF CX=FE00 DX=000E SP=00B8 BP=0000 SI=0000 DI=0000
DS=17DB ES=17CB SS=17DB CS=17DB IP=0005 NV UP EI PL NZ NA PO NC
17DB:0005 B409 MOV AH,09
-g
This program cannot be run in DOS mode.
Program terminated normally
-
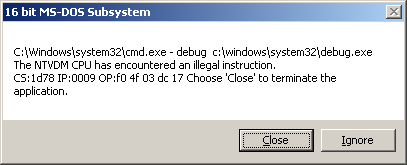
So I was looking for a real MSDOS program to debug and thought that debug.exe would be a natural choice. Unfortunately there was an illegal instruction during double debugging:
C:\Users\user>debug c:\windows\system32\debug.exe
-g
-g
So it looks like WinDbg double debugging is much more robust despite the bigger file size (debug.exe is only 21KB).
- Dmitry Vostokov @ DumpAnalysis.org + TraceAnalysis.org -